Lassen Sie uns Ihre E-Mails optimieren
Sie erhalten die Kontrolle über Ihre E-Mails
 |
 |
 |
 |
 |
 |
Ignoriert |
Gelesen |
|
|---|---|---|
 |
 |
 |
E-Mails versenden, ohne sich um die Authentifizierung kümmern zu müssen
Digital signierte E-Mail-Nachrichten: SPF, DKIM und sichere E-Mail-Authentifizierung
IP-Adressen sind für den Versand von E-Mails wichtig
Wechseln Sie sicher von Ihrem aktuellen Mailserver zu RealSender

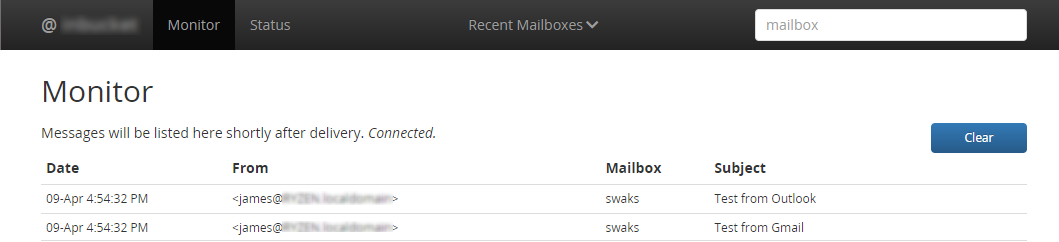
Versenden Sie E-Mails, ohne sich um die Benutzerauthentifizierung kümmern zu müssen.
Wir stellen Ihnen einen offenen Port zur Verfügung, über den Sie Daten übertragen können:
Dabei wird lediglich die IP-Adresse Ihrer Verbindung überprüft.
Geben Sie einfach unter
an, von welchen IP-Adressen aus Sie sich verbinden,
und schon können Sie Ihre E-Mails versenden.
Um sich vor E-Mail-Missbrauch zu schützen,überprüfen immer mehr E-Mail-Server
die Identität des Absenders, bevor sie die Nachricht zustellen.
Wenn Sie E-Mails ohne RealSender versenden, können Ihre Empfänger nicht sicher sein,
dass die empfangene Nachricht tatsächlich von Ihnen stammt.
Wenn Sie E-Mails mit RealSender versenden, werden alle Nachrichten, die Sie
senden,
digital signiert, sodass die Empfänger ihnen vertrauen können.
Es gibt zwei Standards zur Überprüfung der Absenderidentität: SPF und DKIM.
RealSender bietet beide an:

Die „Internetprotokolladresse“ oder „IP-Adresse“
ist vergleichbar mit einer Telefonnummer Ihres Festnetzanschlusses oder Mobiltelefons.
Es handelt sich um personenbezogene Daten, die automatisch
von einem anderen Computer erfasst werden, sobald eine Verbindung über das Internet hergestellt wird.
Kein anderes Gerät im Internet hat dieselbe IP-Adresse.
Dies ist notwendig, damit ein Gerät mit einem anderen kommunizieren kann.
„Dedizierte“ IP-Adressen sind für den Versand von E-Mails
wichtig,
da ihre Reputation einen entscheidenden Einfluss darauf hat, ob die E-Mails angenommen werden oder nicht.
Die Verwendung „gemeinsam genutzter“ IP-Adressen für die geschäftliche Kommunikation
ist so, als würde man jedes Mal einen anderen Vertriebsmitarbeiter zum selben Kunden schicken.
Da der Empfänger ihn nicht kennt, wird er ihm mit Misstrauen begegnen.
In extremen Fällen, wenn derselbe Verkäufer jeden Tag andere Produkte anbietet,
ist es sehr wahrscheinlich, dass er beim nächsten Mal, wenn er an die Tür klopft, nicht mehr willkommen ist.
Die meisten SMTP-Dienste im Internet stellen ihren Kunden „gemeinsam genutzte“ IP-Adressen zur Verfügung.
Jedes Mal, wenn Sie eine E-Mail versenden, wird eine andere IP-Adresse zugewiesen.
Ähnliches gilt für Cloud-Hosting-Anbieter, die ihre Dienste auf Minutenbasis anbieten.
In diesem Fall vergeben sie eine oder mehrere „vorübergehend zugewiesene“ IP-Adressen.
Seit seiner Gründung im Jahr 2009 hat sich RealSender dazu entschlossen, ausschließlich SMTP-Server mit „dedizierten“ IP-Adressen anzubieten.
Das bedeutet, dass jeder Kunde eine IP-Adresse erhält, die sich im Laufe der Zeit nicht ändert.
Durch die Verknüpfung mit dem Unternehmensdomainnamen mittels E-Mail-Authentifizierung gewinnen beide an Glaubwürdigkeit.
Wenn Ihre Mitteilungen konsistent sind und den Erwartungen entsprechen,
werden sie nach und nach von den Empfängern wahrgenommen, die ihnen eine höhere Reputation zuerkennen.
Dieses Vertrauen kann ein hohes Niveau erreichen, sodass alle von Ihnen gesendeten Mitteilungen
automatisch akzeptiert und als „Wichtig“ oder „Hohe Priorität“ eingestuft werden.
Wechseln Sie von Ihrem derzeitigen Mailserver zur sicheren Umgebung von RealSender.
Sie können dieselben Anmeldedaten
sowie den SMTP-Hostnamen verwenden, sofern dieser unter Ihrer Domain liegt.
Sie können E-Mails sicher versenden, auch ohne Authentifizierung.
Themen in diesem Bereich:
Nur die angegebenen Absender dürfen passieren
Unberechtigte Zugriffe werden erkannt, blockiert und nach drei fehlgeschlagenen Versuchen gesperrt
optionale zusätzliche Sicherheitskonfigurationen
Jedem Kunden wird ein eigener RealSender-SMTP-Server zugewiesen.
Nur so lässt sich die Reputation des Servers kontrollieren
und die Reputation der Absenderdomains täglich überprüfen.
Bei diesem Ansatz erhalten nur die registrierten Absender die Erlaubnis, die Nachricht zu versenden.
Das System überprüft jede Nachricht und akzeptiert oder lehnt sie auf Grundlage der Liste der zugelassenen Absender ab.
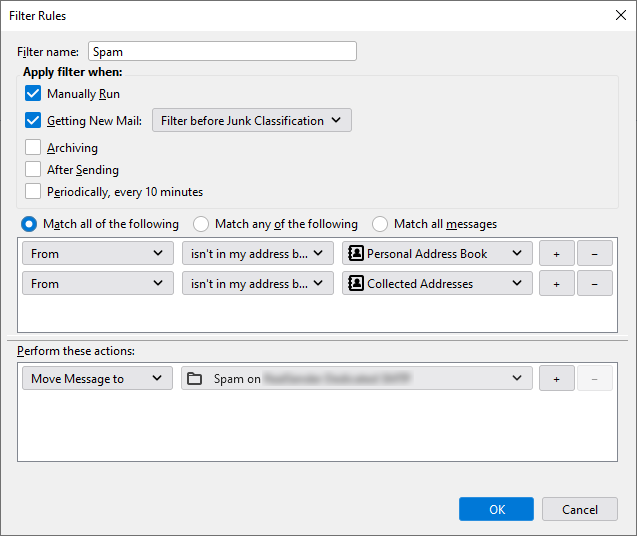
Die „autorisierten Absender“ für jedes RealSender-Konto
müssen sich auf einen oder mehrere Domainnamen beziehen, die von demselben Unternehmen registriert wurden.
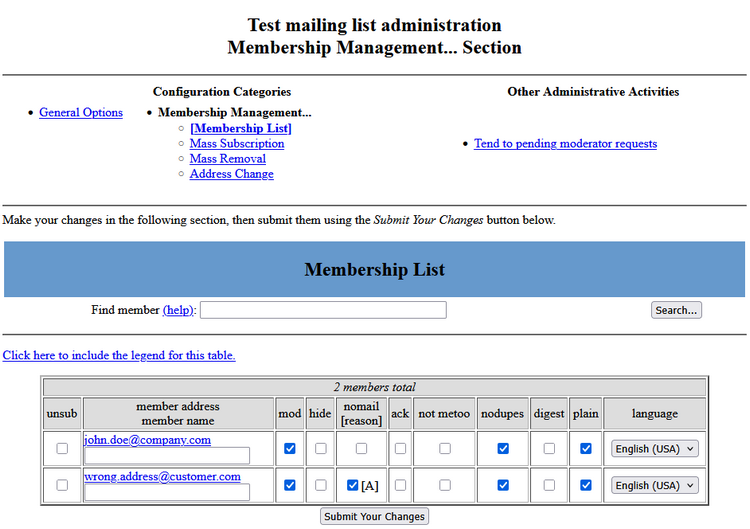
RealSender-Partner und große Organisationen können die Liste der autorisierten Absender unter
selbstständig aktualisieren.

RealSender nutzt die Serveranwendung Fail2ban, um Ihren dedizierten SMTP-Server zu sichern.
Dies schützt vor unbefugtem Zugriff und DOS-Angriffen (Denial-of-Service).
Nach drei fehlgeschlagenen Versuchen wird die Quell-IP gesperrt und gesperrt.
Mögliche Gründe für die Aufnahme in die schwarze Liste könnten sein:
Anmeldeversuch mit falschen Anmeldedaten
(falscher Benutzername oder falsches Passwort)
Authentifizierungsversuch über ungesicherte Kanäle
(das System erfordert eine TLS/SSL-Authentifizierung)
Die E-Mail-Adresse des Absenders ist nicht zum Versand von
berechtigt
(siehe Einschränkungen für von RealSender autorisierte Absender)
SMTP-Verbindung während des Authentifizierungsprozesses unterbrochen
(Mehrere unterbrochene Verbindungen führen dazu, dass der SMTP-Dienst für berechtigte Benutzer nicht verfügbar ist)
Die Sperre hat zur Folge, dass der SMTP-Server nicht mehr auf Verbindungsversuche reagiert,
und der Computer, der die Anfrage stellt, folgende Meldung erhält:
Verbindung zu der Adresse 93.184.216.34 herstellen: Verbindung abgelehntSo gehen Sie mit versehentlich gesperrten IP-Adressen um:
26.08.2024 01:38:01,199 fail2ban.filter [19671]: INFO [smtp] 93.184.216.34 gefunden – 26.08.2024 01:38:00
26.08.2024 01:38:01,201 fail2ban.filter [19671]: INFO [smtp] 93.184.216.34 gefunden – 26.08.2024 01:38:01
26.08.2024 01:38:01,404 fail2ban.filter [19671]: INFO [smtp] 93.184.216.34 gefunden – 26.08.2024 01:38:01
26.08.2024 01:38:01,972 fail2ban.actions [19671]: HINWEIS [smtp] Sperre für 93.184.216.3423.08.2024 07:00:12,501 fail2ban.filter [30057]: INFO [smtp] 93.184.216.34 nach IP ignorieren
23.08.2024 07:00:12,501 fail2ban.filter [30057]: INFO [smtp] 93.184.216.34 nach IP ignorieren
23.08.2024 07:00:13,115 fail2ban.filter [30057]: INFO [smtp] 93.184.216.34 nach IP ignorieren
Themen in diesem Bereich:
Sicherheitsoption zum Blockieren aller E-Mails, die potenziell schädliche Anhänge enthalten
Sicherheitsoption zur Begrenzung der Anzahl der von einem Absender gesendeten Nachrichten
Sicherheitsoption zum Blockieren aller E-Mails, die das Gewichtslimit überschreiten
Sicherheitsoption zur Umwandlung großer Dateianhänge in Links
alle gesendeten E-Mails transparent als BCC versenden

Die Option „Schädliche Anhänge blockieren“ blockiert alle potenziell schädlichen Anhänge
mit Ausnahme einiger sicherer Dateiformate, die Sie festlegen können, wie z. B.: pdf, txt, gif, jpg und png.
Das Versenden von E-Mails mit nicht autorisierten Anhängen wird unterbunden.
Die Nachricht wird nicht über den SMTP-Server
weitergeleitet;
die E-Mail wird mit folgender Warnung an den Absender zurückgeschickt:
Der Anhang mit dem Namen „example.zip“
verstößt gegen die E-Mail-Sicherheitsrichtlinien Ihres Unternehmens.
Die Zustellung wurde blockiert.
Weitere Informationen erhalten Sie von Ihrem IT-Administrator.
Inspiriert durch einen Kommentar von Phil Pennock in der SAGE-Mailingliste:
Ich wünschte wirklich, ich könnte die Anzahl der E-Mails pro Kunde und Tag begrenzen,
wobei diese Obergrenze angehoben werden könnte, wenn ein Kunde berechtigte Gründe für den Versand von E-Mails hat …Hohe E-Mail-Volumen werden oft durch ein gehacktes Konto verursacht.
Dies kann dem Ruf Ihres Unternehmens und dem Ihres Mail-Servers schaden.
Mit der Option „Anzahl der Nachrichten begrenzen“ können Sie eine maximale Anzahl von E-Mails pro Tag und Absender festlegen,
sodass überschüssige E-Mails blockiert werden, bevor sie ins Internet gelangen.
Der Versand von Nachrichten mit „übermäßiger Menge“ wird unterbunden.
Die E-Mails werden sofort an den Absender zurückgeschickt, zusammen mit einer Warnung wie:
An error occurred when sending email. The mail server answered:
450 4.7.1 <>... sender@example.com has exceeded n messages per 1 day.Als Maßnahme gegen Spam haben die meisten SMTP-Server eine Option eingeführt, mit der die Anzahl der Empfänger
begrenzt werden kann, die für einen bestimmten Umschlag angegeben werden können. In Sendmail heißt diese Option „MaxRecipientsPerMessage“.
RealSender empfiehlt, die Anzahl der Empfänger pro Nachricht zu begrenzen (
),
um Missbrauch einzudämmen und das Risiko zu vermeiden, dass zu viele Adressen in CC oder BCC gesetzt werden.
Wir stellen eine Liste mit 300 @bogusemail.net-Adressen zum Testen zur Verfügung:
bogusemail-test.txt
Die Nachrichten gelangen an einen „Black-Hole“-Mailserver.
Sie können diese nach Belieben nutzen:
um zu überprüfen, an wie viele Empfänger pro Nachricht
Ihr SMTP-Server den Versand zulässt.
Wenn Sie jemandem einen großen Anhang senden,
kommt dieser möglicherweise nicht an, da die zulässige Größe für eingehende Anhänge bei diesem Empfänger geringer sein könnte.
Mit der Option „Nachrichtengröße begrenzen“ können Sie eine maximale Nachrichtengröße festlegen
,
sodass diese bereits vor dem Hochladen blockiert werden.
Das Versenden von Anhängen, die zu groß sind, wird unterbunden,
die E-Mail wird sofort an den Absender zurückgeschickt,
mit einer Warnung wie:
Die Nachricht, die Sie senden möchten, überschreitet
die globale Größenbeschränkung des Servers von (xxxx Byte).
Verringern Sie die Größe der Nachricht und versuchen Sie es erneut.Alternativ können große Anhänge online unter
in Ihrem Webspace veröffentlicht und über einen einfachen, kompakten Link geteilt werden.
Die E-Mail mit dem Link zum Benutzerbereich enthält folgende Anweisungen:
Link zu Ihrem Webspace: (/Temporäre Inhalte werden nach 7 Tagen gelöscht)
https://username:secretcode@rsXXX.realsender.com/view/
(Kopieren Sie den Link und fügen Sie ihn hier ein: https://webspace.realsender.com)
Beispiel: https://rsXXX.realsender.com/view/example.mp4 (101 MB)
Die App „filelink“ von RealSender wandelt automatisch
alle Anhänge, die größer sind als die von Ihnen festgelegte Größe
in einen Link um, etwa so:
[Beispiel für eine große Datei.pdf] (43,96 MB) wurde verschoben nach:
http://rsXXX-realsender.com/files/e1eb3665a1a0766ea65616b6210cfd538c4950f8.pdf
Die Datei wird nach zwölf Monaten GELÖSCHT.Der Empfänger erhält eine kurze Nachricht.
Er kann den Anhang herunterladen, wenn er ihn benötigt.
Die Domain im Link kann eine beliebige eigene Domain oder Subdomain sein, die Sie verwenden möchten.

E-Mails sind der wichtigste Kanal der modernen Geschäftskommunikation.
Ihr versehentlicher Verlust würde der Wissensbasis des Unternehmens großen Schaden zufügen.
Darüber hinaus sollte Geschäftskorrespondenz in der Regel bis zu zehn Jahre lang aufbewahrt werden.
!! Wenn Ihr Unternehmen persönliche E-Mail-Adressen verwendet,
wie z. B. name.surname@companyname.com,
müssen Sie die Absender vor der Aktivierung dieser Funktion darüber informiert habenMithilfe der BCC-Funktion (Blind Carbon Copy) überträgt
RealSender alle gesendeten E-Mails transparent
an ein spezielles POP3-Postfach
das so konfiguriert ist, dass es innerhalb kurzer Zeit große Mengen an E-Mails empfangen kann
Sie können diese automatisch über externe Dienste abrufen
!!! Gespeicherte E-Mail-Nachrichten werden nach 7 Tagen automatisch gelöscht !!!
zum Beispiel mithilfe der Einstellung„E-Mails von anderen Konten abrufen“
verfügbar in Gmail, sowohl in der Einzelversion (kostenlos) als auch in der G Suite-App-Version
an eine andere E-Mail-Adresse
richtig konfiguriert, damit die Nachrichten nicht als Spam eingestuft werden
Die Gmail G Suite-App bietet die Option„Eingehende E-Mail-Gateways einrichten“

Themen in diesem Bereich:
Beispiele für die Konfiguration von E-Mail-Clients: Outlook – Outlook 2007 – Outlook 2013, 2016 – Mac OS X Mail – Thunderbird – Zimbra Desktop
Beispiele für die Konfiguration von E-Mail-Servern: Microsoft Exchange Server – Microsoft Office 365 – Zimbra Collaboration
ein einsatzbereiter E-Mail-Server, der alle an die autorisierte Domain gesendeten Nachrichten empfängt
ein Spamfilter, der auf E-Mail-Authentifizierung und autorisierten Absendern basiert
So starten Sie mit RealSender:
Wir signieren E-Mails automatisch mit DKIM, sodass Sie nichts weiter tun müssen.
Haben Sie Fragen? Kontaktieren Sie uns!


Extras > Optionen > Konten
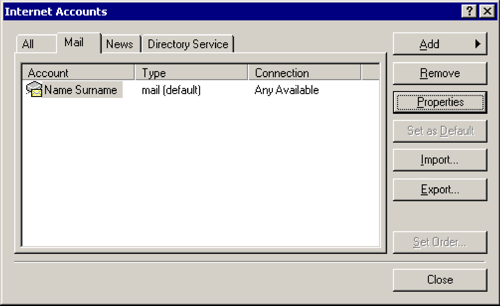
E-Mail > [Eigenschaften]
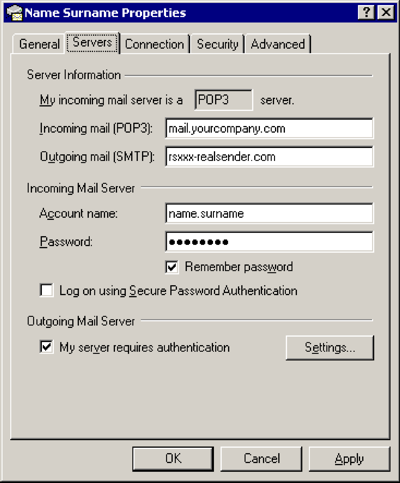
Server
Ausgehende E-Mails (SMTP): rsxxx.realsender.com
Postausgangsserver
[x] Mein Server erfordert eine Authentifizierung
[Einstellungen…]
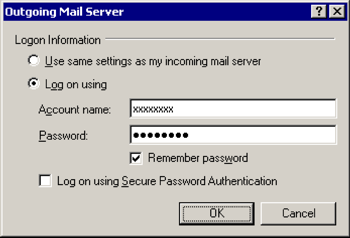
Postausgangsserver
[x] Melden Sie sich an mit
Kontoname: (der, den wir Ihnen geschickt haben)
Passwort: (das, das wir Ihnen geschickt haben)[x] Passwort speichern
[OK]

Erweitert
Ausgehende E-Mails (SMTP): 25
[x] Dieser Server erfordert eine sichere Verbindung (SSL)
[OK]

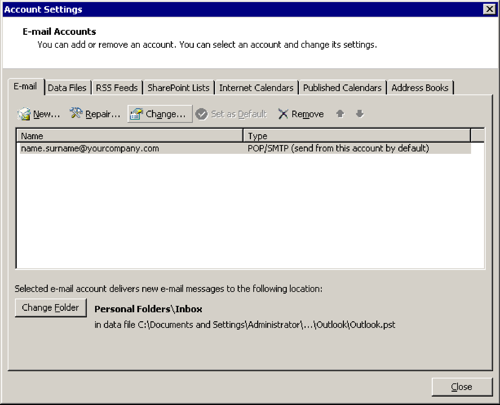
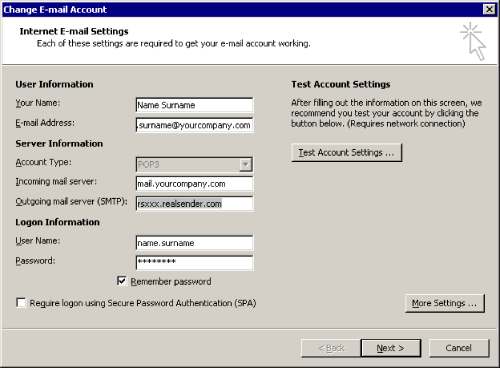
Extras > Optionen…
E-Mail-Einstellungen > [E-Mail-Konten…]
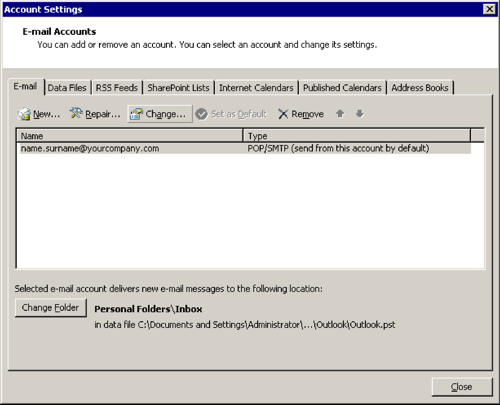
[Ändern…]
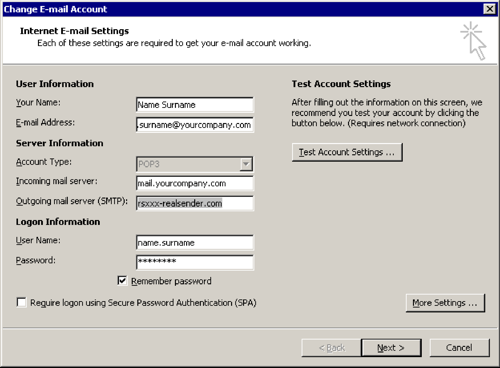
E-Mail-Konto ändern
Postausgangsserver (SMTP): rsxxx.realsender.com
[Weitere Einstellungen…]
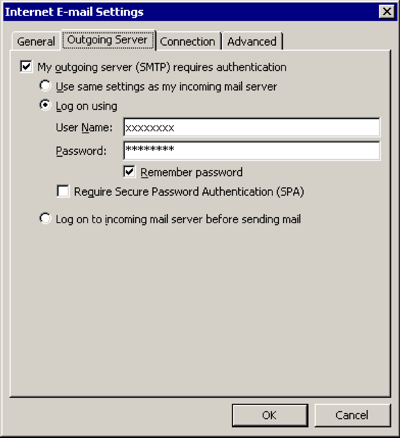
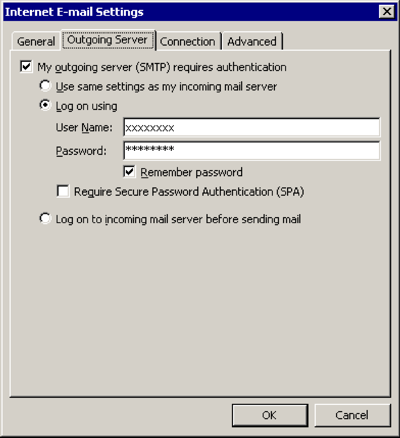
Postausgangsserver
[x] Mein Postausgangsserver (SMTP) erfordert eine Authentifizierung
[x] Melden Sie sich an mit
Benutzername: (den wir Ihnen zugesandt haben)
Passwort: (das wir Ihnen zugesandt haben)[x] Passwort speichern
[OK]
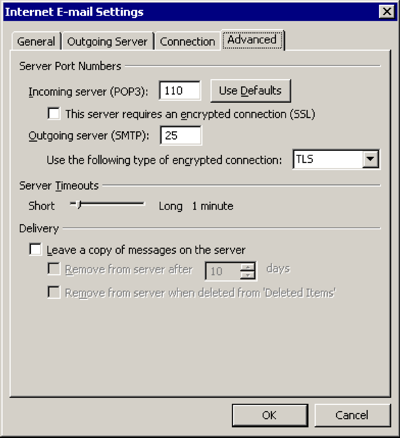
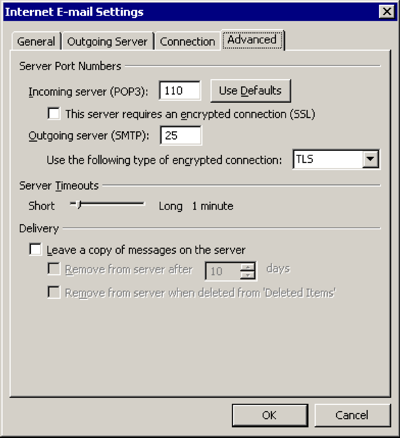
Erweitert
Verwenden Sie die folgende Art von verschlüsselter Verbindung: TLS
[OK]

Datei > [Info]

[Konto- und Social-Media-Einstellungen]
[Kontoeinstellungen…]
[Ändern…]
E-Mail-Konto ändern
Postausgangsserver (SMTP): rsxxx.realsender.com
[Weitere Einstellungen…]
Postausgangsserver
[x] Mein Postausgangsserver (SMTP) erfordert eine Authentifizierung
[x] Melden Sie sich an mit
Benutzername: (den wir Ihnen zugesandt haben)
Passwort: (das wir Ihnen zugesandt haben)[x] Passwort speichern
[OK]
Erweitert
Verwenden Sie die folgende Art von verschlüsselter Verbindung: TLS
[OK]

Mail > Einstellungen… > Server-Einstellungen
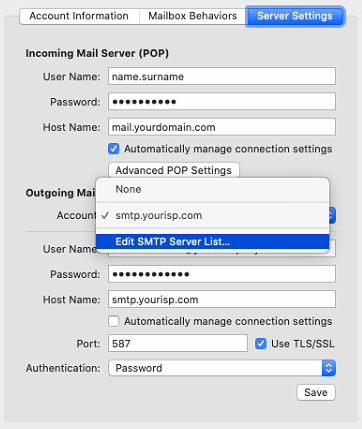
Postausgangsserver (SMTP) > SMTP-Serverliste bearbeiten …
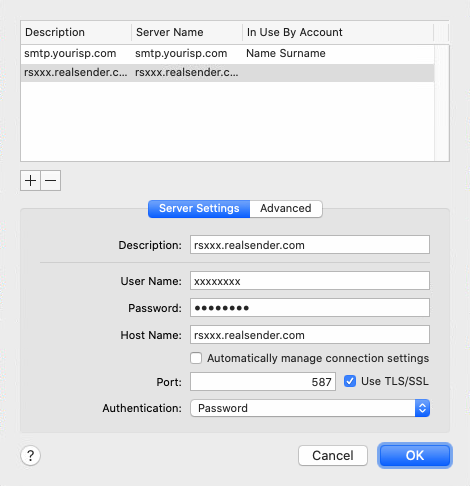
[+] Konto erstellen
Beschreibung: rsxxx.realsender.com
Benutzername: (den wir Ihnen zugesandt haben)
Passwort: (das wir Ihnen zugesandt haben)
Hostname: rsxxx.realsender.com
[ ] Kontoeinstellungen automatisch erkennen und beibehalten
Port: 587 [x] TLS/SSL verwenden
Authentifizierung: Passwort
[OK]
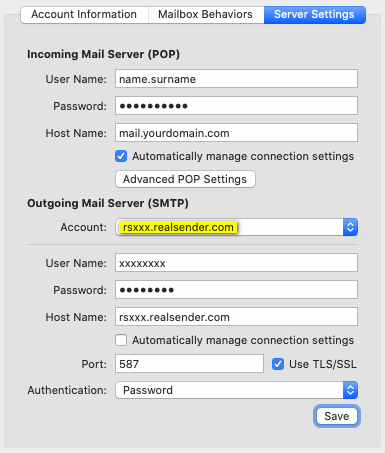
Postausgangsserver (SMTP)
Konto: rsxxx.realsender.com
[Speichern]

Extras > Kontoeinstellungen
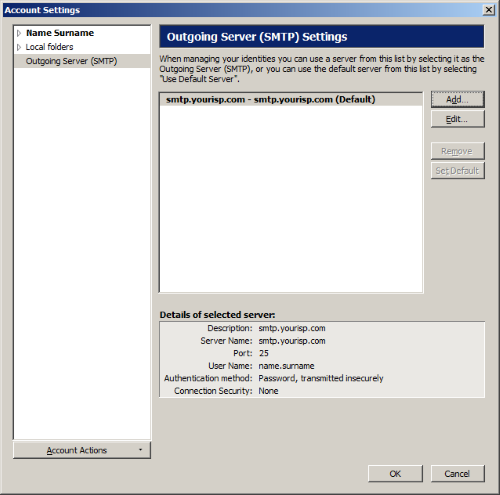
Postausgangsserver (SMTP) > [Hinzufügen…]
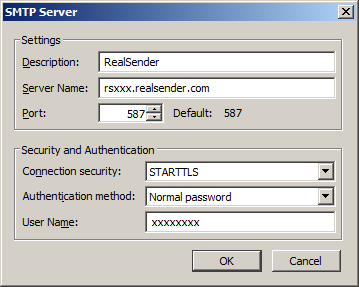
Einstellungen
Beschreibung: RealSender
Servername: rsxxx.realsender.com
Port: 587
Sicherheit und Authentifizierung
Verbindungssicherheit: STARTTLS
Authentifizierungsmethode: Normales Passwort
Benutzername: (der, den wir Ihnen zugesandt haben)
[OK]
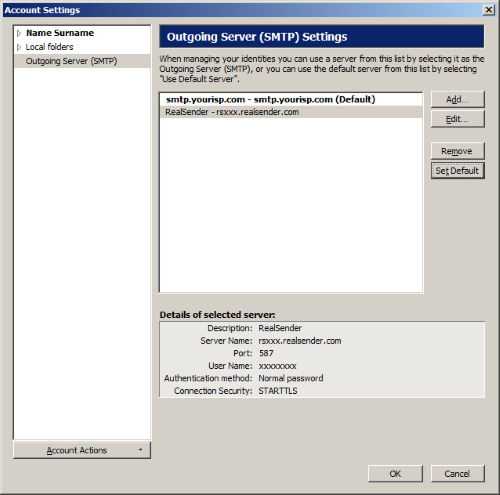
RealSender > [Als Standard festlegen]
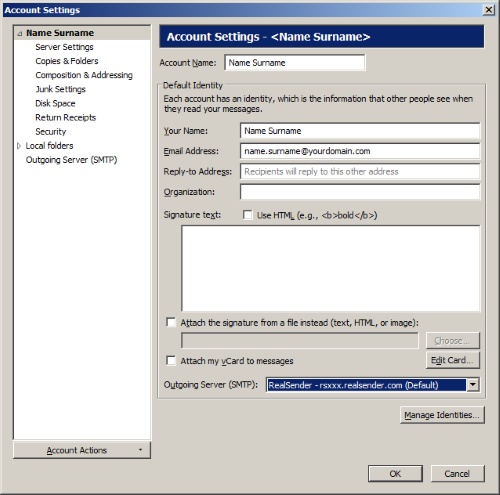
Kontoeinstellungen
(Wählen Sie Ihr E-Mail-Konto in der Baumstruktur auf der linken Seite aus)
Postausgangsserver (SMTP): RealSender
[OK]
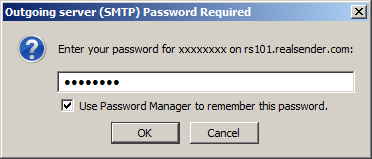
Wenn du zum ersten Mal eine Nachricht sendest
Passwort für den Postausgangsserver (SMTP) erforderlich
Geben Sie Ihr Passwort ein für…: (das, das wir Ihnen geschickt haben)
[x] Dieses Passwort mit dem Passwort-Manager speichern
[OK]

Desktop starten > Einstellungen (oben rechts)
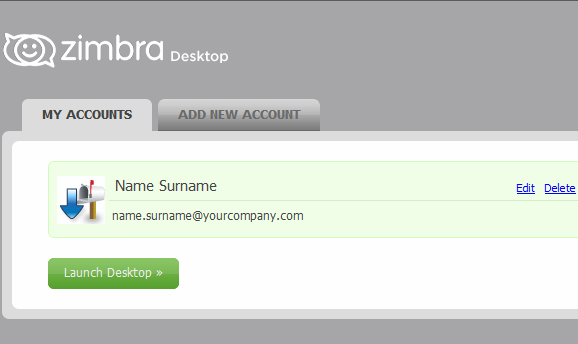
MEINE KONTEN > [Bearbeiten]
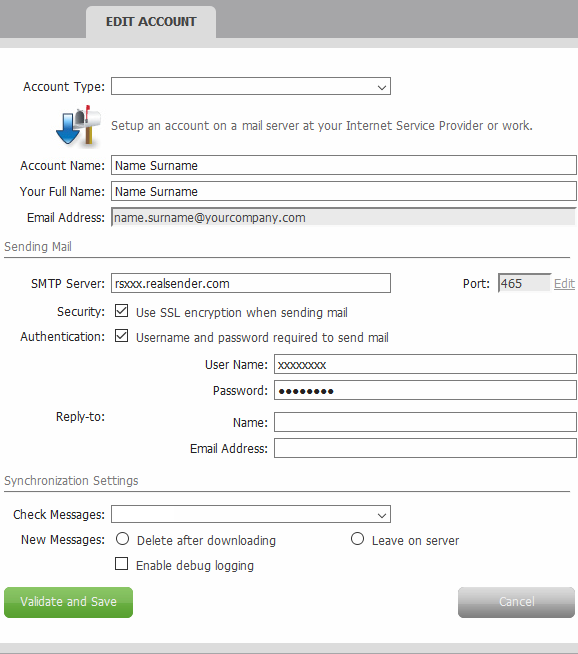
KONTO BEARBEITEN
E-Mails versenden
SMTP-Server: rsxxx.realsender.com
Sicherheit: [x] Beim Versenden von E-Mails SSL-Verschlüsselung verwenden
Authentifizierung: [x] Benutzername und Passwort zum Versenden von E-Mails erforderlich
Benutzername: (den wir Ihnen geschickt haben)
Passwort: (das, das wir Ihnen geschickt haben)
[Überprüfen und speichern]
So starten Sie mit RealSender:
Wir signieren E-Mails automatisch mit DKIM, sodass Sie nichts weiter tun müssen.
Haben Sie Fragen? Kontaktieren Sie uns!

EAC
(Exchange Admin Center)

E-Mail-Fluss > Sende-Konnektoren
[+] Neuer Sende-Anschluss

neuer Sendeanschluss
*Name:
Typ:
[x] Internet (z. B. zum Versenden von E-Mails)
[Weiter]

Smart Host bearbeiten
Geben Sie einen vollqualifizierten Domänennamen (FQDN), eine IPv4-Adresse oder eine IPv6-Adresse an:
rsxxx.realsender.com
[Speichern]

neuer Sendeanschluss
*Netzwerkeinstellungen:
[x] E-Mails über Smart-Hosts leiten
(unverändert)
[Weiter]

Neuer Send-Konnektor – Authentifizierung
Intelligente Host-Authentifizierung:
[x] Basisauthentifizierung
[x] Basisauthentifizierung erst nach dem Start von TLS anbieten*Benutzername:
(den wir Ihnen geschickt haben)*Passwort:
(das, das wir Ihnen geschickt haben)
[Weiter]

Neuer Send-Anschluss – Routing
*Adressraum:
TYP: SMTP-
DOMAIN: *
KOSTEN: 1
[Weiter]

Neuer Sendekonnektor – welcher Exchange-Server
[BÖRSE]
[Hinzufügen ->] BÖRSE
[ok]

[Ende]

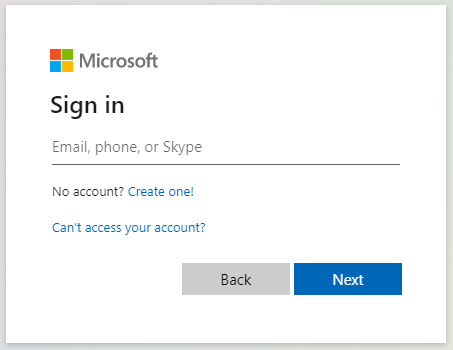
Microsoft Office 365-Verwaltungscenter

Menü links > Admin
Microsoft 365-Verwaltungscenter > … Alle anzeigen
Microsoft 365-Verwaltungscenter > Verwaltungscenter > Exchange
Exchange-Verwaltungscenter > E-Mail-Fluss > Konnektoren
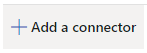
Konnektoren > Konnektor hinzufügen
Verbindung von: [x] Office 365
Verbindung zu: [x] Partnerorganisation[Weiter]
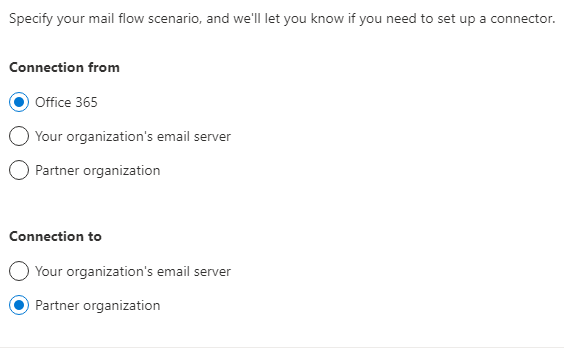
Dieser Connector wendet Routing- und Sicherheitsbeschränkungen für E-Mail-Nachrichten an, die
von Office 365 an Ihre Partnerorganisation oder Ihren Dienstanbieter gesendet werden.
Name: RealSender
Was möchten Sie tun, nachdem der Connector gespeichert wurde?
[x] Aktivieren[Weiter]
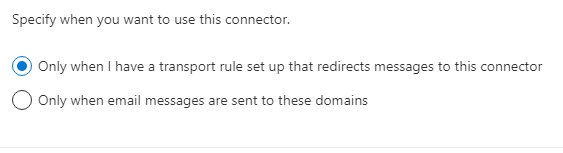
Geben Sie an, wann Sie diesen Konnektor verwenden möchten.
[x] Nur, wenn ich eine Transportregel eingerichtet habe, die Nachrichten an diesen Konnektor weiterleitet[Weiter]
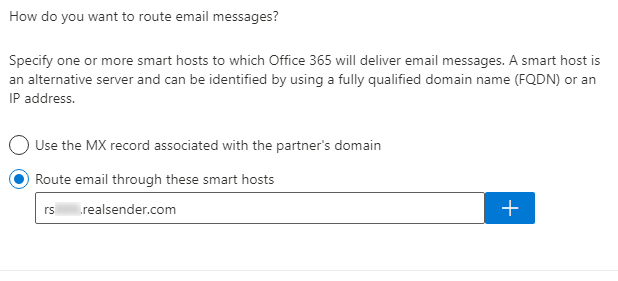
Wie möchten Sie E-Mail-Nachrichten weiterleiten?
Geben Sie einen oder mehrere Smart Hosts an, an die Office 365 E-Mail-Nachrichten zustellen soll.
Ein Smart Host ist ein alternativer Server und kann über einen vollqualifizierten Domänennamen (FQDN) oder eine IP-Adresse identifiziert werden.
[x] E-Mails über diesen Smart Host weiterleiten
rsxxx.realsender.com [+][Weiter]
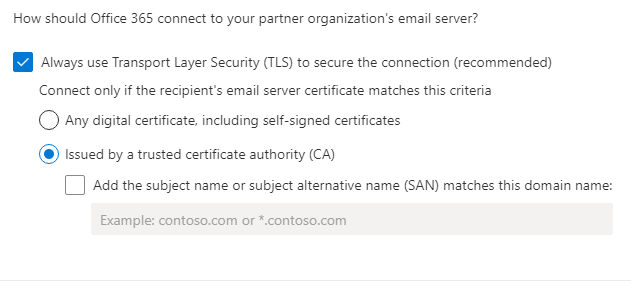
Wie soll Office 365 eine Verbindung zum E-Mail-Server Ihrer Partnerorganisation herstellen?
[x] Verwenden Sie immer Transport Layer Security (TLS), um die Verbindung zu sichern (empfohlen)
Stellen Sie nur dann eine Verbindung her, wenn das Zertifikat des E-Mail-Servers des Empfängers diesen Kriterien entspricht
[x] Ausgestellt von einer vertrauenswürdigen Zertifizierungsstelle (CA)[Weiter]
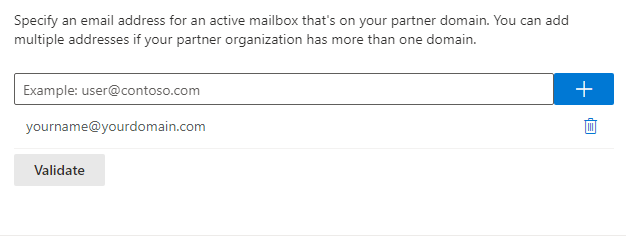
Geben Sie eine E-Mail-Adresse für ein aktives Postfach an, das sich in Ihrer Partnerdomain befindet.
Sie können mehrere Adressen hinzufügen, wenn Ihre Partnerorganisation über mehr als eine Domain verfügt.
yourname@yourdomain.com [+]
[Überprüfen]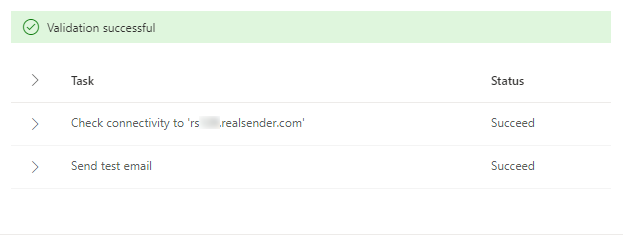
[Überprüfen]
Überprüfung läuft...
Überprüfung erfolgreich
> Aufgabe Status
> Verbindung zu „rsxxx.realsender.com“ prüfen Erfolgreich
> Test-E-Mail senden Erfolgreich[Weiter]
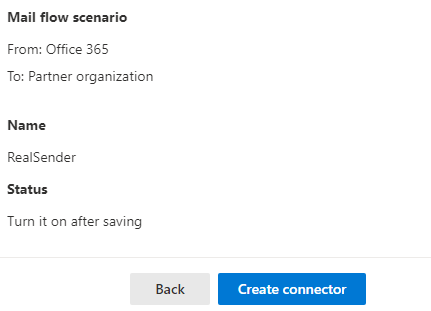
E-Mail-Fluss-Szenario
Von: Office 365
An: Partnerorganisation
Name
RealSender
Status
Nach dem Speichern aktivieren
Verwendung des Konnektors
Nur verwenden, wenn eine Transportregel eingerichtet ist, die Nachrichten an diesen Konnektor weiterleitet.
Routing
E-Mail-Nachrichten über diese Smart Hosts leiten: rsxxx.realsender.com
Sicherheitsbeschränkungen
Verwenden Sie immer Transport Layer Security (TLS) und stellen Sie nur dann eine Verbindung her, wenn das E-Mail-Serverzertifikat des Empfängers von einer vertrauenswürdigen Zertifizierungsstelle (CA) ausgestellt wurde.[Konnektor erstellen]

Zimbra Collaboration
(Netzwerkversion / Open Source)
> Admin-Konsole
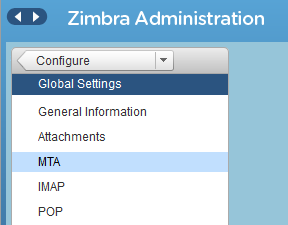
Zimbra-Verwaltung
> Konfigurieren
> Globale Einstellungen
> MTA
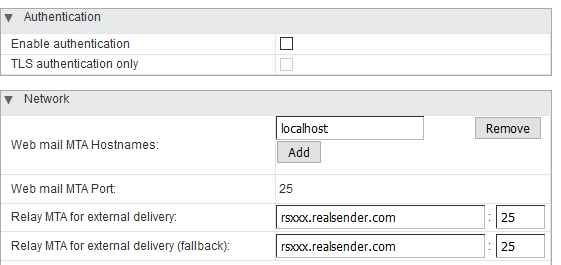
Authentifizierung
Authentifizierung aktivieren [ ]
Nur TLS-Authentifizierung [ ]
Netzwerk
Hostnamen des Webmail-MTA: localhost
Port des Webmail-MTA: 25Relay-MTA für die externe Zustellung: rsxxx.realsender.com : 25
Relay-MTA für die externe Zustellung (Fallback): rsxxx.realsender.com : 25

Die „inxbox“-App von RealSender ist ein sofort einsatzbereiter E-Mail-Server,
der alle an die autorisierte Domain gesendeten Nachrichten empfängt.
Er ist sofort betriebsbereit, sobald der MX-Eintrag auf ihn verweist.
Er wird oft als Notfall-Mailserver eingesetzt.
Sollte Ihr üblicher E-Mail-Dienst ausfallen,
nimmt inxbox alle an ihn gesendeten Nachrichten sofort entgegen.
Ohne dass eine spezielle Konfiguration erforderlich ist,
wie beispielsweise die Angabe einzelner Benutzer-E-Mail-Adressen.
Wenn „
“ als historisches E-Mail-Archiv konfiguriert ist,
speichert ein automatischer Prozess die Nachrichten
nach Empfänger, Monat und Jahr.
Hauptmerkmale:
zeichnet alle E-Mails transparent auf
ein sicherer Webbereich zum Online-Lesen von E-Mails im Posteingang
ein sofort einsatzbereites Postfach, das jede Nachricht empfängt und für einen begrenzten Zeitraum speichert

E-Mails sind der wichtigste Kanal der modernen Geschäftskommunikation.
Ihr versehentlicher Verlust würde der Wissensbasis des Unternehmens großen Schaden zufügen.
Darüber hinaus sollte Geschäftskorrespondenz in der Regel bis zu zehn Jahre lang aufbewahrt werden.
!! Wenn Ihr Unternehmen persönliche E-Mail-Adressen verwendet,
wie z. B. name.surname@companyname.com,
müssen Sie die Absender vor der Aktivierung dieser Funktion darüber informiert habenWir stellen Ihnen eine eigene Domain für eingehende E-Mails zur Verfügung:
So archiviert die „Inbox“-App von RealSender nahtlos
alle E-Mails, auf die Sie über folgende Adresse zugreifen können:
ein spezielles POP3-Postfach
,
das so konfiguriert ist, dass es innerhalb kurzer Zeit große Mengen an E-Mails empfangen kann
ein sicherer Webbereich unter
online verfügbar über eine angepasste Version unserer Webmail-Oberfläche
Ein automatischer Prozess archiviert die Nachrichten nach Empfänger, Monat und Jahr.
In Verbindung mit dem RealSender Secure Email Gateway (
)
werden alle versendeten E-Mails automatisch kopiert und archiviert.
Funktionen der Weboberfläche:
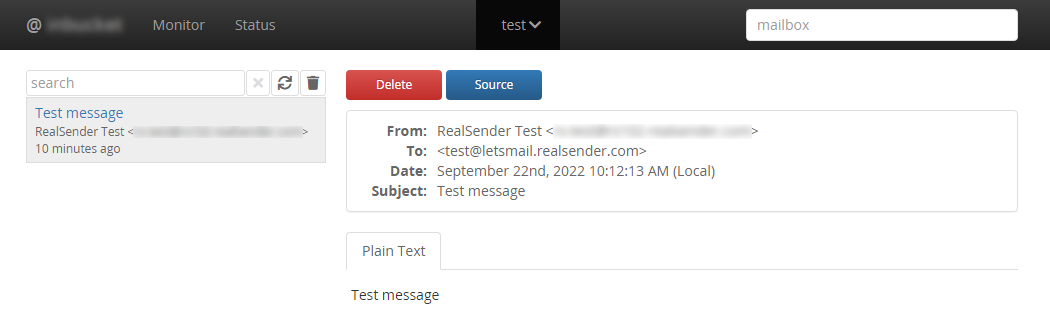
Eine funktionierende Demo ist in unserem (kostenlosen) Bereich für Postmaster-Tools verfügbar:
» inxbox Demo – temporäre E-Mail-Adresse

Die inxbox-App-Demo ist ein sofort einsatzbereites temporäres Postfach,
das jede Nachricht empfängt
und diese eine Stunde lang speichert
!! Alle empfangenen Nachrichten sind für jeden sichtbar !!Bitte beachten Sie: Der zugehörige Domainname unterscheidet sich von dem im vorherigen Punkt genannten.
E-Mails sind der Hauptkanal für Cyberangriffe.
Das Fälschen der Absenderadresse lässt sich anhand der E-Mail-Authentifizierungsdaten erkennen.
Die „spamstop“-App von RealSender zeigt die Ergebnisse der Echtheitsprüfungen
direkt im Betreff der empfangenen Nachrichten an.
In Kombination mit einem Filter
, der Nachrichten nach Absendern sortiert, die NICHT in Ihrem Adressbuch enthalten sind, ist dies eine effiziente Anti-Spam-Lösung.
Es kann für die gesamte Domain oder auch nur für einige wenige E-Mail-Adressen aktiviert werden.
Hauptmerkmale:
SPF-basierte Überprüfung des E-Mail-Absenders
Überprüfung des Absenders und des E-Mail-Siegels auf Basis von DKIM
Mindestens eine der Domänen muss mit der Absender-Domäne übereinstimmen
Zwei SPAM-Tags wurden dem Betreff hinzugefügt, um auf Betrug hinzuweisen
damit Sie in Ihrem Posteingang nur E-Mails von Absendern erhalten, die Sie zuvor zugelassen haben
um E-Mails nur von Absendern zu erhalten, die Sie zuvor autorisiert haben
um Ihre E-Mail-Postfächer vor unerwünschten Absendern und gefährlichen Anhängen zu schützen

Wir möchten sicherstellen, dass die Absenderadresse nicht gefälscht oder manipuliert wurde*.
* = die Nachricht so erscheinen lassen, als stamme sie von einer anderen Person als dem tatsächlichen Absender
Die SPF-Authentifizierung hilft uns festzustellen, ob die Nachricht über einen autorisierten SMTP-Server gesendet wurde.
Diese Informationen werden im DNS der Domain gespeichert, also an einem sicheren Ort außerhalb der E-Mail-Nachricht.
Nur wenn die Nachricht NICHT korrekt authentifiziert wurde:
wird das Symbol !! (Achtung) an den Betreff angehängt:
wird einer der folgenden Hinweise in den Kopf der Nachricht, in die Zeile „X-RealSender“, eingefügt:
:: spf-none :: Die Absenderdomain enthält keine Informationen zur Authentifizierung der E-Mail
:: spf-softfail :: Der SMTP-Server ist nicht unter den autorisierten Servern aufgeführt, dieser Fall sollte jedoch als „Softfail“ behandelt werden
:: spf-fail :: Der SMTP-Server ist nicht unter den autorisierten Servern aufgeführt, und die E-Mail sollte abgelehnt oder verworfen werdenManchmal sind die auf Domänenebene gespeicherten Informationen nicht korrekt oder nicht verständlich.
:: spf-permerror :: Es ist ein dauerhafter Fehler aufgetreten (z. B. ein falsch formatierter SPF-Eintrag)Die SPF-Prüfung erfolgt anhand der „Mail From“-E-Mail-Adresse, die in den E-Mail-Headern verborgen ist.
Sichtbar ist lediglich die „From“-E-Mail-Adresse. Wenn sich die Stammdomänen unterscheiden, wird folgende Warnung angezeigt:
:: spf-diff :: Die Stammdomänen von „Mail From“ und „From“ sind unterschiedlich
DKIM (DomainKeys Identified Mail) ermöglicht es Absendern nachzuweisen, dass die E-Mail tatsächlich von ihnen versendet wurde und nach dem Versand nicht verändert wurde.
Dies wird erreicht, indem jeder ausgehenden E-Mail-Nachricht eine digitale Signatur (ein Siegel) beigefügt wird, die mit einem Domainnamen verknüpft ist.
Nur wenn die Nachricht NICHT korrekt signiert wurde:
wird das Symbol !! (Achtung) an den Betreff angehängt:
wird einer der folgenden Hinweise in den Kopf der Nachricht, in die Zeile „X-RealSender“, eingefügt:
:: dkim-none :: Es wurden keine DKIM-Signature-Header (weder gültige noch ungültige) gefunden
:: dkim-fail :: Es wurde ein gültiger DKIM-Signature-Header gefunden, aber die Signatur enthält keinen korrekten Wert für die Nachricht Manchmal ist es nicht möglich, die Überprüfung durchzuführen:
:: dkim-invalid :: Es liegt ein Problem mit der Signatur selbst oder dem Eintrag des öffentlichen Schlüssels vor. Das heißt, die Signatur konnte nicht verarbeitet werden.
:: dkim-temperror :: Es wurde ein Fehler festgestellt, der wahrscheinlich nur vorübergehender Natur ist, wie z. B. eine vorübergehende Unmöglichkeit, einen öffentlichen Schlüssel abzurufen.Wenn die Nachricht mit einer anderen Domain signiert wurde, wird ein Hinweis auf die Abweichung hinzugefügt:
Diese Warnung erscheint NICHT, wenn der Absender die SPF-Prüfung besteht:
:: dkim-diff :: Die Nachricht wurde NICHT von der Domain des Absenders signiert
DMARC (Domain-based Message Authentication, Reporting and Conformance),
ist ein Standard zur E-Mail-Authentifizierung, der entwickelt wurde, um gefälschte E-Mails mit gefälschten Domänen zu bekämpfen.
Im Kapitel „3.1. Identifikatorabgleich“ heißt es:
E-Mail-Authentifizierungstechnologien authentifizieren verschiedene (und
unterschiedliche) Aspekte einer einzelnen Nachricht. Beispielsweise authentifiziert [DKIM]
die Domäne, die die Nachricht signiert hat,
während [SPF] entweder die Domäne authentifizieren kann, die im
RFC5321.MailFrom-Teil (MAIL FROM) von [SMTP] oder im RFC5321.EHLO/
HELO-Domäne oder beides. Dies können unterschiedliche Domänen sein, und sie sind
für den Endbenutzer in der Regel nicht sichtbar.
DMARC authentifiziert die Verwendung der RFC5322.From-Domäne, indem es verlangt, dass
diese mit einem authentifizierten Identifikator übereinstimmt (abgestimmt ist).
-- https://tools.ietf.org/html/rfc7489#section-3.1Das bedeutet ganz einfach:
Wenn ein Absender seine E-Mail mittels SPF und/oder DKIM authentifiziert,
muss mindestens eine der Domains mit der Absender-Domain übereinstimmenDieser Ansatz ist weithin anerkannt und gilt allgemein
als bewährte Methode zur Identifizierung vertrauenswürdiger Absenderdomänen.
Bei der SPF-Authentifizierung
muss die Stammdomain der „Mail From“-Adresse mit der Stammdomain der „From“-Adresse übereinstimmen.
Bei der gelockerten Übereinstimmung kann jede beliebige Subdomain verwendet werden, ohne dass die Anforderung an die Domain-Übereinstimmung verletzt wird.
Für die DKIM-Authentifizierung
muss die Stammdomain der DKIM-Signaturdomain mit der Absenderdomain übereinstimmen.
Bei einer gelockerten Übereinstimmung kann jede beliebige Subdomain verwendet werden, ohne dass die Anforderung an die Domain-Übereinstimmung verletzt wird.
Beide Regeln werden eingehalten:
Die Absenderdomain ist vollständig vertrauenswürdig:
Die Nachricht kommt unverändert an
Wenn nur eine der beiden Regeln erfüllt ist
wird das Tilde-Zeichen (~) an den Betreff angehängt,
wird eine der folgenden Erläuterungen in den Kopf der Nachricht eingefügt
~ ... Betreff ...
X-RealSender: ~ | spf=bestanden (Domäne NICHT abgeglichen) | dkim=bestanden | ~~ ... Betreff ...
X-RealSender: ~ | spf=pass | dkim=pass (Domäne NICHT abgeglichen) | ~
DMARC wird von immer mehr Unternehmen eingesetzt, um ihre Absender vor Spoofing zu schützen.
Die Nutzung erfordert eine ordnungsgemäße Authentifizierung mittels SPF oder DKIM sowie die Übereinstimmung der „From“- und „Mail-From“-Domains.
For more information:
<dmarc> act on fraudulent email
Nachrichten von Absendern mit dem _dmarc-Eintrag „
“
werden, sofern sie NICHT authentifiziert sind, im Betreff mit zwei [ SPAM ]-Markierungen hervorgehoben:
[ SPAM ] ... Betreff der Nachricht ... [ SPAM ]Nachrichten ohne den _dmarc-Eintrag, bei denen sowohl die SPF- als auch die DKIM-Authentifizierung fehlschlagen,
werden mit dem Tag [suspicious] im Betreff gemeldet:
[verdächtig] … Betreff der Nachricht … 
Die „spamstop“-App von RealSender ist eine effiziente Anti-Spam-Lösung
in Kombination mit einem Filter, der Nachrichten
nach Absendern sortiert, die NICHT in Ihrem Adressbuch enthalten sind.
Die meisten modernen E-Mail-Programme bieten diese Funktion an.
Hier sind einige Konfigurationsbeispiele:
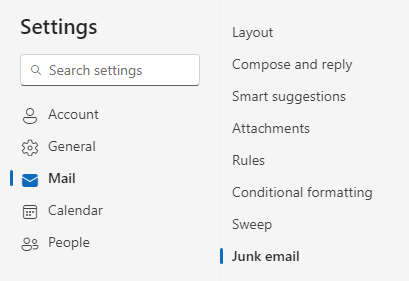
In den Outlook-Einstellungen aktivieren: E-Mails von meinen Kontakten als vertrauenswürdig einstufen
Erstelle in Thunderbird einen Filter mit der Regel „Absender ist nicht in meinem Adressbuch“.

Unten sehen Sie den Bildschirm „Einstellungen“ in Outlook.
Aktivieren Sie unter „Junk-E-Mails“ die Option „E-Mails von meinen Kontakten vertrauen“.
Klicken Sie auf [Speichern], um die Änderungen zu übernehmen.

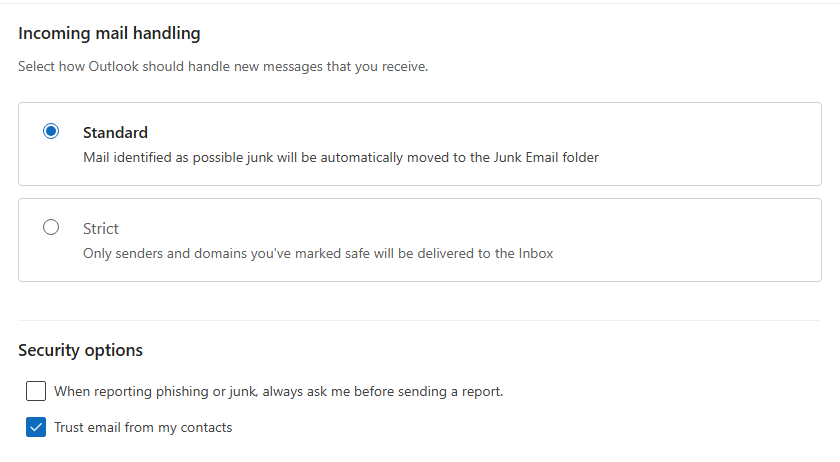

Unten sehen Sie einen Screenshot des Tools „Nachrichtenfilter“ in Thunderbird.
Fügen Sie Bedingungen mit der Option „Alle folgenden Bedingungen erfüllen“ hinzu:
Führen Sie folgende Schritte aus: Verschieben Sie die Nachricht in den Ordner „Spam“.

Nicht alle E-Mail-Programme bieten ausgefeilte Möglichkeiten zum Filtern von E-Mails.
In solchen Fällen kann man bereits im Vorfeld Maßnahmen ergreifen.
Mit der Funktion „Autorisierte Absender“ können Sie Nachrichten
nur von Absendern empfangen, die Sie zuvor autorisiert haben
(Sie können auch die gesamte Domain angeben, z. B. @example.com):
Alle normalen E-Mails werden wie gewohnt in Ihrem Posteingang ankommen.
Alle Spam-E-Mails werden in ein anderes Postfach weitergeleitet:
oder in den „Junk“-Ordner des Benutzers in Microsoft 365 Exchange.
Es gehen keine E-Mails verloren.
Sie können den Ordner mit den gelöschten Nachrichten ein- oder mehrmals täglich durchsehen.
So sparen Sie viel wertvolle Zeit.

Diese Konfiguration sorgt dafür, dass unerwünschte E-Mails
von nicht autorisierten Absendern korrekt in den Junk-E-Mail-Ordner des Benutzers verschoben werden
Die von der SpamStop-App gefilterten Nachrichten werden unter
mit den folgenden Anti-Spam-Headern und Werten zugestellt:
X-Forefront-Antispam-Report: SFV:SKB(Die Nachricht wurde vom Spamfilter
als Spam markiert, da die E-Mail-Adresse oder E-Mail-Domain des Absenders
NICHT in der Liste der zugelassenen Absender enthalten ist)
Die folgende Aktion muss aktiviert werden:
Setzen Sie den Spam-Konfidenzwert (SCL) dieser Nachrichten auf 6 (Spam)
Der Standardwert des Parameters „SCLJunkThreshold“ ist 4, was bedeutet, dass
bei einem SCL-Wert von 5 oder höher die Nachricht in den Junk-E-Mail-Ordner des Benutzers verschoben werden sollte.
Gehen Sie im Exchange-Verwaltungscenter (EAC) zu „Mailfluss“ > „Regeln“.
Wählen Sie auf der Seite „Regeln“ in der Dropdown-Liste die Option „Hinzufügen“ > „Neue Regel erstellen“ aus.
Nehmen Sie auf der sich öffnenden Seite „Neue Regel“ die folgenden Einstellungen vor:
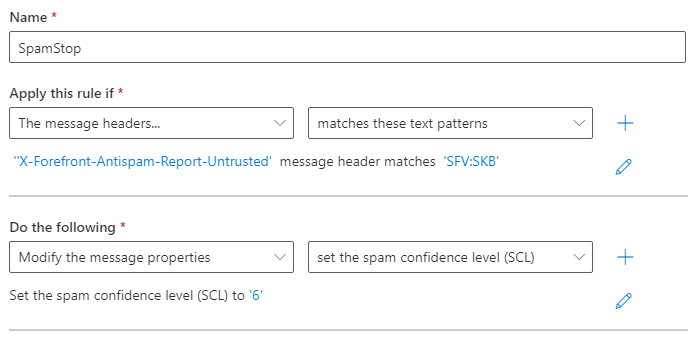
Name: SpamStop
Wende diese Regel an, wenn der Nachrichten-Header „X-Forefront-Antispam-Report-Untrusted“
mit „SFV:SKB“ übereinstimmt
Gehen Sie wie folgt vor:
Ändern Sie die Nachrichteneigenschaften
Setzen Sie den Spam-Konfidenzwert „SCL“ auf: ‚6‘
Speichern und aktivieren Sie die Regel.
Sie sorgen für zusätzliche Sicherheit bei Ihren E-Mails.
Um Ihre E-Mail-Postfächer
vor gefälschten Absendern und gefährlichen Anhängen zu schützen.
Sicherheitsoptionen, die auf Wunsch aktiviert werden:
um E-Mails nur von Absendern zu erhalten, die die Authentifizierungsprüfungen bestanden haben
um alle potenziell schädlichen Anhänge aus E-Mails zu entfernen
Dies ist nützlich, wenn Sie nur Nachrichten von verifizierten Absendern erhalten möchten.
Alle E-Mails, die die Prüfungen nicht bestehen, werden gelöscht oder zurückgewiesen.
Sie müssen sicherstellen, dass die E-Mail-Adresse des Absenders nicht gefälscht wurde.
Diese Überprüfung kann durch die Kombination von SPF- und DKIM-Authentifizierung erfolgen.
SPF bestätigt die Absenderadresse und deren Beziehung zu dem Server, von dem die Nachricht versendet wurde.
DKIM stellt sicher, dass E-Mail-Nachrichten (einschließlich Anhänge) nicht verändert werden
, nachdem sie beim Versand „signiert“ wurden.
Theoretisch ist das ganz einfach, in der Praxis können sowohl SPF als auch DKIM
auf eine andere Domain verweisen als die E-Mail-Adresse des Absenders.
Wir überprüfen, ob die SPF-Authentifizierung und die DKIM-Signatur mit der Domain in der Absenderadresse übereinstimmen.
Auf diese Weise kann nur der ursprüngliche Absender die E-Mail authentifizieren. Dies garantiert ihre Herkunft.

Die Option „Gefährliche Anhänge entfernen“ blockiert alle potenziell schädlichen Anhänge
mit Ausnahme einiger sicherer Dateiformate wie PDF, TXT, GIF, JPG und PNG.
Der Empfänger erhält die Nachricht ohne Anhang.
Am Anfang des Inhalts wird eine Warnung eingefügt, die wie folgt lautet:
WARNUNG: Diese E-Mail verstößt gegen die E-Mail-Sicherheitsrichtlinien Ihres Unternehmens und
wurde geändert. Weitere Informationen erhalten Sie von Ihrem IT-Administrator.
Ein Anhang mit dem Namen „example.zip“ wurde aus dieser E-Mail entfernt, da er
ein Sicherheitsrisiko darstellte. Wenn Sie dieses Dokument benötigen, wenden Sie sich bitte an
den Absender und vereinbaren Sie eine alternative Möglichkeit, es zu erhalten.Im Internet ist eine interessante Fallstudie veröffentlicht worden, die mit folgendem Satz endet:
„Für uns hat sich die Filterung von Anhängen als sehr erfolgreich erwiesen“
– web.mit.edu/net-security/Camp/2004/presentations/reillyb-mit2004.ppt (PowerPoint-Präsentation)

Themen in diesem Bereich:
Konfigurationsbeispiele für Newsletter-Software: GroupMail – Inxmail Professional – Joomla AcyMailing – MaxBulk Mailer – phplist – SendBlaster – WordPress MailPoet 3 – WordPress MailPoet 2 – WordPress Mailster
Automatische Einrichtung der Abmeldung per Mausklick für E-Mails
zur Analyse von zurückgesendeten Nachrichten, zur Erkennung von Hard- und Soft-Bounces
um Massen-E-Mails direkt über Ihr E-Mail-Programm zu versenden
So starten Sie mit RealSender:
Wir signieren E-Mails automatisch mit DKIM, sodass Sie nichts weiter tun müssen.
Haben Sie Fragen? Kontaktieren Sie uns!

GroupMail > Extras
Konten verwalten > Neu
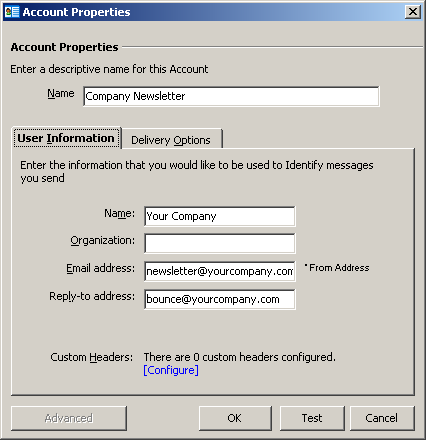
Kontoeinstellungen
Name / Benutzerdaten:
Füllen Sie das Formular mit den Daten Ihres Unternehmens aus

Lieferoptionen
Lieferoptionen: Standard
SMTP-Server: rsxxx-realsender.com
[x] Authentifizierung erforderlich
[Einrichtung]
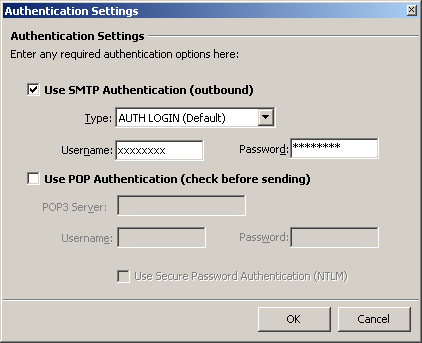
Authentifizierungseinstellungen
[x] SMTP-Authentifizierung verwenden (ausgehend)
Typ: AUTH LOGIN (Standard)
Benutzername: (den wir Ihnen geschickt haben)
Passwort: (das, das wir Ihnen geschickt haben)
[OK]

Erweiterte E-Mail-Einstellungen
SMTP-Port: 25
[x] Der Server erfordert eine SSL-Verbindung
Verwendung: STARTTLS (Standard)
[OK]

Globale Einstellungen > Verwaltung
> Mailserver > E-Mails versenden
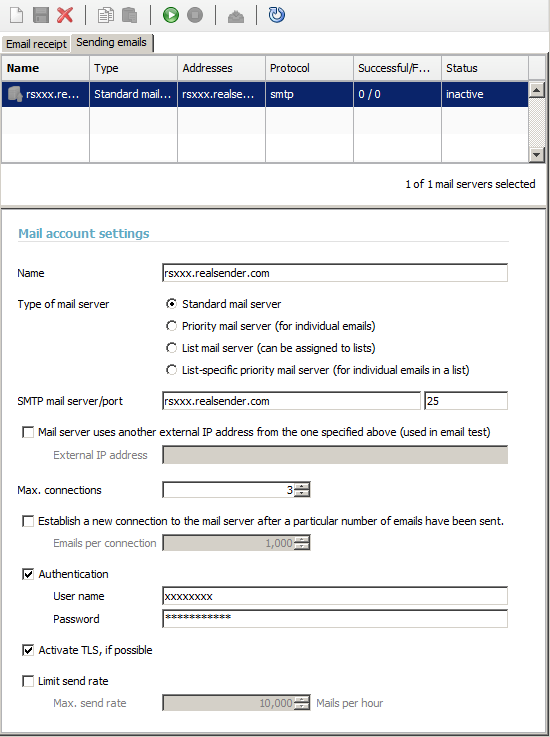
Einstellungen für E-Mail-Konten
Name: rsxxx.realsender.com
SMTP-Mailserver: rsxxx.realsender.com – Port: 25
Max. Verbindungen: 3
[x] Anmelde
Benutzername: (den wir Ihnen zugesandt haben)
Passwort: (das wir Ihnen zugesandt haben)[x] TLS nach Möglichkeit aktivieren
[Speichern]
[Verbindung zum E-Mail-Konto herstellen]


Joomla > Komponenten
AcyMailing > Konfiguration
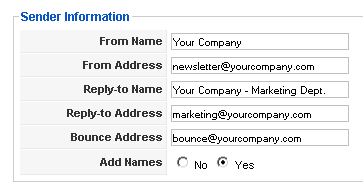
Absenderangaben
Füllen Sie das Formular mit den Daten Ihres Unternehmens aus
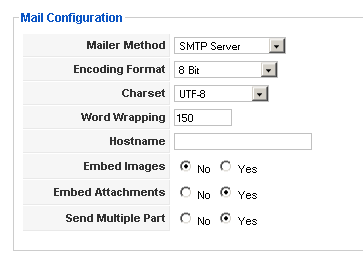
E-Mail-Konfiguration
Versandmethode: SMTP-Server
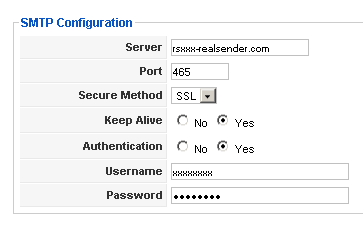
SMTP-Konfiguration
Server: rsxxx.realsender.com
Port: 465
Sicherheitsprotokoll: SSLKeep Alive: [x] Ja
Authentifizierung: [x] JaBenutzername: (den wir Ihnen zugesandt haben)
Passwort: (das wir Ihnen zugesandt haben)
[Einstellungen]
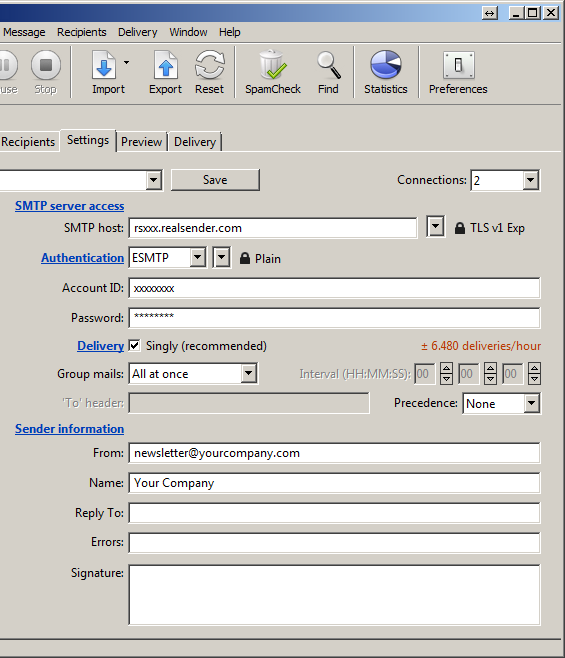
Einstellungen
Anschlüsse: 2
Zugriff auf den SMTP-Server
SMTP-Host: rsxxx.realsender.com – TLS v1 abgelaufen
Authentifizierung: ESMTP – Klartext
Konto-ID: (die, die wir Ihnen geschickt haben)
Passwort: (das, das wir Ihnen geschickt haben)
Versand: [x] Einzeln (empfohlen)
Gruppen-E-Mail: Alle auf einmal
Angaben zum Absender
Von: (E-Mail-Adresse des Absenders)
Name: (Beschreibung des Absenders)
[Neues Konto speichern unter…]
Name: rsxxx
[Erstellen]

Konfiguration getestet auf:
phplist, Version 3
Achtung: Erstellen Sie eine Sicherungskopie, bevor Sie
Änderungen an den Konfigurationsdateien Ihres PhpList-Servers vornehmen
PhpList-Konfiguration
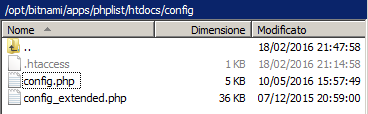
Ausfüllen phplist/htdocs/config/config.php
mit den richtigen Daten:
[…]
define(‘PHPMAILERHOST’, ‘rsxxx.realsender.com’);
[…]
define('PHPMAILER', 1);
define('PHPMAILER_SECURE', 'TLS');
$phpmailer_smtpuser = 'das von uns übermittelte';
$phpmailer_smtppassword = ’das von uns übermittelte’;
$phpmailer_smtpport = 587;
$pageroot = ‘/’;
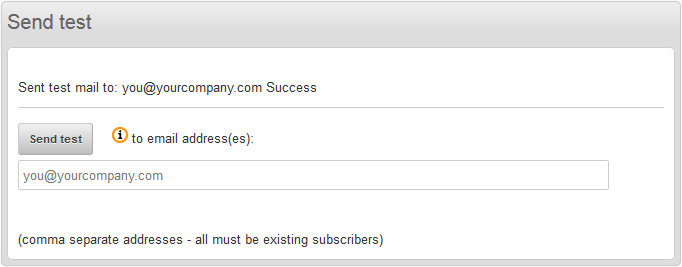

Nachrichten > Senden
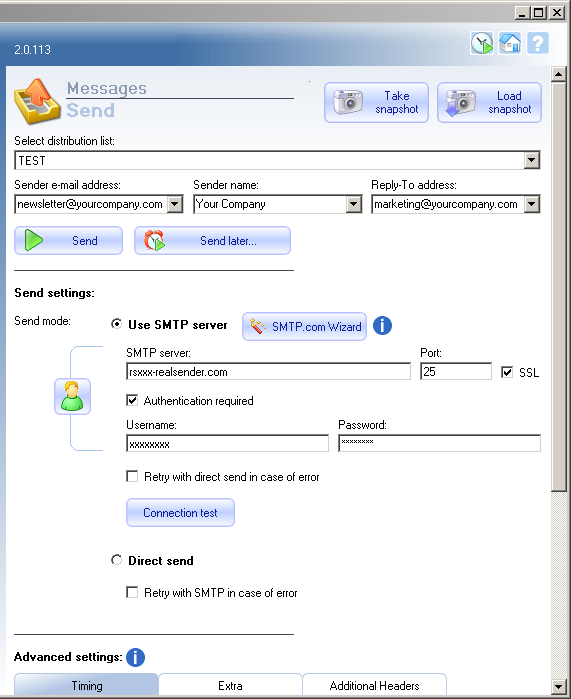
Sendeeinstellungen:
Sendemodus: [x] SMTP-Server verwenden
SMTP-Server: rsxxx.realsender.com
Port: 25 - [x] SSL[x] Anmeldung erforderlich
Benutzername: (den wir Ihnen zugesandt haben)
Passwort: (das wir Ihnen zugesandt haben)
[Schnappschuss machen]

Sendy

Marke auswählen > [Neue Marke hinzufügen]
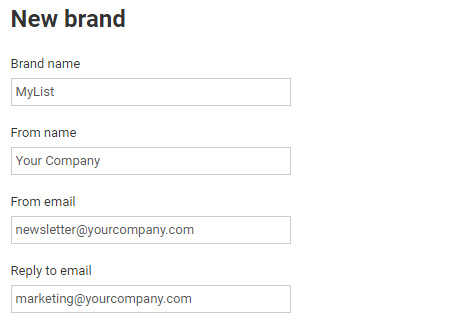
Neue Marke
Markenname
Nachname
Aus einer E-Mail
Auf E-Mail antworten
(Tragen Sie den Namen der Liste und die Daten Ihres Unternehmens in das Formular ein)
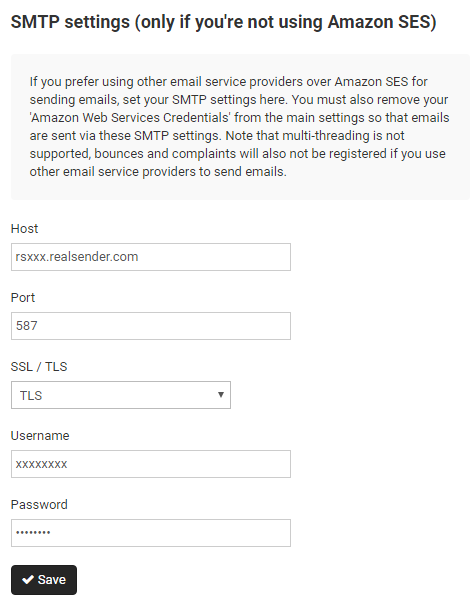
SMTP-Einstellungen
Host: rsxxx.realsender.com
Port: 587
SSL / TLS: TLS
Benutzername: (den wir Ihnen geschickt haben)
Passwort: (das, das wir Ihnen geschickt haben)
[Speichern]
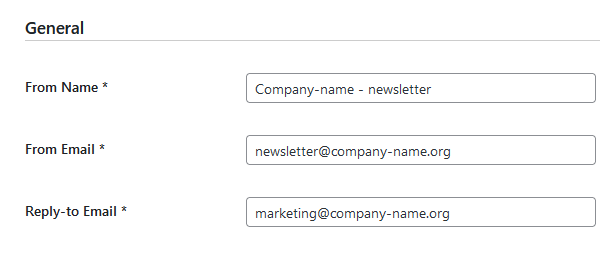
WordPress
MailPoet > Einstellungen
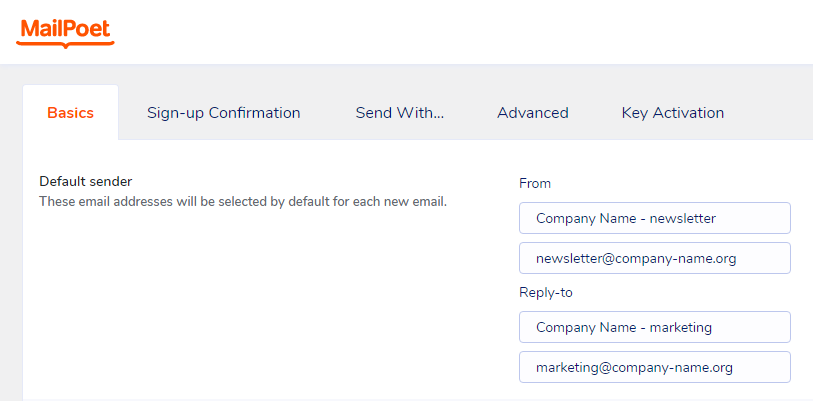
Grundlagen > Standard-Absender
(Füllen Sie das Formular mit den Daten Ihres Unternehmens aus)
Von:
Firmenname – Newsletter (Beschreibung)
newsletter@company-name.org (E-Mail-Adresse)Antwort an
Firmenname – Marketing (Beschreibung)
marketing@company-name.org (E-Mail-Adresse)
[Einstellungen speichern]
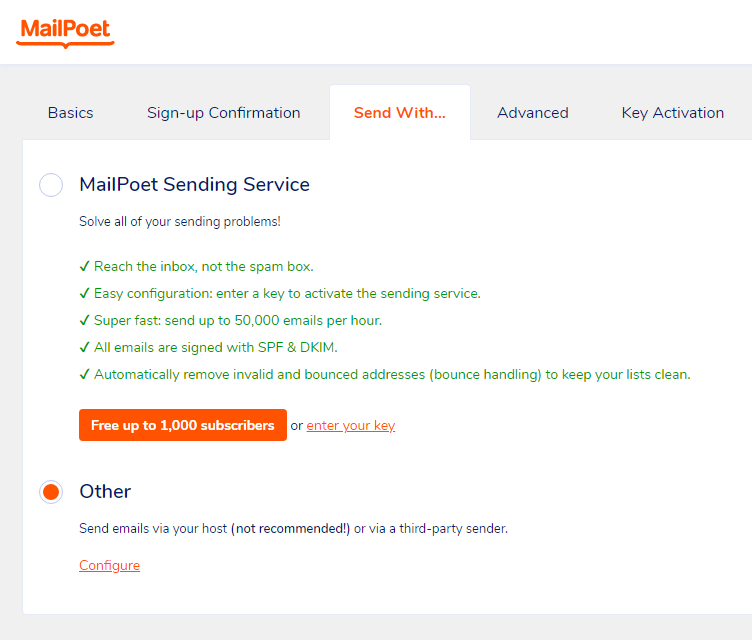
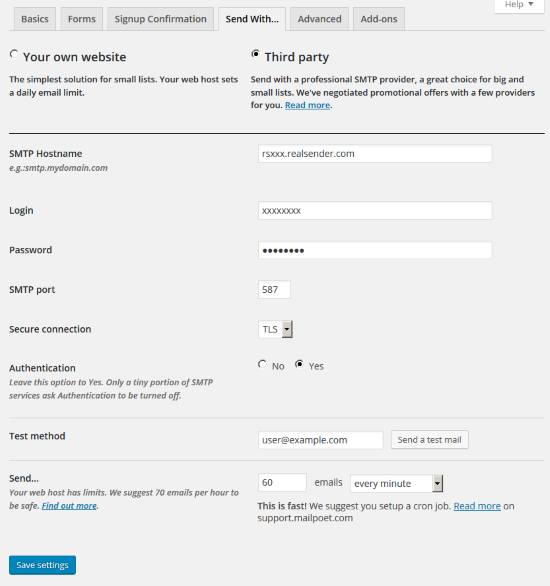
Senden mit…
[x] Sonstiges
Versenden Sie E-Mails über Ihren Host (nicht empfohlen!)
oder über einen externen E-Mail-Dienst.[Konfigurieren]
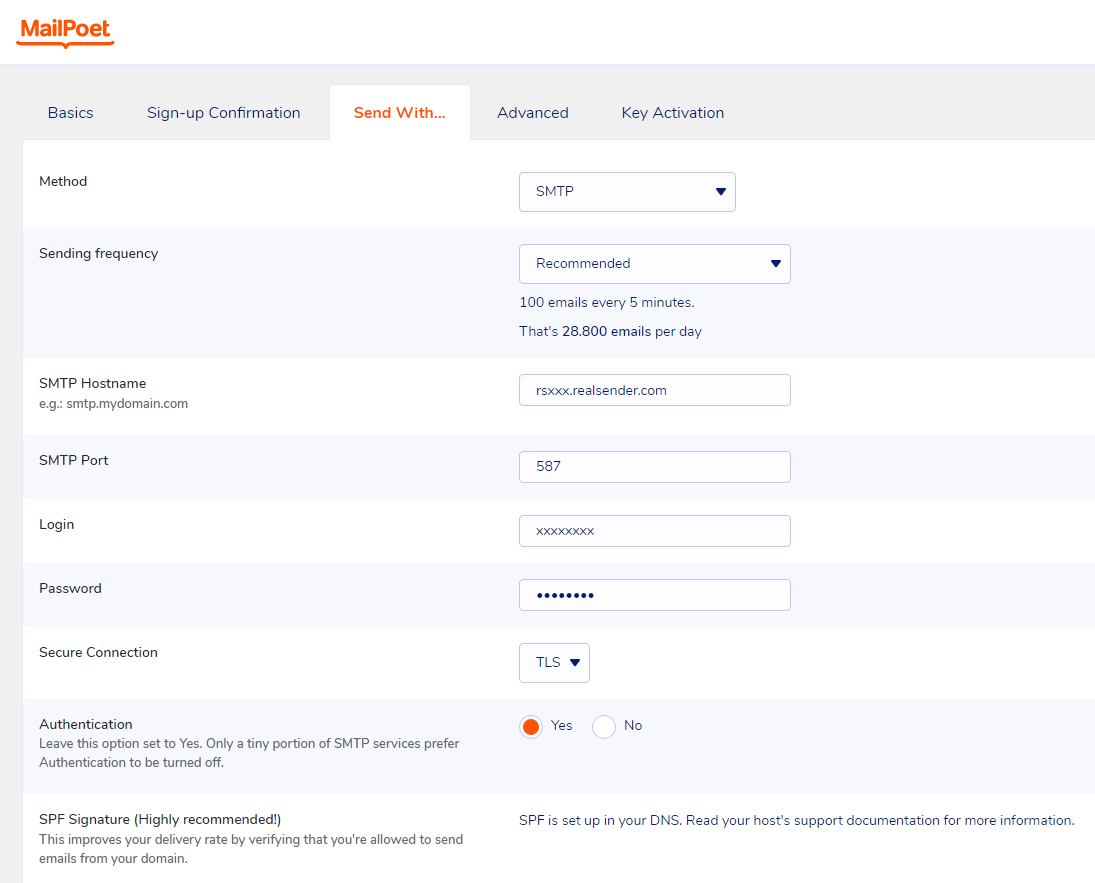
Senden mit…
Methode: SMTP
Versandhäufigkeit: Empfohlene
(100 E-Mails alle 5 Minuten. Das sind 28.800 E-Mails pro Tag)SMTP-Hostname: rsxxx.realsender.com
SMTP-Port: 587
Anmeldung: (die, die wir Ihnen geschickt haben)
Passwort: (das, das wir Ihnen geschickt haben)
Sichere Verbindung: TLS
Authentifizierung: [x] Ja
[Einstellungen speichern]
Für Premium-Funktionen und Support wählen Sie auf der Mailpoet-Preisseite
die Option „Ich möchte nur die Premium-Version ohne Versandfunktion“.
Auf diese Weise können Sie RealSender weiterhin nutzen,
und es mit einer speziellen E-Mail-Adresse kombinieren, um die Bounce-Meldungen zu empfangen.
Außerdem muss das Plugin „Bounce Handler Mailpoet“ installiert werden.
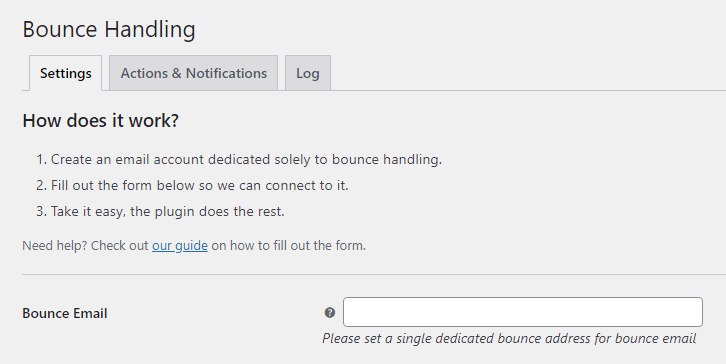
Umgang mit Bounces
Bounce-E-Mail:
Bitte richten Sie eine eigene Bounce-Adresse für Bounce-E-Mails ein

WordPress
MailPoet > Einstellungen
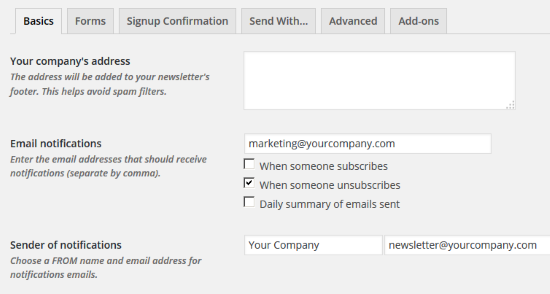
Grundlagen
E-Mail-Benachrichtigungen:
Bitte geben Sie hier die richtige E-Mail-Adresse einAbsender der Benachrichtigungen:
Bitte geben Sie die E-Mail-Adresse des Newsletters ein:
Absendername und E-Mail-Adresse
[Einstellungen speichern]
Senden mit…
[x] Drittanbieter
SMTP-Hostname: rsxxx.realsender.com
Anmeldung: (die, die wir Ihnen geschickt haben)
Passwort: (das, das wir Ihnen geschickt haben)
SMTP-Port: 587
Sichere Verbindung: TLS
Authentifizierung: [x] Ja
… 60 E-Mails pro Minute versenden
[Einstellungen speichern]

WordPress > Plugins
MailPress > Einstellungen
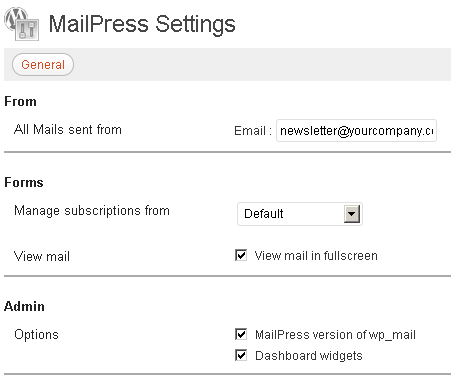
Allgemeines
Von – Alle E-Mails, die von
gesendet wurden
Tragen Sie die E-Mail-Adresse und den Namen des Absenders in das Formular ein
Wenn dies Ihre erste MailPress-Einrichtung ist
müssen Sie auf [Änderungen speichern] klicken
, um die zusätzlichen Einstellungsoptionen (SMTP, Test, Protokolle) anzuzeigen
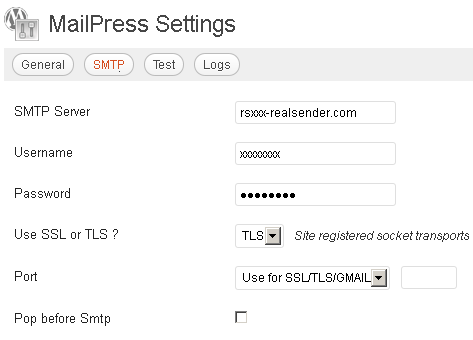
SMTP
SMTP-Server: rsxxx.realsender.com
Benutzername: (den wir Ihnen zugesandt haben)
Passwort: (das wir Ihnen zugesandt haben)SSL oder TLS verwenden? TLS
Port: Für SSL/TLS/Gmail verwenden

WordPress
Einstellungen > Newsletter
Allgemeines
Von:
Aus der E-Mail:
E-Mail-Adresse für die Antwort:
(Füllen Sie das Formular mit den Daten Ihres Unternehmens aus)
[Änderungen speichern]
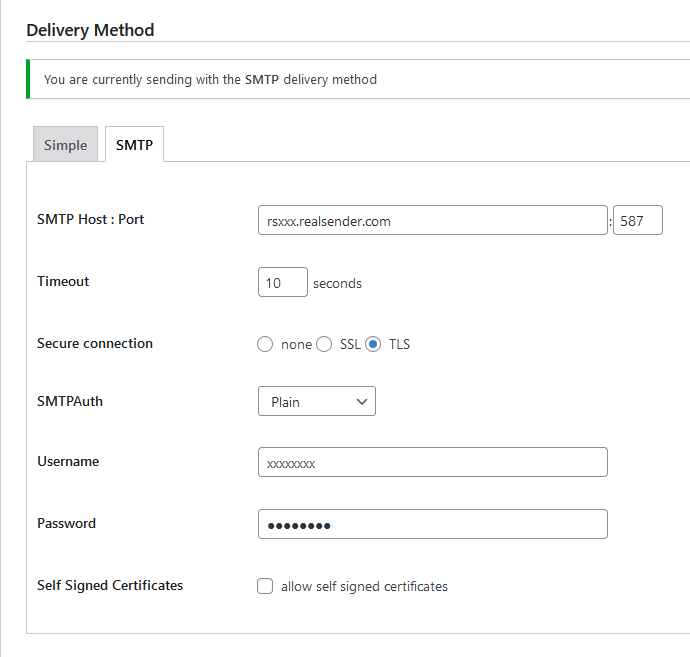
Lieferart
[SMTP]
SMTP-Host: Port rsxxx.realsender.com: 587
Zeitlimit: 10 Sekunden
Sichere Verbindung: [x] TLS
SMTPAuth: Plain
Benutzername: (den wir Ihnen geschickt haben)
Passwort: (das, das wir Ihnen geschickt haben)
[Änderungen speichern]
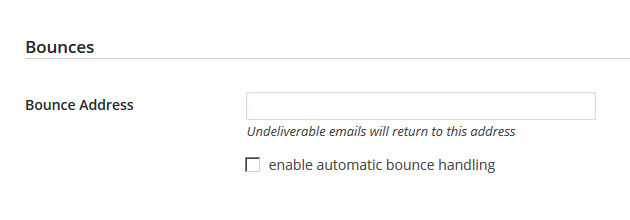
Abpraller
Bounce-Adresse:
Nicht zustellbare E-Mails werden an diese Adresse zurückgeschickt
Bieten Sie den Empfängern stets eine einfache Möglichkeit, sich von Ihren Nachrichten abzumelden.
Wenn Sie den Empfängern die Möglichkeit geben, sich von Ihren Nachrichten abzumelden, können Sie die Öffnungsraten,
die Klickraten und die Effizienz des Versands verbessern.
Wichtig: Wenn Sie mehr als 5.000 Nachrichten pro Tag versenden,
müssen Ihre Marketing- und Abonnement-Nachrichten die Abmeldung mit einem Klick unterstützen.
-- Gmail, Richtlinien für E-Mail-Absender, 2024Erfahren Sie mehr über die „List-Unsubscribe“-Header in RFC 2369 und RFC 8058.
Nachdem wir festgestellt hatten, dass die meisten unserer Kunden in ihren versendeten Nachrichten KEINE „List-Unsubscribe:“-Header verwendeten,
haben wir beschlossen, diese automatisch zu jeder Nachricht hinzuzufügen – allerdings nur, wenn diese Header noch nicht vorhanden sind.
Stornierungsanfragen MÜSSEN innerhalb von zwei Tagen bearbeitet werden.
Sie dürfen NICHT mit einer Abmeldeanfrage auf andere Weise antworten.
Gmail und andere Anbieter generieren automatisch eine E-Mail-Nachricht.
Diese wird an die E-Mail-Adresse gesendet, die Sie uns mitteilen (auch an mehrere Adressen).
Alternativ können Sie unter der Webadresse: rsXXX-realsender.com/unsubs
auf alle in den letzten sieben Tagen eingegangenen Abmeldeanfragen zugreifen,
im JSON-Format, wie im folgenden Beispiel gezeigt:
{
"mailbox": "rsXXX",
"id": "20241107T001800-0000",
"from": "<john.doe@gmail.com>",
"to": [
"<abuse@rsXXX-realsender.com>"
],
"subject": "RealSender :: rsXXX Nov-7 4A6NDqsl008203 :: please UNSUBSCRIBE me ::",
"date": "2024-11-07T00:18:00.938050657+01:00",
"posix-millis": 1730935080938,
"size": 4350,
"seen": false
},
Das wiederholte Versenden an falsche oder inaktive Empfänger gilt als „Spam-Verhalten“.
In den letzten Jahren wurden aus diesem Grund immer mehr SMTP-Server auf schwarze Listen gesetzt.
Der auffälligste Fehler tritt auf, wenn das Postfach der Mail-From-/Return-Path-Adresse,
– also das Postfach, in dem die zurückgesendeten Nachrichten landen – voll oder nicht vorhanden ist.
Wenn bei Tausenden von versendeten Nachrichten 20 % zurückkommen, ist selbst ein großes Postfach innerhalb weniger Minuten schnell voll.
Dass alle zurückgewiesenen Nachrichten empfangen werden, ohne dass sie gelesen werden, könnte als kleiner Makel angesehen werden.
Sie senden weiterhin E-Mails an Adressen, von denen sie zurückkommen, mit Fehlerdetails, die niemanden interessieren.
In beiden Fällen führt dies dazu, dass der SMTP-Server auf die schwarze Liste gesetzt wird. Auf diese Weise werden unter
nicht nur Nachrichten an ungültige Empfänger nicht zugestellt, sondern gültige Empfänger erhalten sie zudem als SPAM.
Um das erste Problem zu lösen, bieten wir schon seit Langem„Newsletter-Postfächer“an.
Die Analyse von Rückläufern ist schwieriger und erfordert ein Tool, das sehr gut funktioniert.

Wir haben uns für„Sisimai: Mail Analyzing Interface“entschieden, früher bekannt als bounceHammer 4: ein Tool zur Analyse von Fehler-E-Mails.
Eine Open-Source-Software, die Bounce-Mails nach RFC 5322 analysiert und strukturierte Daten im JSON-Format generiert.
Um einen Überblick über alle möglichen Fehlercodes zu erhalten, die Sisimai auswertet, werfen Sie einen Blick auf„The SMTP Field Manual“,
eine Sammlung von SMTP-Fehlercodes in Rohform, die von den wichtigsten E-Mail-Anbietern stammen.
Die Implementierung des Bounce-Handlers in RealSender ist ganz einfach.
Die App „bouncehandler“ beginnt mit der Überprüfung der zurückgewiesenen Nachrichten.
Zwei Sperrlisten werden aktiviert:
Die Blockliste für Hard Bounces
enthält alle E-Mail-Adressen, bei denen ein dauerhafter Fehler aufgetreten ist,
wie z. B. „Benutzer unbekannt“ oder „Host nicht erreichbar“
Das wöchentliche Protokoll der Hard Bounces ist unter folgender Webadresse verfügbar:
https://…hardbounces.email.weekly
Die Blockliste für Soft Bounces
enthält alle E-Mail-Adressen, bei denen drei oder mehr vorübergehende Fehler aufgetreten sind,
wie z. B. „Postfach voll“, wobei zwischen den einzelnen Fehlern mindestens eine Woche liegen muss
Das wöchentliche Soft-Bounce-Protokoll ist unter folgender Webadresse verfügbar:
https://…softbounces.email.weekly
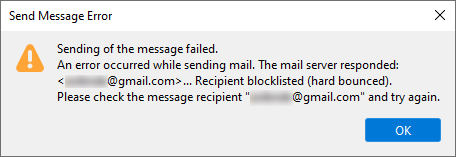
Das Senden von Nachrichten an einen Empfänger, der auf der Sperrliste steht, führt zu folgender Fehlermeldung:
Wir stellen Ihnen die folgenden Dateien zur Verfügung:
als Webadressen, die durch ein Passwort oder eine IP-Adresse geschützt sind:
https://…bounces.json
the details of the bounces received in the last seven days, in JSON format, such as:
{
"feedbacktype": "",
"addresser": "info@circuitocinemascuole.com",
"diagnostictype": "SMTP",
"timezoneoffset": "+0200",
"lhost": "linp.arubabusiness.it",
"destination": "gmail.com",
"timestamp": 1635536166,
"senderdomain": "circuitocinemascuole.com",
"deliverystatus": "5.1.1",
"token": "daad8f8fc89cef70e1406a9d2b38be6c35326e03",
"recipient": "...@gmail.com",
"subject": "Prenotazioni aperte_Giornata Internazionale dei Diritti dell'Infanzia e dell'Adolescenza_Film FIGLI DEL SOLE",
"origin": "/home/rs109-bounce/Maildir/new/1635528969.21113_0.rsbox.realsender.com",
"rhost": "gmail-smtp-in.l.google.com",
"reason": "userunknown",
"diagnosticcode": "550-5.1.1 The email account that you tried to reach does not exist. Please try double-checking the recipient's email address for typos or unnecessary spaces. Learn more at https://support.google.com/mail/?p=NoSuchUser z3si7494964ybg.507 - gsmtp 503 5.5.1 RCPT first. z3si7494964ybg.507 - gsmtp",
"messageid": "McuPi4DjtlyhvlSMVNB4wTXsUKQeIy6XwlKoAZuJ4@www.circuitocinemascuole.com",
"listid": "",
"action": "failed",
"softbounce": 0,
"replycode": "550",
"catch": null,
"alias": "",
"smtpagent": "Sendmail",
"smtpcommand": "DATA"
},https://…hardbounces.json
the details of the hard bounces 1 received in the last seven days, in JSON format
https://…hardbounces.email
the list of email addresses that generated a hard bounce 1 in the last seven days
1 = Auswahlkriterien: softbounce == 0
https://…softbounces.json
the details of the soft bounces 2 received in the last seven days, in JSON format
https://…softbounces.email
the list of email addresses that generated a soft bounce 2 in the last seven days
2 = Auswahlkriterien: softbounce == 1
Dies sind dieselben Dateien, die auch von der automatischen Sperrliste verwendet werden:
https://…hardbouncesfull.email
the list of all email addresses that generated two or more hard bounces
at least one week away from each other
https://…softbouncesfull.email
the list of all email addresses that generated three or more soft bounces
at least one week away from each other
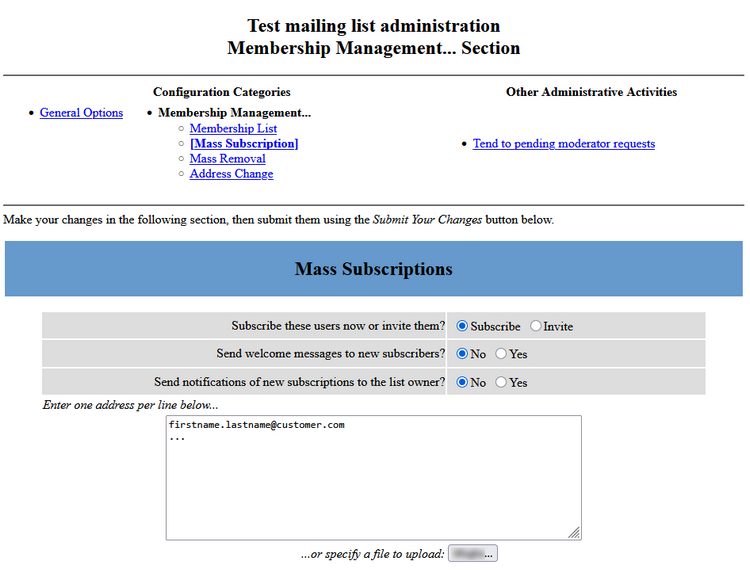
Um die durch den Versand von Newslettern und Massen-E-Mails generierten Rückmeldungen zu erhalten,
müssen Sie zusätzliche Postfächer einrichten (z. B. bounce@…)
und optional eine Mailbox für den Empfang von Antwort-E-Mails (z. B. news@…)
, falls Sie diese filtern und automatische Antworten auf die häufigsten Anfragen versenden möchten.
Aus diesem Grund haben wir zwei auf Ihr RealSender-Konto abgestimmte Postfächer eingerichtet:
bounce@email.youremaildomain.com -> bounce@rsXXX-realsender.com
news@email.youremaildomain.com -> news@rsXXX-realsender.com
Erläuterung:
Die Verwendung einer „Mail-From“-Adresse (auch bekannt als Bounce-/Return-Path-/Envelope-Adresse)
mit einer anderen Domain als der Absenderadresse
würde die DMARC-Authentifizierung unterbrechen
Um die „Newsletter-Postfächer“ zu nutzen,
müssen Sie eine Subdomain der Absenderadresse einrichten
z. B. lautet die Absenderadresse: offers@youremaildomain.com
könnte die Subdomain lauten: email.youremaildomain.com CNAME rsXXX-realsender.com
die Mail-From-Adresse lautet dann: bounce@email.youremaildomain.comDie vorgeschlagene Konfiguration entspricht den Richtlinien unter
,
um DMARC-konforme E-Mails im Auftrag von Kunden zu versenden.
Mit DMARC können Sie authentifizierte E-Mails über eine Subdomain (z. B. email.yourmaildomain.com) versenden und dennoch die Top-Level-Domain im „From:“-Header verwenden (z. B. From: offers@youremaildomain.com).
Es sind keine zusätzlichen Einstellungen im DNS Ihrer Domain erforderlich.
Gemäß RFC 1912, Abschnitt 2.4:
Ein CNAME-Eintrag darf nicht zusammen mit anderen Daten vorhanden sein.
Mit anderen Worten: Wenn „email.youremaildomain.com“ ein Alias für „rsXXX-realsender.com“ ist,
darfst du weder einen MX-Eintrag für „email.youremaildomain.com“ noch einen A-Eintrag
oder gar einen TXT-Eintrag haben Die Postfächer wurden so konfiguriert, dass sie
innerhalb kurzer Zeit große Mengen an E-Mails empfangen können, wie dies beispielsweise bei Bounce-Mails der Fall ist.
!!! Bitte beachten Sie: E-Mail-Nachrichten werden nach 7 Tagen automatisch gelöscht !!!
Um die E-Mails herunterzuladen, sollten Sie Ihren E-Mail-Client
oder die Anwendung zur Analyse der zurückgesendeten Nachrichten
mit der folgenden POP3-Serveradresse konfigurieren: pop.rsXXX-realsender.com.
Benutzernamen und Passwörter sind im geschützten Bereich der Website verfügbar.

Falls diese nicht vorhanden sind, fügt RealSender automatisch die Header „List-Unsubscribe“ und „
“
zu Ihren gesendeten Nachrichten hinzu, wie auf der Seite„Abmeldenvereinfachen“ beschrieben.
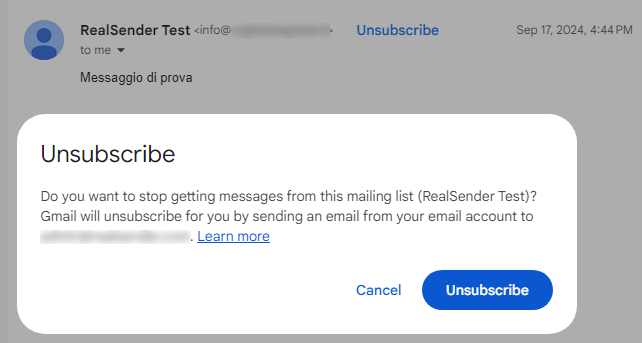
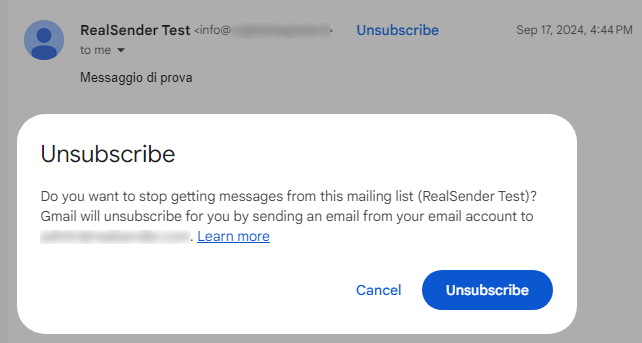
In der Messaging-App des Empfängers,
,
erscheint nach dem Klicken auf den Link „Abmelden“ eine Bestätigungsaufforderung:
Nach Eingang der Anfrage sendet uns der Anbieter die Kündigungsbestätigung an
,
die wir umgehend an die vom Kunden angegebene E-Mail-Adresse – gegebenenfalls an mehrere Adressen – unter
mit dem Betreff „RealSender :: rsXXX MM-TT #EMAILID# :: Bitte tragen Sie mich aus der Liste aus ::“ weiterleiten.
Die App „bouncehandler“ überprüft automatisch, ob unter
Abmeldeanfragen eingegangen sind,
und blockiert neue E-Mails von Empfängern, die darum gebeten haben, künftig keine E-Mails mehr zu erhalten.
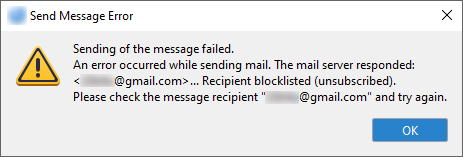
Die Blockliste für „Abmeldungen“ ist aktiviert:
Sie enthält alle E-Mail-Adressen, die über die oben beschriebene „List-Unsubscribe“-Funktion eine Abmeldung beantragt haben:
Das wöchentliche Protokoll aller „Abmeldungen“ ist unter folgender Webadresse verfügbar:
https://…unsubs.email.weekly
Das Senden von Nachrichten an einen Empfänger auf der Sperrliste führt zu einer Fehlermeldung wie dieser:
Wir stellen Ihnen die folgenden Dateien zur Verfügung:
als Webadressen, die durch ein Passwort oder eine IP-Adresse geschützt sind:
https://…unsubs.json
the details of unsubscribe requests received in the last seven days, in JSON format, such as:
{
"mailbox": "rsXXX",
"id": "20241121T181856-0088",
"from": "Jonh Doe <john.doe@bogusemail.net>",
"to": [
"<abuse@rsXXX-realsender.com>"
],
"subject": "RealSender :: rsXXX Nov-1 4ALGbKtb016000 :: please UNSUBSCRIBE me ::",
"date": "2024-11-21T18:18:56.908809804+01:00",
"posix-millis": 1732209536908,
"size": 4057,
"seen": false
},https://…unsubs.email
the list of email addresses that have requested unsubscription in the last seven days
Es handelt sich um dieselben Dateien, die auch von der automatischen Sperrliste verwendet werden:
https://…unsubssfull.email
the list of all email addresses that requested unsubscription, in alphabetical order

Mit der App „copymail“ von RealSender können Sie Massen-E-Mails
an bis zu Tausende von Empfängern direkt aus Ihrem E-Mail-Programm versenden.
In drei einfachen Schritten:
Jeder Empfänger erhält die Nachricht so, als wäre sie ausschließlich an ihn selbst gesendet worden,
wobei Ihre E-Mail-Adresse als Absender angegeben ist.
Wichtigste Merkmale:

Das wiederholte Versenden an falsche oder inaktive Empfänger gilt als „Spam-Verhalten“.
Die „Copymail“-App von RealSender erledigt dies automatisch und im Hintergrund.
Der Empfänger sieht nur den ursprünglichen Absender, der weiterhin die Antworten der Empfänger erhält.
E-Mail-Nachrichten enthalten einen Header, der für den Empfänger unsichtbar bleibt. Er heißt „Return-Path“ und ermöglicht es, Fehlermeldungen an eine andere E-Mail-Adresse zu senden.
Copymail füllt diesen automatisch mit wertvollen Informationen, die nicht nur den Empfang der Nachrichten ermöglichen, sondern auch Aufschluss darüber geben, von welcher Liste die Nachricht gesendet wurde und welche E-Mail-Adresse den Fehler verursacht hat.
Nachfolgend finden Sie ein Beispiel für den in eine Nachricht eingefügten Kopftext:
von der Liste „Test“ an den Empfänger gesendet „wrong.address@customer.com“:
Return-Path: <test-bounces+wrong.address=customer.com@mXXX-realsender.com>
Die Anwendung unterscheidet zwei Arten von Fehlern:
Hard Bounce (Statuscode 5.XXX.XXX): Die E-Mail-Adresse hat einen permanenten Fehler ausgelöst
wie beispielsweise „550 5.1.1 … Benutzer unbekannt“ oder „5.1.2 … Host unbekannt“
Ein permanenter Fehler bedeutet, dass Sie niemals wieder an diesen Empfänger senden sollten.
Soft Bounce (Statuscode 4.XXX.XXX): Die E-Mail-Adresse hat einen vorübergehenden Fehler verursacht
wie z. B. „452 4.2.2 … Postfach voll“
Ein vorübergehender Fehler bedeutet, dass Sie die Zustellung zu einem späteren Zeitpunkt erneut versuchen können.
Hier eine kurze Beschreibung, wie das automatische Bounce-Management funktioniert:
Nach drei Hard Bounces (dauerhafter Fehler, z. B. „Benutzer unbekannt“) oder sechs Soft Bounces (vorübergehender Fehler, z. B. „Postfach voll“) wird der Empfänger gesperrt und in der Abonnentenliste in der Spalte „nomail“ ein Häkchen gesetzt.
Sobald der Empfänger gesperrt wurde, werden drei Nachrichten mit dem Wortlaut „Ihr Abonnement für die Liste … wurde deaktiviert“ versendet, bevor der Empfänger aus der Liste entfernt wird.
Wenn der Empfänger aus der Liste entfernt wird, erhält der Administrator eine E-Mail-Benachrichtigung.
Hinweis: Nur ein Fehler pro Tag wirkt sich auf die Bewertung des Abonnenten aus. Selbst wenn also an einem Tag zehn Bounce-Mails eingehen, erhöht sich die Bewertung nur um einen Punkt.
All diese Vorgänge mögen einfach erscheinen und sogar manuell von einem Mitarbeiter erledigt werden können.
Dies ist jedoch nur bei sehr kleinen Zahlen möglich, also bei bis zu einigen hundert Empfängern.
Im Durchschnitt werden etwa 20 % der versendeten Nachrichten zurückgewiesen.
Von 1.000 E-Mails werden etwa 200 zurückgewiesen,
was ohne die Hilfe eines automatisierten Systems kaum zu bewältigen ist.
1. Die Nutzung automatisierter Anruf- und Kommunikationssysteme ohne
menschliches Eingreifen (automatische Anrufmaschinen), von Faxgeräten
oder von E-Mail zum Zwecke der Direktwerbung ist
nur gegenüber Teilnehmern oder Nutzern zulässig, die zuvor ihre Einwilligung erteilt haben.
2. Ungeachtet des Absatzes 1 darf eine natürliche oder juristische Person, die
im Rahmen des Verkaufs eines Produkts oder einer Dienstleistung von ihren Kunden deren elektronische Kontaktdaten für E-Mail erhält,
gemäß der
Richtlinie 95/46/EG, so darf dieselbe natürliche oder juristische Person diese elektronischen
Kontaktdaten für die Direktwerbung für ihre eigenen ähnlichen Produkte oder Dienstleistungen verwenden,
sofern den Kunden klar und deutlich die Möglichkeit gegeben wird,
kostenlos und auf einfache Weise einer solchen Verwendung der elektronischen
Kontaktdaten zum Zeitpunkt ihrer Erhebung sowie bei jeder
Nachricht zu widersprechen, falls der Kunde einer solchen Verwendung nicht bereits zuvor widersprochen hat.
-- Unaufgeforderte Mitteilungen, Auszug aus Artikel 13 der Richtlinie 2002/58/EGDiese mittlerweile überholte Regel dient nach wie vor als grundsätzliche Richtschnur. Kurz gesagt:
Abgesehen von den rechtlichen Konsequenzen führt die Nichtbeachtung dieser einfachen Regeln im Grunde dazu, dass man als „Spammer“ abgestempelt wird. Der dadurch verursachte Schaden kann sogar dazu führen, dass man nicht einmal mehr jene Empfänger erreicht, die Ihre Nachrichten eigentlich erhalten möchten.
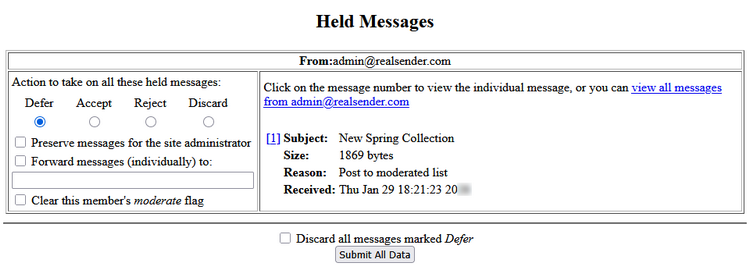
Die „Copymail“-App von RealSender bietet einen Link zu einer Seite mit „Optionen“ zum Abmelden von jeder Liste,
,
den der Kunde in seine E-Mail-Nachrichten einfügen kann. Hier ein Beispiel:
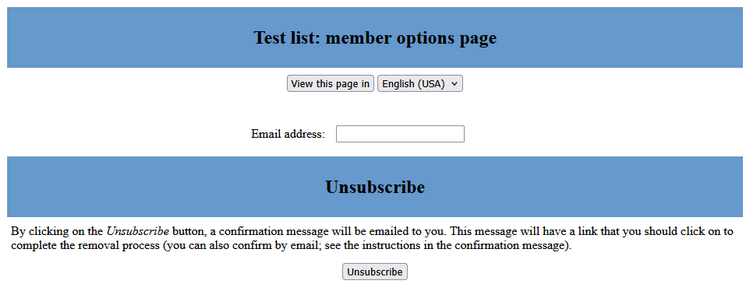
Nach dem Ausfüllen des Formulars erhält der Angabende eine E-Mail an
mit der Aufforderung, auf den Link zu klicken, um die Abmeldung zu bestätigen:
Wir haben eine Anfrage erhalten, ... Ihre E-Mail-Adresse,
... aus der ... Mailingliste zu entfernen. Um zu bestätigen, dass Sie
aus dieser Mailingliste entfernt werden möchten, besuchen Sie bitte diese Webseite:
(http-Adresse zur Bestätigung der Abmeldung)Dieselbe Nachricht wird an diejenigen gesendet, die sich unter
abmelden möchten,
und zwar über den Header „List-Unsubscribe: …“, der automatisch in jede versendete E-Mail eingefügt wird.
Dieser Header ermöglicht es Webmail-Anwendungen wie Gmail, den Link „Abbestellen“
direkt in der Benutzeroberfläche zu aktivieren, ohne dass der Nutzer ihn in der Nachricht suchen muss.
Um über alle Abmeldungen informiert zu werden, die von den Empfängern selbst vorgenommen wurden, wird empfohlen,
die Benachrichtigungsfunktion an die E-Mail-Adresse des Administrators
in den „Allgemeinen Optionen“ der Liste zu aktivieren:
Themen in diesem Bereich:
E-Mails ohne Authentifizierung versenden
Verwenden Sie Ihre eigene Subdomain, zum Beispiel: smtp.IhreDomain.com
So versenden Sie E-Mails über die API
Wie kann man die Ausgabe von HTTP-Anfragen, die durch Webformulare oder Textnachrichten generiert wurden, per E-Mail erhalten?
Erstellen Sie einfache Formulare und erhalten Sie die Daten per E-Mail
Fügen Sie vorab ausgefüllte, personalisierte Links in E-Mails ein und erhalten Sie sofortiges Feedback
erzeugt und übermittelt einen alphanumerischen Code, den der Benutzer bei der Anmeldung an einem geschützten System eingibt
nutzt den E-Mail-Proxy-Server, um die elektronische Kommunikation zu vereinfachen und mobile Geräte zu erreichen

Manchmal ermöglichen alte Softwareprogramme oder sehr einfache Anwendungen
keine sichere Authentifizierung, wie sie von RealSender verlangt wird.
Die Lösung besteht darin, einen Port für den Durchgang über den SMTP-Server
zu öffnen,
wobei lediglich die IP-Adresse der Verbindung und die E-Mail-Adresse des Absenders überprüft werden.
Auf diese Weise können Sie Ihre E-Mails ohne Authentifizierung versenden,
aber Sie haben jederzeit die Möglichkeit, sich zu authentifizieren, wann immer dies möglich ist.
RealSender-Partner und große Organisationen
können die Liste der autorisierten IP-Adressen selbstständig aktualisieren.
Der SMTP-Hostname eines Unternehmens wird in den Einstellungen mehrerer Anwendungen verwendet.
Eine Änderung ist fehleranfällig und zeitaufwendig.
Mit RealSender können Sie Ihre Subdomain festlegen, zum Beispiel:
smtp.deine-E-Mail-Domain.comWir kümmern uns um alles, einschließlich der SSL-Zertifikate
,
die für die sichere SMTP-Authentifizierung erforderlich sind.
Mit dieser Konfiguration können Sie ganz beruhigt sein,
da Sie wissen, dass der SMTP-Hostname unter Ihrer Kontrolle steht.
Ihre IT-Mitarbeiter müssen sich nicht mehr merken, wo
konfiguriert ist,
da es nicht mehr geändert werden muss.
Bitte beachten Sie: Die erforderliche Sonderkonfiguration
ist mit zusätzlichen jährlichen Kosten verbunden
, die im Rahmen der Angebotsphase näher erläutert werden.
Themen in diesem Bereich:
Serveradresse, obligatorische Parameter, JSON-Antworten
Zeichensatz, Content-Type, optionale Parameter, JSON-Antworten
Beispiele für PHP und cURL
Beispiele für PHP und cURL mit Anhängen
Mit RealSender können Sie E-Mails über eine API (Application Programming Interface) versenden.
Auf diese Weise können Sie die E-Mails direkt aus Ihrer Anwendung versenden, ohne den Umweg über SMTP (Simple Mail Transfer Protocol) zu nehmen. Derzeit unterstützen wir ausschließlich POST-Anfragen.
Serveradresse:
https://rsXXX-api.realsender.com/mail/send
Erforderliche/obligatorische Parameter:
| apiuser | Benutzername für die Authentifizierung |
| apipass | Authentifizierungspasswort |
| von | E-Mail-Adresse des Absenders |
| zu | E-Mail-Adresse des Empfängers |
| Betreff | Betreff der E-Mail |
| Text | E-Mail-Text im Klartext |
| html | E-Mail-Text im HTML-Format |
Wenn alles in Ordnung ist, wird die Nachricht gesendet und Sie erhalten eine positive JSON-Antwort:
{"success":true}
Im Falle von Fehlern wird etwa Folgendes angezeigt:
{"success":false,"errorMsgs":["Please provide the 'subject' value."]}
Der Inhalt muss im internationalen Zeichensatz UTF-8 gesendet werden.
Um dies zu testen, fügen Sie „€uro“ in Ihre Betreffzeile ein und senden Sie die Nachricht ab. Wenn der Zeichensatz falsch ist, erhalten Sie folgende JSON-Warnung:
{"success":false,"errorMsgs":["The 'subject' value is not correctly encoded. It must be UTF-8 encoded."]}
Je nachdem, ob Sie das Feld „text“ oder beide Felder („text“ und „html“) ausgefüllt haben, werden die Nachrichten mit einem der folgenden „Content-Type“-Angaben versendet :
| Text | text/plain (nur Text) |
| html | text/html (nur HTML) |
| Text+HTML | multipart/alternative (sowohl Text als auch HTML) – Die Einstellungen des E-Mail-Clients entscheiden darüber, welcher Teil angezeigt wird |
Nicht erforderliche/optionale Parameter:
| Absender | Absenderbeschreibung |
| toname | Beschreibung des Empfängers |
| Antworten an | E-Mail-Adresse, an die die Antworten gesendet werden |
| Rückweg | E-Mail-Adresse, an die die zurückgewiesenen E-Mails gesendet werden: . Diese muss in der Liste der autorisierten Absender des RealSenders enthalten sein. |
| cc | E-Mail-Adresse im BCC-Feld |
| ccname | Beschreibung der Durchschrift |
| bcc | E-Mail-Adresse für die Blindkopie |
| bccname | Beschreibung der Blindkopie |
| anhängen | Anhang(e) – können im Formular mehrfach vorkommen – maximale Größe 3 MB Der Dateiinhalt muss Teil des Multipart-HTTP-POST-Anrufs sein enctype=“multipart/form-data” ist für INPUT TYPE=FILE erforderlich |
Die Felder „An“, „cc“ und „bcc“ können eine einzelne E-Mail-Adresse oder eine durch Kommas getrennte Liste von E-Mail-Adressen enthalten.
!! In RealSender ist die Gesamtzahl der Empfänger pro E-Mail auf 25 begrenzt (sie kann auf bis zu 100 erhöht werden).
Die Antworten des Servers liegen im JSON-Format (JavaScript Object Notation) vor:
| E-Mail gesendet | {"success":true} |
| E-Mail wurde NICHT gesendet | {"success":false,"errorMsgs":["..."]} |
POST-Anfrage an
CURL-freie Methode mit PHP
<?php
$url = 'https://rsXXX-api.realsender.com/mail/send';
$data = array('apiuser' => 'the one we provided you', 'apipass' => 'the one we provided you', 'from' => 'sender@example.com', 'to' => 'recipient@example.com', 'subject' => 'subject of the message', 'text' => 'email body in plain text', 'html' => 'email body in HTML format');
// use key 'http' even if you send the request to https://...
$options = array(
'http' => array(
'header' => "Content-type: application/x-www-form-urlencoded\r\n",
'method' => 'POST',
'content' => http_build_query($data),
),
);
$context = stream_context_create($options);
$result = file_get_contents($url, false, $context);
var_dump($result);
?>POST-Anfrage an
CURL-Methode
curl -d 'apiuser=der von uns bereitgestellte&apipass=der von uns bereitgestellte you&from=sender@example.com&to=recipient@example.com&subject=Betreff der Nachricht&text=E-Mail-Text im Klartext&html=E-Mail-Text im HTML-Format'https://rsXXX-api.realsender.com/mail/sendPOST-Anfrage mit Anhängen (max. 5: attach1, attach2, …)
CURL-freie Methode mit PHP
<?php
require_once 'HTTP/Request2.php';
$config = array('use_brackets' => false,
);
$request = new HTTP_Request2('https://rsXXX-api.realsender.com/mail/send',
HTTP_Request2::METHOD_POST,
$config);
$data = array('apiuser' => 'the one we provided you',
'apipass' => 'the one we provided you',
'from' => 'sender@example.com',
'to' => 'recipient@example.com',
'subject' => 'subject of the message',
'text' => 'email body in plain text',
'html' => 'email body in HTML format');
foreach ($data as $k => $d) {
$request->addPostParameter($k, $d);
};
$request->addUpload('attach1', './sample.pdf', 'sample.pdf', 'application/pdf');
$request->addUpload('attach2', './sample.txt', 'sample.txt', 'text/plain');
$result = $request->send();
var_dump($result);
?>POST-Anfrage mit Anhängen
CURL-Methode
curl -F 'apiuser=der von uns bereitgestellte' \
-F 'apipass=der von uns bereitgestellte' \
-F 'from=sender@example.com' \
-F 'to=recipient@example.com' \
-F 'subject=Betreff der Nachricht' \
-F 'text=E-Mail-Text im Klartext' \
-F 'html=E-Mail-Text im HTML-Format' \
-F 'attach=@sample.pdf;type=application/pdf' \
-F 'attach=@sample.txt;type=text/plain' \
https://rsXXX-api.realsender.com/mail/sendThemen in diesem Bereich:
Skriptadresse, obligatorische Parameter, ausgeblendete und nicht ausgeblendete Felder
Nicht erforderliche / optionale Parameter, ausgeblendete und nicht ausgeblendete Felder
Einfaches Beispiel für ein HTML-Webformular
Beispiel für die Konfiguration der SMS-Weiterleitung an HTTP mithilfe von Teltonika-Routern
Mit RealSender können Sie ganz einfach HTTP-Anfragen, wie beispielsweise Inhalte von Webformularen, per E-Mail versenden.
Auf diese Weise erhalten Sie die Ergebnisse Ihrer Feedback-Formulare direkt in Ihrem E-Mail-Postfach.
Es sind keine besonderen Einstellungen Ihrerseits erforderlich.
Die Formulare können auf jeder HTML-Webseite veröffentlicht oder direkt in Ihre E-Mails eingefügt werden.
Skriptadresse:
<form action="https://rsXXX.realsender.com/script/form.pl" method="post" accept-charset="utf-8">
Erforderliche/obligatorische Parameter (ausgeblendete Felder):
| Empfänger | die E-Mail-Adresse oder den „Alias“, an den die Formularübermittlung gesendet wird: . Aus Sicherheitsgründen sollte die „echte“ Adresse auf Serverebene konfiguriert werden. |
| erforderlich | Dies ist eine Liste der Felder, die der Benutzer ausfüllen muss, bevor er das Formular absendet: . Wir empfehlen, nur das Feld „E-Mail“ zu überprüfen (Inhalt und Syntax werden überprüft): . Zusätzliche Überprüfungen werden in der Regel über JavaScript durchgeführt; wir können Beispiele bereitstellen. |
| Weiterleitung | Nach erfolgreicher Formularübermittlung wird der Benutzer zu dieser URL weitergeleitet |
| Umleitung bei fehlenden Feldern | Der Benutzer wird hierher weitergeleitet, wenn eines der „erforderlichen“ Felder leer gelassen wird |
Erforderliche/obligatorische Parameter (nicht ausgeblendete Felder):
| Es wird zur E-Mail-Adresse des Absenders der Nachricht | |
| falls die E-Mail-Adresse korrekt ist |
Die Daten werden an die konfigurierte Empfänger-E-Mail-Adresse gesendet. Der Benutzer wird zur „Redirect“-URL weitergeleitet. |
| falls die E-Mail-Adresse fehlt oder syntaktisch falsch ist |
Es wird keine E-Mail an gesendet; der Benutzer wird stattdessen auf die URL „missing_fields_redirect“ weitergeleitet. |
Nicht erforderliche/optionale Parameter (ausgeblendete Felder):
| Betreff | die Betreffzeile der E-Mail |
| Umweltbericht | Eine Liste der Umgebungsvariablen des Benutzers, die in die E-Mail aufgenommen werden sollen . Dies ist nützlich, um beispielsweise die IP-Adresse des Benutzers zu erfassen. Beispiel: value=“REMOTE_HOST,REMOTE_ADDR,HTTP_USER_AGENT” |
| Leere Felder drucken | Wenn dieser Wert auf „1“ gesetzt ist, werden leere Felder in die E-Mail aufgenommen |
Nicht erforderliche/optionale Parameter (nicht ausgeblendete Felder):
| Echter Name | Wenn der vollständige Name des Benutzers angegeben wird, wird er Teil der E-Mail-Adresse des Absenders |
| beliebiges_anderes_Feld | Sie können so viele Felder hinzufügen, wie Sie benötigen; auf Serverebene ist keine Konfiguration erforderlich |
Für die Übermittlung des Formulars wird der internationale Zeichensatz UTF-8 verwendet.
Um dies zu testen, fügen Sie in einem beliebigen Feld „€uro“ ein, senden Sie das Formular ab und überprüfen Sie die E-Mail-Nachricht, die Sie erhalten.
Dies ist ein einfaches Beispiel für ein HTML-Webformular
mit zwei optionalen Parametern: „realname“ und „notes“
<form action="https://rsXXX.realsender.com/script/form.pl" method="post" accept-charset="utf-8">
<input type="hidden" name="recipient" value="email_address-or-alias" />
<input type="hidden" name="required" value="email" />
<input type="hidden" name="redirect" value="/form/thankyou.html" />
<input type="hidden" name="missing_fields_redirect" value="/form/error.html" />
Name:<br />
<input name="realname" /><br />
Email:<br />
<input name="email" /><br />
Notes:<br />
<textarea cols="40" rows="2" name="notes"></textarea><br />
<input type="submit" />
</form>Die Landingpages „redirect“ und „missing_fields_redirect“ können auf Ihrem Server gehostet werden.
Sie können so viele Felder hinzufügen, wie Sie benötigen; auf Serverebene ist keine Einrichtung erforderlich.
Um SMS-Nachrichten direkt in Ihrem Postfach unter
zu empfangen
bieten Teltonika-Router die Option „SMS-Weiterleitung an HTTP konfigurieren“ an.
Sie finden diese Option in der Teltonika-WebUI unter: Dienste > Mobile Dienste > SMS-Gateway.
!! Die Domain des Empfängers (yourdomain.com) muss zuvor von RealSender autorisiert worden sein !!
Name des Zahlenwerts: email
Methode: Post
URL: https://rsXXX.realsender.com/script/sms.pl
Name des Nachrichtenwerts: message
Zusatzdatenpaar 1: recipient | name@yourdomain.com
Zusatzdatenpaar 2: subject | Text-Message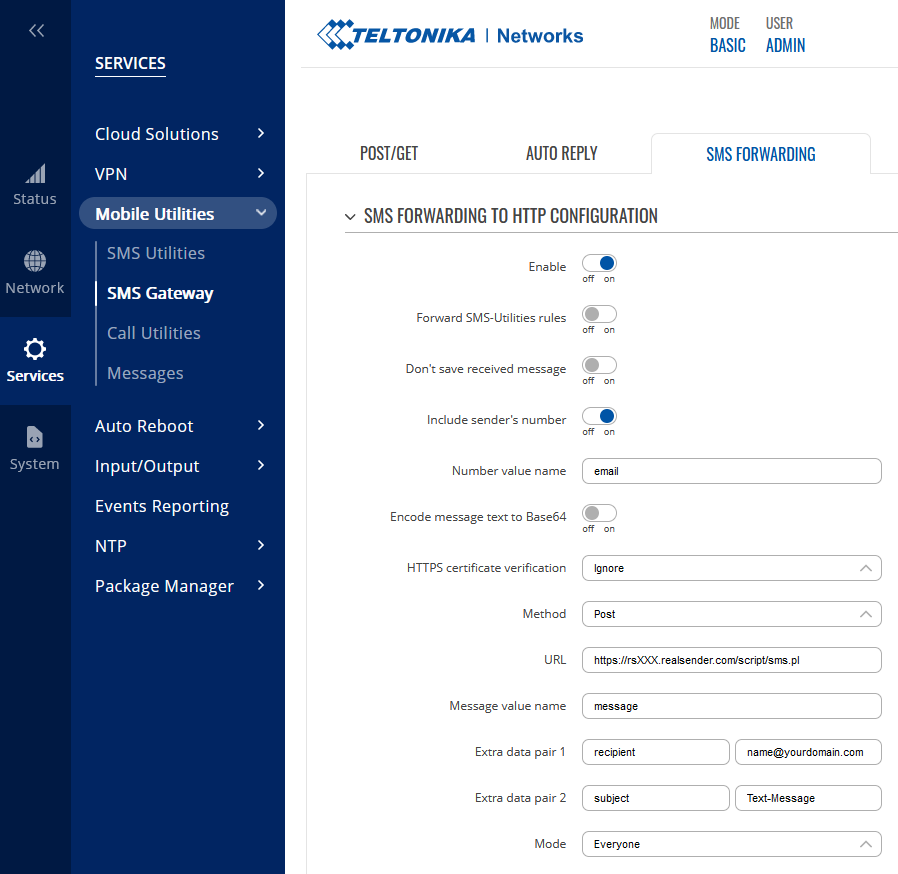
!! Für die ordnungsgemäße Funktion von RealSender ist eine 4G-Verbindung (LTE) erforderlich !!
Sie können dies in der Teltonika-WebUI einrichten: Netzwerk > Mobilfunk > SIM-Karteneinstellungen
Netzwerktyp: Nur 4G (LTE)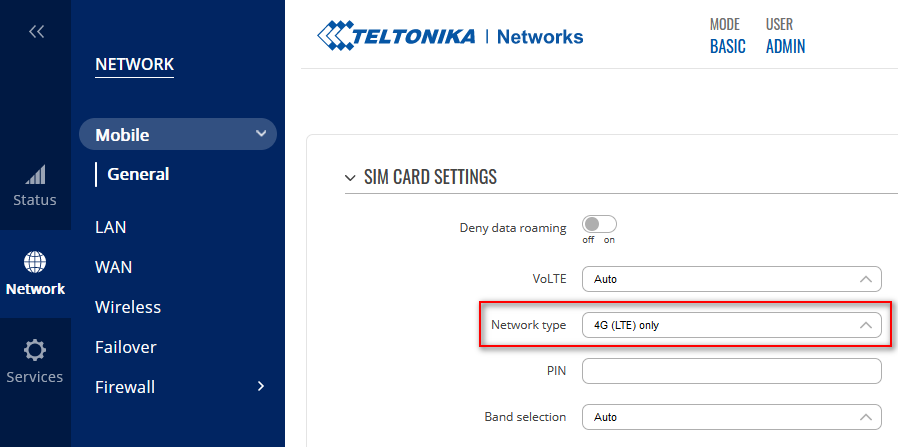
Sie können das Internet-Gateway so einstellen, dass es über Ihr LAN läuft.
Teltonika WebUI: Netzwerk > LAN > NETZWERKSCHNITTSTELLEN > [Bearbeiten]
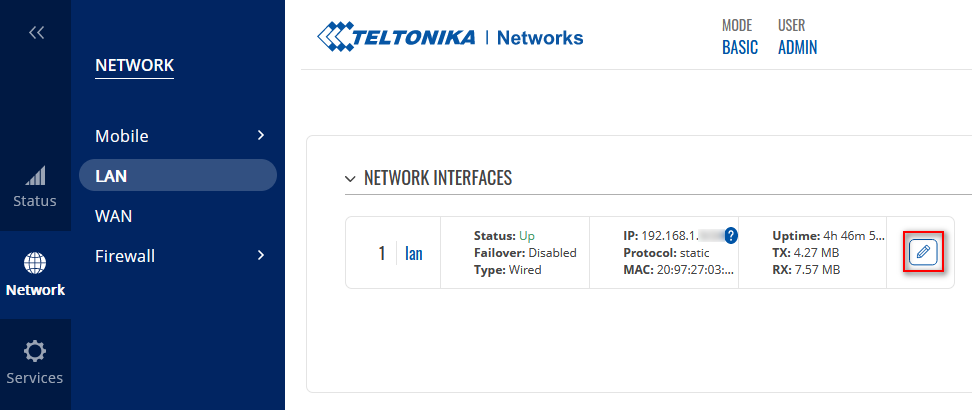
Konfigurieren Sie einfach das IPv4-Gateway und die DNS-Server unter
siehe das folgende Beispiel (passen Sie es an Ihre eigenen Parameter an):
SCHNITTSTELLEN: LAN
...
IPv4-Gateway: 192.168.1.1
DNS-Server: 8.8.8.8 !! obligatorisch !!Die mobile Datenverbindung kann auf verschiedene Weise deaktiviert werden, siehe: „Mobile Daten deaktivieren“.
Wenn die mobilen Daten deaktiviert sind, funktioniert der SMS-Versand weiterhin.
The easiest way to Disable Mobile Data, is to TEXT to the mobile number: <router_password> mobileoff
You can check the changes in the same way, using the “status” command: <router_password> status
Betreff: SMS (+41790000000)
Nachfolgend finden Sie die empfangene SMS. Sie wurde von
(+41790000000) am Montag, 26. Juni 2023 um 08:31:29 MESZ eingereicht
---------------------------------------------------------------------------
Testnachricht
---------------------------------------------------------------------------
Es kann schwierig sein, über das Internet klare und strukturierte Informationen zu erhalten.
Dazu ist eine Benutzeroberfläche zum Ausfüllen sowie eine Serveranwendung erforderlich, die die Daten übermittelt.
Mit dem „Formular-Generator“ von RealSender können Sie einfache und responsive Formulare erstellen,
die somit auch auf Tablets und Smartphones mit kleinen Bildschirmen genutzt werden können,
und die die Daten direkt an Ihre E-Mail-Adresse senden.
Einige „Drag & Drop“-Komponenten helfen Ihnen dabei, Ihre Fragen zu strukturieren:
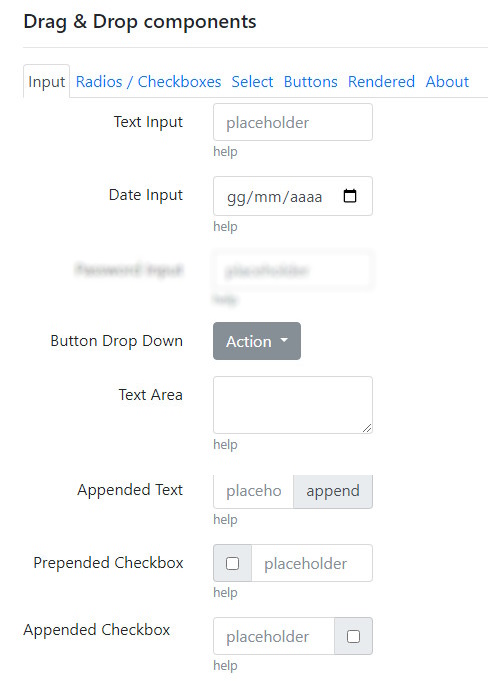
Die Quelle kann als gebrauchsfertige „form.html“-Datei heruntergeladen werden:
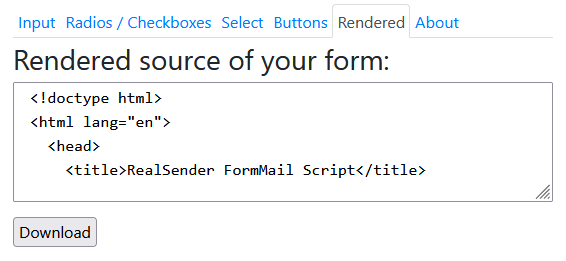
Die Nachricht wird im„Temporary-E-Mail“-Dienst von RealSender empfangen: inxbox.realsender.com
HINWEIS: In der Datei „form.html“ können drei Parameter geändert werden:
- recipient = der Code, der der E-Mail-Adresse des Empfängers zugeordnet ist
Um Missbrauch zu verhindern, wird die E-Mail-Adresse im Absenderskript vorab verschlüsselt
Wenn „0“ angegeben wird, wird die Nachricht in der „temporären E-Mail“ von RealSender empfangen
- email = die E-Mail-Adresse der Person, die das Formular ausfüllt (ID=E-Mail)
Sie wird nur verwendet, wenn im Formular KEIN „E-Mail“-Feld vorhanden ist
- subject = der Betreff der E-Mail-NachrichtFordern Sie eine kostenlose Testversion an, wenn Sie die HTML-Datei online veröffentlichen möchten.
Sie erhalten dann ein ansprechendes Bestätigungs-Popup wie das unten abgebildete.
Die eingegebenen Daten werden direkt an Ihre E-Mail-Adresse gesendet.
Weitere Informationen zur Aktion dieses Monats finden Sie hier:
https://click.youremaildomain.com/s/flash.pl?promo=yesWenn Sie an der Veranstaltung teilnehmen möchten, klicken Sie bitte hier:
https://click.youremaildomain.com/s/flash.pl?event=yesUm das neue Produkt zu bestellen, klicken Sie hier:
https://click.youremaildomain.com/s/flash.pl?newproduct=yesWenn Sie die E-Mail-Adresse wie unten angegeben an das Ende des Links anhängen (
),
wird das Feld „Antwort an“ automatisch ausgefüllt, sodass die Antwort an die E-Mail-Adresse der Person gesendet wird, die auf den Link geklickt hat:
&email=name@example.comUm die „Landing Page“ festzulegen, die nach dem Absenden der Daten angezeigt wird,
fügen Sie den Parameter „rdir“ am Ende des Links hinzu, wie unten gezeigt:
&rdir=/okGeben Sie alternativ Ihre Website-Adresse an, zum Beispiel:
&rdir=www.example.com/thankyouUm zu verhindern, dass die in Ihren Mitteilungen enthaltenen Links
als „Phishing-Versuch“ eingestuft werden,
muss eine Subdomain der sendenden Domain konfiguriert werden, zum Beispiel:
click.yourmaildomain.com CNAME click.realsender.comDer Empfänger der Benachrichtigung – auch mehrere – wird im Skript festgelegt.
Bitte teilen Sie uns dies während der Konfigurationsphase mit.
In den obigen Beispielen werden Benachrichtigungen an
gesendet,
unsere temporäre E-Mail-Adresse, die unter folgender Adresse zu finden ist:
https://inxbox.realsender.com/monitor
Ein „Benutzercode“ ist ein alphanumerischer Code, den der Benutzer bei der Anmeldung an einem geschützten System eingibt.
Die RealSender-App „usercode“ generiert stündlich automatisch einen eindeutigen Benutzercode,
der auf Anfrage an die zugehörige E-Mail-Adresse gesendet wird.
Nur vorab autorisierte E-Mail-Adressen können den Benutzercode anfordern.
Die Länge und Komplexität des Benutzercodes werden bei der Systemkonfiguration festgelegt.
Hier ist beispielsweise der Inhalt der E-Mail-Nachricht, die den Benutzercode versendet:
Dein Benutzercode lautet: 665407
!! Der Benutzercode läuft stündlich um:03 abDie Integration in Ihr Sicherheitssystem ist ganz einfach:
Um die Sicherheit zu erhöhen, empfehlen wir, den „fail2ban“-Schutz zu aktivieren (
),
der Besucher nach einer bestimmten Anzahl erfolgloser Anmeldeversuche sperrt.
Sie können sich die Funktionsweise ansehen, indem Sie ein RealSender-Testkonto aktivieren.
Zusammen mit den Daten zum Versenden von E-Mails erhalten Sie Anweisungen für den Zugriff auf Ihren Benutzerbereich.
Hier ist beispielsweise der Inhalt der E-Mail mit den Anweisungen
für den Zugriff auf den RealSender-Benutzerbereich und den Webspace:
Link zu Ihrem Benutzerbereich:
https://username:usercode@rsXXX.realsender.com/reserved.area/
Link zu Ihrem Webspace:
https://username:usercode@rsXXX.realsender.com/view/
!! Die Links verfallen stündlich um :03In diesem Fall wird der Usercode in einem webbasierten Zugangssystem verwendet, das durch „Basic Auth“ geschützt ist.
Sowohl der Parameter „username“ als auch der Parameter „usercode“ werden automatisch ausgefüllt,
wodurch dem Benutzer ein einfacher und schneller Zugriff ermöglicht wird.

Der E-Mail-Proxy-Server bietet Ihnen folgende Möglichkeiten:
Hauptmerkmale:
verbessert die Sicherheit, Leistung und Skalierbarkeit Ihres SMTP-Servers
Verbinden Sie Ihre gesamte IT-Infrastruktur sofort mit zertifizierten E-Mail-Anbietern
E-Mail-Nachrichten in eine einzige Zeile komprimieren, E-Mail-Anhänge in Links umwandeln
Benachrichtigungen an die ntfy-App senden, die für Android- und iPhone-Geräte verfügbar ist
E-Mails an Mobiltelefone senden, SMS-Nachrichten in Ihrem E-Mail-Postfach empfangen und SMS-Nachrichten direkt aus Ihrem E-Mail-Postfach beantworten
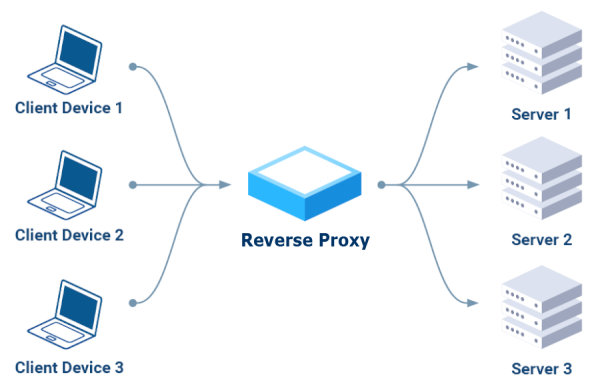
Die wichtigsten Vorteile:

Zertifizierte E-Mail ist eine E-Mail-Form, mit der der Versand und die Zustellung einer Nachricht bestätigt werden können und die Empfangsbestätigungen liefert, die gegenüber Dritten geltend gemacht werden können.
Es gibt drei Betriebsmodi, die auch kombiniert werden können, um das Versenden von E-Mail-Nachrichten per zertifizierter E-Mail zu ermöglichen:
Diese E-Mails werden an einen anderen Server weitergeleitet, der sich beim zertifizierten E-Mail-SMTP-Dienst des Kunden (wie beispielsweise Aruba, Legalmail oder Register, um nur einige zu nennen) authentifiziert.
Der Absender wird automatisch auf die zertifizierte E-Mail-Adresse des Kunden gesetzt.
Zurückgesendete Nachrichten (z. B. „Empfänger unbekannt“ oder „Postfach voll“) werden an die als Absender angegebene zertifizierte E-Mail-Adresse gesendet.
Falsche oder nicht mehr gültige E-Mail-Adressen müssen manuell korrigiert oder gelöscht werden, um einen weiteren Versand zu verhindern, da sie den Spam-Schutz in den Posteingängen der Empfänger auslösen könnten.
Die App „plainmail“ reduziert Ihre E-Mails auf eine einzige Textzeile,
sie blendet E-Mail-Anhänge aus und versendet stattdessen Links:
Fügen Sie einfach „.plain“ an die E-Mail-Domain des Empfängers an, z. B.
.
Der Empfänger erhält dann nur die Betreffzeile:
Empfänger: email@example.com.plain
Betreff: Ihre kurze Nachricht, Emoticons sind erlaubtZusätzliche E-Mail-Inhalte und Anhänge werden ignoriert,
stattdessen erscheint folgende Meldung:
< PlainMail >
All content except the subject line has been removed.Schreibe einfach „[A]“ in die Betreffzeile und füge der E-Mail einen Anhang hinzu.
Die App „plainmail“ wandelt diesen automatisch in einen Link um.
Die Domain im Link kann eine beliebige eigene Domain oder Subdomain sein, die Sie verwenden möchten.
Die Datei wird nach sechs Monaten GELÖSCHT.

ntfy (ausgesprochen „notify“) funktioniert als „Publish-Subscribe“-Benachrichtigungsdienst, bei dem Sie eine Nachricht an ein „Thema“ senden. Ein Smartphone oder Computer, auf dem die ntfy-App läuft und das bzw. der dasselbe Thema abonniert hat, erhält die Nachricht als Echtzeit-Push-Benachrichtigung.
Dadurch können sofortige Benachrichtigungen übermittelt werden, die von Skripten, Servern oder anderen Diensten generiert werden, sodass Benutzer Benachrichtigungen ohne aufwendige Konfiguration erhalten können.
Veröffentlicher:
Sie können Nachrichten zu einem Thema per E-Mail veröffentlichen, indem Sie eine E-Mail an eine bestimmte Adresse senden.
Beispielsweise können Sie eine Nachricht veröffentlichen, indem Sie eine E-Mail an topic@ntfy.youremaildomain.com senden.
Der Inhalt der Nachricht entspricht dem Betreff der E-Mail.
Nur RealSender-Benutzer sind berechtigt, E-Mails an diese Adresse zu senden
Abonnenten:
erhalten Benachrichtigungen über ihr Smartphone oder ihren Computer,
sofern die ntfy-App installiert ist und sie das gewünschte Thema abonniert haben
Themen:
Stellen Sie sich Themen als Kanäle vor, die über eindeutige Namen verfügen und in denen Ereignisströme veröffentlicht werden.
Sie müssen Themen nicht explizit erstellen; wählen Sie einfach einen Namen aus und verwenden Sie ihn.
Themennamen sind öffentlich, daher ist es ratsam, einen Namen zu wählen, der nicht leicht zu erraten ist
Nachdem die E-Mail versendet wurde, empfängt der ntfy-Server die Nachricht und speichert sie für die Abonnenten dieses Themas.
Ein Abonnent (über die ntfy-App) ist mit dem Thema verbunden und erhält die Nachricht in Echtzeit.
Es handelt sich um ein „entkoppeltes System“; Publisher müssen ihre Abonnenten nicht kennen und umgekehrt.
Dies vereinfacht die Nutzung und Verwaltung sowohl für den Publisher als auch für den Abonnenten.
Schreibe einfach „[A]“ in die Betreffzeile und füge der E-Mail einen Anhang hinzu.
Die App „plainmail“ wandelt diesen automatisch in einen Link um.
Die Domain im Link kann eine beliebige eigene Domain oder Subdomain sein, die Sie verwenden möchten.
Die Datei wird nach sechs Monaten GELÖSCHT.

Verbinden Sie Ihre E-Mails mit der mobilen Welt,
optimieren Sie Ihre geschäftlichen Kommunikationsmöglichkeiten,
ohne Ihre Arbeitsgewohnheiten zu ändern:
Push-Benachrichtigungen sind der effektivste Weg, um Ihre Kunden schnell zu erreichen.
Mit extrem hohen Öffnungsraten (bis zu 95 %) und Spitzen-Antwortraten (bis zu 45 %).
– Quelle: Gartner-Studie zu Textnachrichten, Jahr 2019
Empfänger: mobilenumber@text.yourdomain.com
Betreff: Inhalt der SMS, Emoticons sind erlaubt
(weiterer E-Mail-Inhalt und Anhänge werden ignoriert)Wir stellen Ihnen einen für Ihren Mobilfunkanbieter vorkonfigurierten Industrierouter zur Verfügung.
Die Steuerung des Versands und der Zustellung von SMS-Nachrichten muss über den jeweiligen Netzbetreiber erfolgen.
Unser System überprüft alle zehn Minuten, ob der Router reagiert (bitte überprüfen Sie die Stromversorgung und die Internetverbindung).
Um Missbrauch zu vermeiden, müssen Nachrichten über RealSender unter Verwendung vorab autorisierter Absender gesendet werden,
mit „strenger“ SPF- und DKIM-Konformität. Erfahren Sie mehr über E-Mail-Authentifizierung – Fortgeschrittene.
Die SMS-Antworten werden direkt an Ihre bevorzugte E-Mail-Adresse
gesendet,
zusammen mit einer E-Mail-Nachricht wie dieser:
Betreff: SMS (+41790000000)
Nachfolgend finden Sie die empfangene SMS. Sie wurde von
(+41790000000) am Montag, 29. Juli 2025 um 10:57:00 Uhr MESZ übermittelt
---------------------------------------------------------------------------
Testnachricht
---------------------------------------------------------------------------Mit der „plainmail“-App von RealSender kannst du Textnachrichten direkt aus deiner E-Mail heraus versenden.
So können Sie direkt aus Ihrer bevorzugten E-Mail-Anwendung antworten.
Die Empfängeradresse ist bereits mit der Nummer des ursprünglichen Absenders ausgefüllt:
Empfänger: mobilenumber@text.yourdomain.com
Betreff: der Inhalt der Antwort
(weiterer E-Mail-Inhalt und Anhänge werden ignoriert)Die Kommunikation zwischen E-Mail-Programm und Mobilgerät kann somit fortgesetzt werden.
Schreibe einfach „[A]“ in die Betreffzeile und füge der E-Mail einen Anhang hinzu.
Die App „plainmail“ wandelt diesen automatisch in einen Link um.
Die Domain im Link kann eine beliebige eigene Domain oder Subdomain sein, die Sie verwenden möchten.
Die Datei wird nach sechs Monaten automatisch gelöscht.

Themen in diesem Bereich:
Unsere Geschichte und unsere Aufgabe
So erreichen Sie uns bei geschäftlichen oder technischen Fragen
Pläne für einen einzelnen dedizierten SMTP-Server oder mehrere dedizierte SMTP-Server
Richtlinien gegen Spam und weitere Informationen zum Service
was wir Ihnen nicht bieten können
Wie gehen wir mit dem Datenschutz um?
Erläuterung der Fachbegriffe

Nachdem wir von 2006 bis 2009 über ein Jahrzehnt lang
– eine deutsche E-Mail-Marketing-Plattform – vertrieben hatten,
wussten wir, wie wichtig die Reputation des SMTP-Servers ist.
Es gab nur einen Weg, dies zu gewährleisten:
einen dedizierten SMTP-Server mit eigener IP-Adresse für jeden Kunden.
Dies war unser erster Schritt auf dem Weg zur Bereitstellung innovativer Lösungen,
in einer zuverlässigen, ständig überwachten Umgebung.
Unsere Aufgabe ist es: „um Ihre E-Mails wirkungsvoller zu gestalten“.
Wir arbeiten jeden Tag hart dafür.
bietet Ihnen volle Kontrolle und Transparenz über Ihre ausgehenden E-Mails,
damit die Empfänger Ihre Nachrichten erhalten und ihnen vertrauen.

Bei geschäftlichen oder technischen Fragen:
E-Mail: contact@mx.realsender.com
Telefon: +41 61 5000365
SMS: +41 79 6276163
Unser Büro ist montags bis freitags von 9:00 bis 19:00 Uhr (MEZ) geöffnet.
So erreichen Sie uns:
Umsatzsteuer-Identifikationsnummer: IT02457460125
 |
RealSender – ein dedizierter SMTP-Server , der bis zu 10.000 E-Mails pro Woche versenden kann (wird in der Regel für 1:1-E-Mails und Transaktions-E-Mails verwendet) |
 |
HighSender – ein E-Mail-Gateway zu mehreren dedizierten SMTP-Servern – leitet E-Mails über 2 bis 100 Server weiter, wobei die Last automatisch verteilt wird – kann bis zu 1.000.000 E-Mails pro Woche versenden (wird in der Regel für Newsletter und Massenversendungen genutzt) |
Für Dienste, die als „Apps“ bezeichnet werden, fallen zusätzliche Kosten an. Bitte kontaktieren Sie uns für weitere Informationen. |
Völlig kostenlose, unverbindliche Testphase
90 Tage Geld-zurück-Garantie nach dem Kauf
“ beginnen |
(GB) |
(€ gilt nur für die EU) |
“ (E-Mails, die versendet werden können) |
|
|---|---|---|---|---|
| RealSender 100x3 | 100 | 9 | 990 $/€ | bis zu 30.000 |
| RealSender 50x2 | 50 | 6 | 590 $/€ | bis zu 20.000 |
| RealSender 25 | 25 | 3 | 390 $/€ | bis zu 10.000 |
| RealSender 10 | 10 | 2 | 240 $/€ | bis zu 6.000 |
| RealSender 5 | 5 | 0.5 | 190 $/€ | bis zu 2.000 |
Das wöchentliche Limit kann geringer ausfallen, falls es zu Problemen bei der Zustellung kommt
Benötigen Sie mehr Absender-E-Mail-Adressen oder mehr Traffic? Bitte kontaktieren Sie uns
x3 = Die Nachrichten werden über drei dedizierte SMTP-Server in zwei verschiedenen Rechenzentren versendet:
Sollte einer ausfallen oder nicht erreichbar sein, leiten die beiden anderen Ihre Nachrichten weiter
x2 = Die Nachrichten werden über zwei dedizierte SMTP-Server in verschiedenen Rechenzentren versendet:
Sollte einer ausfallen oder nicht erreichbar sein, übernimmt der andere die Weiterleitung Ihrer Nachrichten
1 GB Datenverkehr entsteht durch den Versand von ca. 10.000 E-Mails mit einer Größe von jeweils 100 KB
Für „Absenderadressen“ und „wöchentlichen Datenverkehr“ gilt eine Toleranzgrenze von +20 %
Bei Überschreitung des Limits werden Sie kontaktiert, um ein Upgrade durchzuführen
RealSender verfolgt eine Null-Toleranz-Politik gegenüber SPAM (unerwünschte Werbe-E-Mails)
Kunden, die unaufgeforderte kommerzielle E-Mails oder verbotene Werbung
oder andere belästigende oder illegale Inhalte per E-Mail versenden,
müssen mit einer sofortigen Kündigung ihres Kontos ohne Rückerstattung rechnen
Völlig kostenlose, unverbindliche Testphase
90 Tage Geld-zurück-Garantie nach dem Kauf
“ beginnen |
(GB) |
“ (E-Mails, die versendet werden können) |
||
|---|---|---|---|---|
| HighSender 4 | k. A. | 8 | Kontaktieren Sie uns für ein Angebot | bis zu 40.000 |
| HighSender 3 | k. A. | 6 | Kontaktieren Sie uns für ein Angebot | bis zu 30.000 |
| HighSender 2 | k. A. | 4 | Kontaktieren Sie uns für ein Angebot | bis zu 20.000 |
Das wöchentliche Limit kann niedriger ausfallen, falls es zu Lieferproblemen kommt
Benötigen Sie ein höheres wöchentliches Limit? Bitte kontaktieren Sie uns
1 GB Datenverkehr entsteht durch den Versand von ca. 10.000 E-Mails à 100 KB
Für den „wöchentlichen Datenverkehr“ gilt eine Toleranzgrenze von +20 %
Bei Überschreitung des Limits werden Sie kontaktiert, um ein Upgrade durchzuführen
k. A.: In der Regel wird nur eine „Absenderadresse“ verwendet; bitte fragen Sie nach, falls Sie weitere benötigen
RealSender verfolgt eine Null-Toleranz-Politik gegenüber SPAM (unerwünschte Werbe-E-Mails)
Kunden, die unaufgeforderte kommerzielle E-Mails oder verbotene Werbung
oder andere belästigende oder illegale Inhalte per E-Mail versenden,
müssen mit einer sofortigen Kündigung ihres Kontos ohne Rückerstattung rechnen
RealSender verfolgt eine Null-Toleranz-Politik gegenüber SPAM (unerwünschte Werbe-E-Mails). Kunden, die unaufgeforderte kommerzielle E-Mails, verbotene Werbung oder andere belästigende oder illegale Inhalte per E-Mail versenden, müssen mit einer sofortigen Kündigung ihres Kontos ohne Rückerstattung rechnen. Wiederholte Sendungen an falsche Empfänger und die Nichteinhaltung des wöchentlichen Limits gelten als „Spammer-Verhalten“.
Die „Absenderadressen“ für jedes RealSender-Konto müssen unter einem oder mehreren Domainnamen liegen, die von demselben Unternehmen registriert wurden. Jeder Server kann bis zu 10.000 E-Mails pro Woche versenden. Die Anzahl der Empfänger pro E-Mail ist auf 100 begrenzt. Der RealSender-Dienst ist ausschließlich für geschäftliche Zwecke bestimmt: Es sind sowohl eine vollständige Postanschrift als auch eine Steuernummer erforderlich.
RealSender leitet die E-Mails lediglich weiter und überprüft deren Inhalt weder in rechtlicher noch in sachlicher oder sonstiger Hinsicht. RealSender übernimmt zudem keine Verantwortung für den Inhalt der von ihm weitergeleiteten E-Mails.
Der Kunde verpflichtet sich, RealSender von jeglicher Haftung für jegliche Nutzung seines Kontos freizustellen. Darüber hinaus verpflichtet sich der Kunde, RealSender von allen Ansprüchen und Aufwendungen, einschließlich angemessener Anwaltskosten, freizustellen und schadlos zu halten, die sich aus einem Verstoß des Kunden gegen die Dienstleistungsvereinbarung oder aus einem direkten oder indirekten Schaden ergeben, den der Kunde einer anderen Partei zugefügt hat.
Der Kunde erklärt sich ausdrücklich damit einverstanden, dass die Nutzung des Dienstes von RealSender auf sein alleiniges Risiko erfolgt. Weder RealSender noch seine Informationsanbieter, Lizenzgeber, Mitarbeiter oder Beauftragten garantieren, dass der Dienst unterbrechungsfrei oder fehlerfrei ist; ebenso wenig übernehmen RealSender oder seine Informationsanbieter, Lizenzgeber, Mitarbeiter oder Beauftragten eine Gewährleistung hinsichtlich der Ergebnisse, die durch die Nutzung des Dienstes erzielt werden. Der Dienst wird „wie besehen“ ohne jegliche ausdrückliche oder stillschweigende Gewährleistung bereitgestellt, einschließlich, aber nicht beschränkt auf Gewährleistungen hinsichtlich des Eigentumsrechts oder stillschweigende Gewährleistungen der Marktgängigkeit oder Eignung für einen bestimmten Zweck oder anderweitig, mit Ausnahme jener Gewährleistungen, die sich aus den für diese Dienstleistungsvereinbarung geltenden Gesetzen ergeben und die nicht ausgeschlossen, eingeschränkt oder geändert werden können. Weder RealSender noch andere an der Erstellung, Produktion oder Bereitstellung des Dienstes beteiligte Personen haften für direkte, indirekte, zufällige, besondere oder Folgeschäden, die sich aus der Nutzung des Dienstes, der Unmöglichkeit der Nutzung des Dienstes oder aus einer Verletzung einer Gewährleistung ergeben. Der Kunde erkennt ausdrücklich an, dass die Bestimmungen dieses Absatzes auch für alle Inhalte Dritter und alle anderen über den Dienst verfügbaren Inhalte gelten.
Nach schriftlicher, per Fax oder per E-Mail an den Kunden übermittelter Mitteilung ist RealSender berechtigt, diesen Dienstleistungsvertrag oder die Preise zu ändern sowie nach eigenem Ermessen ohne vorherige Ankündigung einzelne oder alle Aspekte der Dienstleistung einzustellen oder anzupassen.
RealSender und Inxbox sind in der EU eingetragene Marken.
Für jeden Kunden wird ein eigener SMTP-Server eingerichtet, optimiert und rund um die Uhr in Betrieb gehalten.
Dies ist mit minimalen Kosten verbunden, die Sie in gemeinsam genutzten SMTP-Umgebungen nicht finden werden,
die hingegen nur sehr wenige Garantien bieten und für ihre Nutzer mit hohen Risiken verbunden sind.
Wir haben keinen Einfluss auf den Inhalt der versendeten Nachrichten; diese können dazu führen, dass sie im Spam- oder Junk-Ordner landen.
Einige Freemail-Anbieter leiten Nachrichten von unbekannten Absendern standardmäßig in den Spam-Ordner weiter.
Ihr Antispam-System lernt daraus, wie ihre Nutzer mit den empfangenen Nachrichten umgehen.
Wenn der einzelne Empfänger die empfangene E-Mail einmal als KEINEN Spam markiert, lernt das System, dass es sich um gültige Nachrichten handelt
und beginnt, sie in den Ordner „Posteingang“ statt in den „Spam“-Ordner zu leiten.
Alternativ muss der Absender im Adressbuch des Empfängers stehen oder zuvor E-Mails ausgetauscht haben.
Unsere technischen Mitarbeiter helfen Ihnen dabei, diese Fälle zu identifizieren und eine effektive Zustellstrategie zu implementieren.
RealSender leitet die E-Mails lediglich im Auftrag seiner Kunden weiter und überwacht oder archiviert deren Inhalt nicht.
Wir speichern die Protokolle der letzten 7 Tage sowie die Statistiken zum generierten Datenverkehr, die den Kunden wie hier beschrieben zur Verfügung stehen:
Protokolle & Zustellungs
Statistiken
Die Nutzung des Dienstes setzt voraus, dass unsere Kunden die Nutzungsbedingungen akzeptieren.
Im Falle von Missbrauch können wir dank des automatischen Überwachungssystems für Sperrlisten schnell reagieren.
Auf allen Startseiten unserer Server ist die E-Mail-Adresse angegeben, an die unerwünschte Werbe-E-Mails unserer Kunden gemeldet werden können: [abuse@realsender.com] (mailto: abuse@realsender.com)
Sie können den Datenschutzbeauftragten über dieses Formular erreichen.
Closed-Loop-Marketing
Der Prozess, durch den Kundendaten in Ihre Marketingkampagnen einfließen und die Umsatzleistung steigern können.
DomainKeys Identified Mail (DKIM)
DKIM ist ein E-Mail-Authentifizierungsprotokoll, das es dem Absender ermöglicht, ausgehende E-Mails mithilfe von Public-Key-Kryptografie so zu signieren, dass dies vom Empfänger überprüft werden kann. Die DKIM-Spezifikation basiert auf den früheren Protokollen Domain Keys und Identified Internet Mail. DKIM ist in IETF RFC 4871 definiert. Der DKIM-Standard wird bereits von Gmail und anderen großen Unternehmen eingesetzt, um Phishing und Spoofing aus dem E-Mail-Verkehr vollständig zu eliminieren.
E-Mail-Authentifizierung Eine Technologie, die überprüft, ob eine E-Mail-Nachricht tatsächlich von der Domain stammt, von der sie angeblich gesendet wurde [2]. Die Überprüfung der Identität einer E-Mail ist zu einem entscheidenden ersten Schritt geworden, um Spam, Fälschungen, Betrug und sogar schwerwiegendere Straftaten zu verhindern. [3]
Internet Engineering Task Force (IETF)
Die Internet Engineering Task Force ist eine große, offene internationale Gemeinschaft aus Netzwerkentwicklern, Betreibern, Anbietern und Forschern, die sich mit der Weiterentwicklung der Internetarchitektur und dem reibungslosen Betrieb des Internets befassen. Sie steht allen Interessierten offen. Das Ziel der IETF ist es, das Internet besser funktionieren zu lassen.
Message Transfer Agent (MTA)
Jedes System, auf dem SMTP-Routing-Software läuft, das eine Nachricht entgegennehmen, verarbeiten, Zielinformationen im DNS (oder einer anderen Routing-Tabelle) nachschlagen und an das vorgesehene Empfängersystem zustellen kann. MTAs sind in der Regel Serveranwendungen wie Sendmail, Microsoft Exchange, Postfix, Lotus Domino, qmail, PowerMTA usw.
Secure SMTP
Erweiterung des SMTP-Dienstes, die es einem SMTP-Server und einem SMTP-Client ermöglicht, TLS (Transport Layer Security) zu nutzen, um eine vertrauliche, authentifizierte Kommunikation über das Internet zu gewährleisten. [1]
Sender Policy Framework (SPF)
SPF ist ein pfadbasiertes E-Mail-Authentifizierungsprotokoll, das es E-Mail-Empfängern ermöglicht, festzustellen, ob der Absender zur Nutzung der in der Kopfzeile der Nachricht angegebenen Domains berechtigt ist, indem die IP-Adresse des ausgehenden MTA des Absenders anhand der vom Absender in DNS-TXT-Einträgen veröffentlichten Informationen überprüft wird. SPF ist in IETF RFC 4408 definiert.
Das Simple Mail Transfer Protocol (SMTP)
ist ein Internetstandard für die Übertragung von elektronischer Post (E-Mail) über IP-Netzwerke. SMTP wurde erstmals von Jonathan Postel in IETF RFC 821 (1982) definiert und zuletzt durch IETF RFC 5321 (2008) aktualisiert, das die Erweiterungen des Extended SMTP (ESMTP) enthält; es ist das heute weit verbreitete Protokoll. SMTP ist für den Transport ausgehender E-Mails vorgesehen und nutzt Port 25.
Transport Layer Security (TLS)
Das TLS-Protokoll gewährleistet die Sicherheit der Kommunikation über das Internet. Das Protokoll ermöglicht es Client-Server-Anwendungen, auf eine Weise zu kommunizieren, die darauf ausgelegt ist, das Abhören, die Manipulation oder die Fälschung von Nachrichten zu verhindern. TLS ist ein Protokoll im IETF-Standardisierungsprozess, das zuletzt in RFC 5246 aktualisiert wurde.
[1] RFC 3207 – SMTP-Dienst-Erweiterung für sicheres SMTP über Transport Layer Security
[2] OTA-Bericht zum Stand der E-Mail-Authentifizierung 2008
[3] E-Mail-Authentifizierung von David MacQuigg

Themen in diesem Bereich:
die erforderlichen Mindesteinstellungen
Erhalten Sie die volle Kontrolle über den Ruf Ihrer E-Mails
Bestimmen Sie selbst, was mit Ihren E-Mails geschieht
überprüft alle zehn Minuten automatisch die ordnungsgemäße Funktion der Dienste
Themen in diesem Bereich:
Einführung in das Sender Policy Framework
Überprüfen Sie Ihre SPF-Einstellungen für E-Mails, indem Sie eine E-Mail senden
Einführung in DomainKeys Identified Mail
Überprüfen Sie Ihre DKIM-Einstellungen für E-Mails, indem Sie eine E-Mail senden

SPF ist die Abkürzung für „Sender Policy Framework“, einen Standard zur E-Mail-Authentifizierung (
),
mit dem Sie festlegen können, welche SMTP-Server zum Versenden von E-Mails für Ihre Domain berechtigt sind.
Damit können Sie die Absenderadresse und deren Verbindung zu dem Server, der die Nachricht versendet hat, überprüfen.
Wenn E-Mails über Ihre Absenderdomain versendet werden, kann der Empfänger feststellen, ob sie von einem SMTP-Server stammen, den Sie kennen.
Es wird empfohlen, dies zu konfigurieren, da einige Empfänger Ihre Nachrichten möglicherweise ablehnen, wenn SPF gar nicht eingerichtet ist.
Es gibt zwei verschiedene Ansätze:
Die „sanfte“ Konfiguration führt zu weniger oder gar keinen Ablehnungen seitens der Empfänger.
Die „harte“ Konfiguration führt dazu, dass einige Nachrichten abgelehnt werden, wenn der Server nicht angegeben wurde oder in manchen Fällen, wenn die E-Mail weitergeleitet oder über eine Mailingliste versendet wurde.
Die „harte“ Konfiguration gibt dem Ziel-Mailserver mehr Spielraum bei der Entscheidung, ob die Nachricht angenommen wird oder nicht; dies ist der von uns empfohlene Ansatz.
Für die SPF-Konfiguration muss genau bekannt sein, welche Server Sie zum Versenden von E-Mails verwenden.
Bei RealSender sollte der TXT-Eintrag Ihrer Domain (example.com) die Zeichenfolge
a:example.realsender.com enthalten und wie folgt aussehen:
example.com TXT "v=spf1 a:example.realsender.com ~all" Bei HighSender sollte der TXT-Eintrag Ihrer Domain (example.com) die Zeichenfolge „
include:spf.realsender.com“ enthalten und wie folgt aussehen:
example.com TXT "v=spf1 include:spf.realsender.com ~all" Diese Tools helfen Ihnen bei der Überprüfung der Konfiguration:
www.kitterman.com/spf/validate.html *
ruft SPF-Einträge für den angegebenen Domainnamen ab und prüft, ob der Eintrag gültig ist
spf check online
überprüft Ihre E-Mail-SPF-Einstellungen durch das Versenden einer E-Mail-Nachricht
* = Link zu einer externen Website, wird in einem neuen Fenster geöffnet
Selbst wenn alles korrekt eingerichtet ist, kann die Nachrichtenüberprüfung unter
fehlschlagen,
wenn die E-Mail weitergeleitet oder über eine Mailingliste versendet wurde.
In these cases, to keep the email authentication consistent,
configure the dkim signature domain to be aligned with the sender’s From address.
See: email authentication advanced » <dkim> alignment for dmarc.

spf@tester.realsender.comhttps://tester.realsender.com/spfDer RealSender-SPF-Check online fügt ein Präfix zum Betreff hinzu, wenn die Nachricht nicht ordnungsgemäß authentifiziert wurde:
!! spf-fail !! Der SMTP-Server ist nicht unter den autorisierten Servern aufgeführt
und die E-Mail sollte abgelehnt oder verworfen werden
!! spf-softfail !! Der SMTP-Server ist nicht unter den autorisierten Servern aufgeführt
dieser Fall sollte jedoch als „Softfail“ behandelt werden
!! spf-neutral !! Der SPF-Eintrag gibt ausdrücklich an, dass keine Aussage über die Gültigkeit getroffen werden kann
!! spf-none !! Die Absenderdomain enthält keine Informationen zur Authentifizierung der E-Mail Manchmal sind die auf Domänenebene gespeicherten Informationen nicht korrekt oder nicht verständlich.
!! spf-permerror !! Es ist ein dauerhafter Fehler aufgetreten (z. B. ein falsch formatierter SPF-Eintrag)
!! spf-temperror !! Es ist ein vorübergehender Fehler aufgetretenDie SPF-Prüfung erfolgt anhand der „Mail-From“-E-Mail-Adresse, die in den E-Mail-Headern verborgen ist.
Sichtbar ist lediglich die „From“-E-Mail-Adresse. Wenn sich die Stammdomänen unterscheiden, wird folgende Warnung angezeigt:
!! spf-diff !! Die Stammdomänen von „Mail-From“ und „From“ sind unterschiedlichWenn die Nachricht sowohl die SPF-Prüfung als auch die SPF-Alignment-Prüfung für DMARC (Relaxed Alignment) besteht, erhalten Sie folgende Meldung:
|OK| spf-pass Ihre E-Mail besteht die SPF-Prüfung + die SPF-AbgleichprüfungWenn nur eines von beiden, SPF ODER DKIM, die Übereinstimmungsprüfung für DMARC (gelockerte Übereinstimmung) besteht,
wird die Nachricht dennoch als „OK“ (vertrauenswürdig) eingestuft und das Tilde-Zeichen (~) am Anfang hinzugefügt:
|~OK| spf-pass Ihre E-Mail besteht die SPF-Prüfung (nicht die DKIM-Prüfung) + DKIM-Prüfung
DKIM ist die Abkürzung für „DomainKeys Identified Mail“, einen Standard zur E-Mail-Authentifizierung (
),
der sicherstellen soll, dass die E-Mail (einschließlich der Anhänge) seit dem Anbringen der „Signatur“ nicht verändert wurde.
Dies geschieht, indem jeder ausgehenden E-Mail-Nachricht eine digitale Signatur hinzugefügt wird, die mit einem Domainnamen verknüpft ist.
Es werden zwei Schlüssel verwendet: ein „öffentlicher“ und ein „privater“ Schlüssel:
Beim Versenden einer Nachricht generiert der SMTP-Server eine „verschlüsselte Hash-Signatur“, die auf dem Inhalt der E-Mail-Nachricht und dem privaten Schlüssel basiert.
Das Empfängersystem kann die Signatur im E-Mail-Header überprüfen, indem es sie mit dem E-Mail-Inhalt und dem „öffentlichen“ Schlüssel des Absenders abgleicht.
DKIM-Signaturen sind für Endnutzer nicht unmittelbar sichtbar; sie werden von der E-Mail-Infrastruktur hinzugefügt und überprüft.
Die SMTP-Server von RealSender signieren alle ausgehenden E-Mail-Nachrichten mit einer DKIM-Signatur.
RealSender versieht zunächst alle ausgehenden Nachrichten mit seiner eigenen, mit dem SMTP-Server verbundenen Domain,
.
Auf Seiten der Benutzer oder Administratoren ist keine Konfiguration erforderlich.
Um die„DKIM-Domänenabgleichung für DMARC“zu erhalten,
muss die Nachricht mit derselben Domäne wie die des Absenders signiert sein.
Bei RealSender sollten Sie in den DNS-Einstellungen Ihrer Domain (beispiel.com) zwei CNAME-Einträge
hinzufügen, und zwar wie folgt:
key1._domainkey.example.com CNAME key1._domainkey.yourcompany.realsender.com
key2._domainkey.example.com CNAME key2._domainkey.yourcompany.realsender.comDieses Tool hilft Ihnen bei der Überprüfung der Konfiguration:
toolbox.googleapps.com *
* = Link zu einer externen Website, wird in einem neuen Fenster geöffnet
Eine mit DKIM signierte Nachricht kann nicht verändert werden, ist aber dennoch für jeden lesbar.
Eine signierte Nachricht, die die Überprüfung nicht besteht, wird in der Regel abgelehnt.
Wenn auf dem Weg vom Absender zum Empfänger keine Änderungen vorgenommen wurden, sollte dies nicht passieren.
Es sind uns seltene Fälle bekannt, die alle mit der Zeilenlänge zusammenhängen (diese darf maximal 990 Zeichen betragen).
Manche Anwendungen senden den Inhalt in einer einzigen Zeile oder übertragen eine sehr lange Zeile innerhalb des HTML-Codes.
In diesen Fällen wird die DKIM-Signatur beschädigt, was zu dem Prüfergebnis „dkim=fail“ führt.

dkim@tester.realsender.comhttps://tester.realsender.com/dkimDer RealSender-DKIM-Check online fügt ein Betreff-Präfix hinzu, wenn die Nachricht nicht korrekt signiert wurde:
!! dkim-none !! Es wurden keine DKIM-Signature-Header (weder gültige noch ungültige) gefunden
!! dkim-fail !! Es wurde ein gültiger DKIM-Signature-Header gefunden, aber die Signatur
enthält keinen korrekten Wert für die Nachricht Manchmal ist es nicht möglich, die Überprüfung durchzuführen:
!! dkim-invalid !! Es liegt ein Problem mit der Signatur selbst oder dem Eintrag des öffentlichen Schlüssels vor.
Das heißt, die Signatur konnte nicht verarbeitet werden.
!! dkim-temperror !! Es wurde ein Fehler festgestellt, der wahrscheinlich nur vorübergehender Natur ist,
wie beispielsweise eine vorübergehende Unmöglichkeit, einen öffentlichen Schlüssel abzurufen.Wenn die Nachricht mit einer anderen Domain signiert wurde, wird dem Betreff ein „diff“-Hinweis hinzugefügt.
Diese Warnung wird NICHT angezeigt, wenn der Absender die SPF-Prüfung und die SPF-Übereinstimmung für DMARC besteht:
!! dkim-diff !! Die Nachricht wurde NICHT von der Domain des Absenders signiertWenn die Nachricht sowohl die DKIM-Prüfung als auch die DKIM-Übereinstimmungsprüfung für DMARC (gelockerte Übereinstimmung) besteht, erhalten Sie folgende Meldung:
|OK| dkim-pass Ihre E-Mail besteht die DKIM-Prüfung + die DKIM-AusrichtungsprüfungWenn nur eines von DKIM oder SPF die Übereinstimmungsprüfung für DMARC (gelockerte Übereinstimmung) besteht,
wird die Nachricht dennoch als „OK“ (vertrauenswürdig) eingestuft und das Tilde-Zeichen (~) am Anfang hinzugefügt:
|~OK| dkim-pass Ihre E-Mail besteht die DKIM-Prüfung (nicht die Übereinstimmung) + SPF-ÜbereinstimmungsprüfungThemen in diesem Bereich:
Nicht übereinstimmende SPF-Domains können dazu führen, dass die DMARC-Prüfung fehlschlägt
Nicht übereinstimmende DKIM-Domänen können dazu führen, dass die DMARC-Prüfung fehlschlägt
Domänenbasierte Nachrichtenauthentifizierung, Berichterstattung und Konformität
Online-Erfassung von RUA-Nachrichten und Erstellung täglicher DMARC-Berichte

DMARC ist ein Standard zur E-Mail-Authentifizierung, der entwickelt wurde, um gefälschte E-Mails mit gefälschten Domainnamen zu bekämpfen.
Für die Domain-Abgleichung sind folgende Voraussetzungen erforderlich:
Wenn ein Absender seine E-Mail mittels SPF und/oder DKIM authentifiziert,
muss mindestens eine der Domains mit der Absender-Domain übereinstimmenUm dies im Rahmen des SPF (Sender Policy Framework) zu erreichen, müssen Sie sich mit zwei Domänen befassen:
DMARC unterstützt zwei Arten der SPF-Anpassung: die lockere Anpassung und die strenge Anpassung.
Wenn Sie keine strenge Anpassung festlegen, wird standardmäßig die lockere Anpassung angenommen.
Bei einer lockeren Übereinstimmung muss lediglich die Stammdomain der „Mail-From“-Adresse mit der Stammdomain der „From“-Adresse übereinstimmen.
Durch die lockere Übereinstimmung können beliebige Subdomains verwendet werden, ohne dass die Anforderung an die Domain-Übereinstimmung verletzt wird.
Beispiel:
Wenn Ihre „Mail-From“-Domain „mail.abc.com“ und Ihre „From“-Domain „abc.com“ lautet,
wird Ihre E-Mail die SPF-Prüfung bestehen (die Stammdomains „abc.com“ stimmen überein)
Wenn Ihre „Mail-From“-Domain „abc.mail.com“ und Ihre „From“-Domain „abc.com“ lautet,
wird Ihre E-Mail die SPF-Prüfung NICHT bestehen (die Stammdomains „mail.com“ und „abc.com“ stimmen nicht überein)
Bei strikter Übereinstimmung muss die Domäne der „Mail-From“-Adresse exakt mit der Domäne der „From“-Adresse übereinstimmen.
Beispiel:
Wenn Ihre „Mail-From“-Domain „mail.abc.com“ lautet und Ihre „From“-Domain ebenfalls „mail.abc.com“ ist,
wird Ihre E-Mail die SPF-Prüfung bestehen (die Domains „mail.abc.com“ stimmen überein)
Wenn Ihre „Mail-From“-Domain „mail.abc.com“ und Ihre „From“-Domain „abc.com“ lautet,
wird Ihre E-Mail die SPF-Prüfung NICHT bestehen (die Domains „mail.abc.com“ und „abc.com“ stimmen nicht überein)

DMARC ist ein Standard zur E-Mail-Authentifizierung, der entwickelt wurde, um gefälschte E-Mails mit gefälschten Domänen zu bekämpfen.
In Bezug auf die Domänenabgleichung sind folgende Anforderungen zu erfüllen:
Wenn ein Absender seine E-Mail mittels SPF und/oder DKIM authentifiziert,
muss mindestens eine der Domains mit der Absender-Domain übereinstimmenDamit dies im Rahmen von DKIM (DomainKeys Identified Mail) funktioniert,
muss die DKIM-Signaturdomäne (DKIM-Signature: d=…) mit der Absenderdomäne übereinstimmen.
DMARC unterstützt zwei Arten der DKIM-Anpassung: die lockere Anpassung und die strenge Anpassung.
Wenn Sie keine strenge Anpassung festlegen, wird standardmäßig die lockere Anpassung angenommen.
Bei einer lockeren Zuordnung muss lediglich die Stammdomain der DKIM-Signaturdomain mit der Absenderdomain übereinstimmen.
Dank der lockeren Zuordnung kann jede beliebige Subdomain verwendet werden, ohne dass die Anforderungen an die Domain-Zuordnung verfehlt werden.
Beispiel:
Wenn Ihre DKIM-Signaturdomäne „mail.abc.com“ lautet und Ihre Absenderdomäne „abc.com“,
wird Ihre E-Mail die DKIM-Überprüfung bestehen (die Stammdomänen „abc.com“ stimmen überein).
Wenn Ihre DKIM-Signatur „abc.mail.com“ lautet und Ihre „From“-Domain „abc.com“ ist,
wird Ihre E-Mail die DKIM-Überprüfung NICHT bestehen (die Stammdomains „mail.com“ und „abc.com“ stimmen nicht überein)
Bei strikter Übereinstimmung muss die DKIM-Signaturdomäne exakt mit der Domäne der Absenderadresse übereinstimmen.
Beispiel:
Wenn Ihre DKIM-Signaturdomäne „mail.abc.com“ lautet und Ihre Absenderdomäne „mail.abc.com“ ist,
wird Ihre E-Mail die DKIM-Überprüfung bestehen (die Domänen „mail.abc.com“ stimmen überein)
Wenn Ihre DKIM-Signaturdomäne „mail.abc.com“ lautet und Ihre Absenderdomäne „abc.com“,
wird Ihre E-Mail die DKIM-Überprüfung NICHT bestehen (die Domänen „mail.abc.com“ und „abc.com“ stimmen nicht überein)

DMARC steht für: Domain-based Message Authentication, Reporting and Conformance.
Es handelt sich um einen Standard zur E-Mail-Authentifizierung, der entwickelt wurde, um gefälschte E-Mails mit gefälschten Domänen zu bekämpfen.
Absender:
Empfänger:
Bei einigen E-Mail-Anbietern hat dies einen erheblichen Einfluss auf die Zustellbarkeit, siehe:
So funktioniert DMARC mit Gmail und Office 365 im Jahr 2020 *
„Office 365 reagiert im Allgemeinen auf SPF- und DKIM-Authentifizierung.
Der einzige Weg, um konsistente Ergebnisse zu erzielen und den Posteingang zu erreichen, besteht darin, diese mit DMARC zu verknüpfen.“
* = Link zu einer externen Website, wird in einem neuen Fenster geöffnet
DMARC nutzt die Protokolle SPF (Sender Policy Framework) und DKIM (Domain Keys Identified Mail)
, um Situationen zu regeln, in denen E-Mails die Authentifizierungstests nicht bestehen.
SPF verlangt, dass Sie angeben, welche Server Sie zum Versenden von E-Mails verwenden.
Lesen Sie nach, wie Sie SPF konfigurieren, um mehr darüber zu erfahren und es richtig einzurichten.
Die SMTP-Server von RealSender signieren alle ausgehenden E-Mail-Nachrichten mit einer DKIM-Signatur.
Wenn Sie mit derselben Domain wie der Absender signieren möchten, ist eine entsprechende Konfiguration erforderlich.
Weitere Informationen finden Sie in der Anleitung zur Konfiguration von DKIM.
RealSender stellt Ihnen ein Postfach zur Verfügung, in dem die von den Empfängern generierten DMARC-Berichte gesammelt werden.
_dmarc.example.com. IN TXT „v=DMARC1; p=none; rua=mailto:dmarc.example@rsbox.com“Ab dem nächsten Tag erhalten Sie die DMARC-RUAs-Berichte online.
Möglicherweise stellen Sie fest, dass Sie vergessen haben, eine E-Mail-Kampagne zu authentifizieren, die von einem Drittanbieter versendet wird.
Sollte dies der Fall sein, authentifizieren Sie die Kampagne einfach und überprüfen Sie, ob der nächste Versand die DMARC-Tests besteht.
Wenn die Berichte über einige Wochen hinweg korrekt sind, weisen Sie die E-Mail-Anbieter an, diese gefälschten oder Phishing-E-Mails zurückzuweisen bzw. zu blockieren.
Der _dmarc-TXT-Eintrag Ihrer Domain sollte wie folgt geändert werden:
"v=DMARC1; p=reject; rua=mailto:dmarc.example@rsbox.com"Falls Ihr Unternehmen DMARC einsetzt, sollten Sie die Seite
sorgfältig prüfen,
bevor Sie eine neue Methode zum Versenden von E-Mails einführen.
Dmarc wendet strenge Richtlinien für die Überprüfung von SPF und DKIM an
Dies kann dazu führen, dass E-Mails, die diese Tests ansonsten bestehen würden
von E-Mail-Anbietern abgelehnt werden.
Selbst wenn alles korrekt eingestellt ist, kann die Überprüfung fehlschlagen:

RealSender erfasst und analysiert die DMARC-RUA(*)-Berichte für Sie.
* = Bedeutung von „rua“:
Meldungs-URI(s) für aggregierte Daten. In RealSender ist die „rua“ die E-Mail-Adresse, die den Kunden zur Verfügung gestellt wird:
.
An diese Adresse werden Sammelberichte von Domains gesendet:
,
die E-Mails erhalten haben, die angeblich von Ihrer Domain stammen.
Die Berichte werden täglich um 13:00 Uhr (MEZ) erstellt und enthalten die Daten der letzten sieben Tage.
Dies ist ein DMARC-Online-Bericht, Beispielseite:
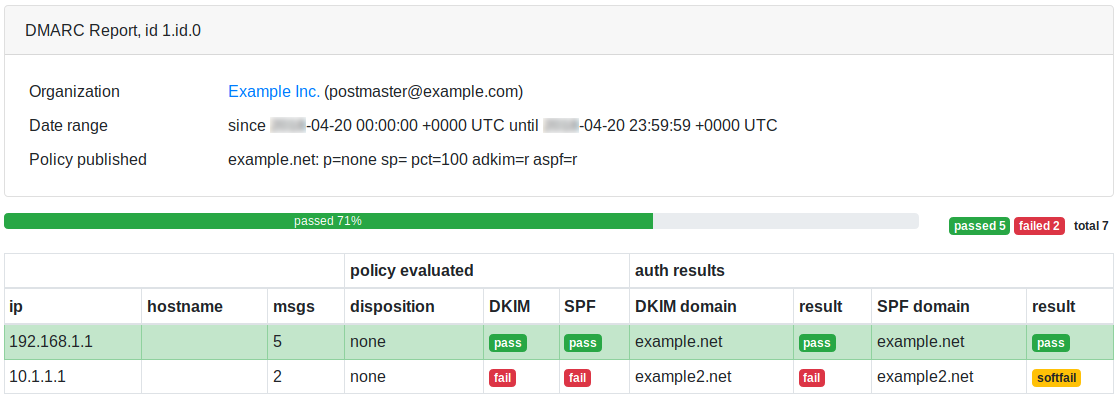
Themen in diesem Bereich:
detaillierte Berichte nach Monat, Tag, Stunde, Host und Absender-E-Mail-Adresse
E-Mail-Protokolle, Zustellstatusbenachrichtigungen (DSN), Benachrichtigungen über erfolgreiche Zustellung
Schau dir die versendeten E-Mails an, um zu verstehen, was los ist
RealSender bietet detaillierte Berichte über die Aktivitäten jedes SMTP-Servers und aller ausgehenden E-Mails.
Die Daten werden alle fünf Minuten automatisch aktualisiert.
Auf Wunsch senden wir Ihnen gerne eine wöchentliche Zusammenfassung per E-Mail zu.
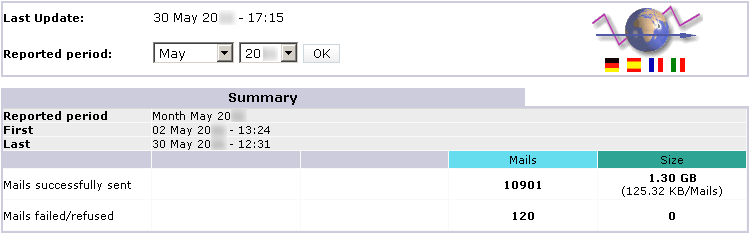
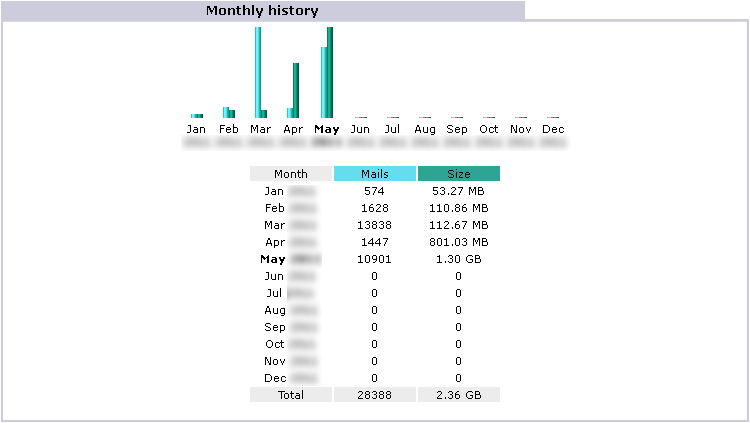
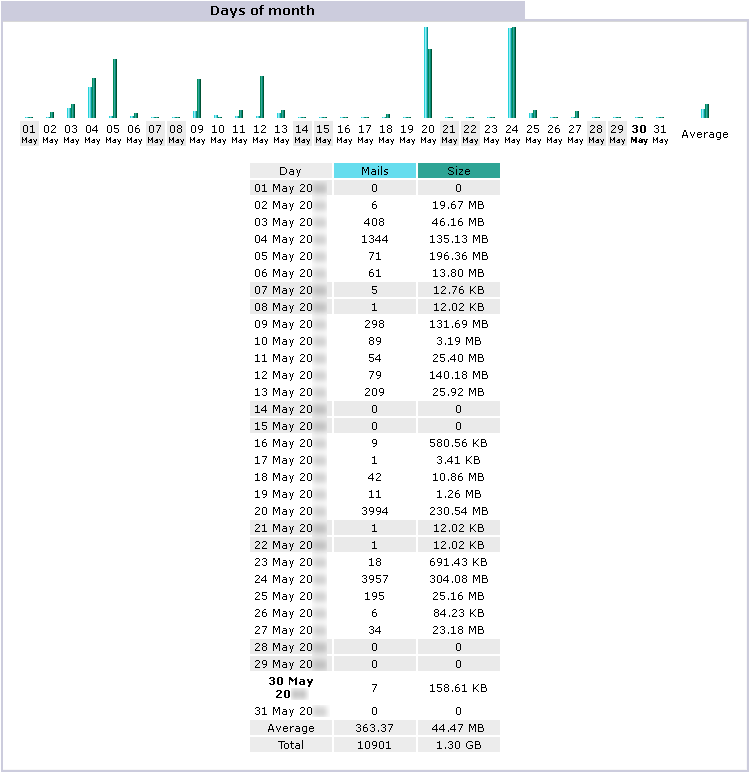
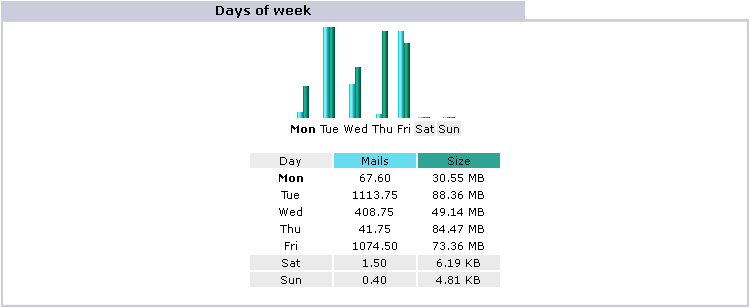
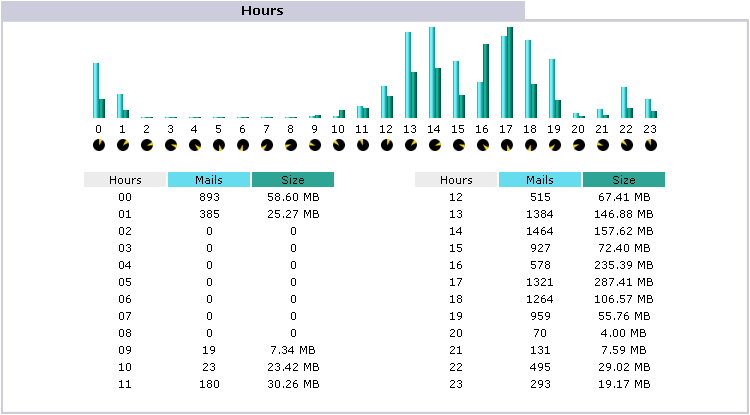
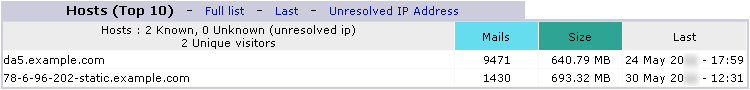
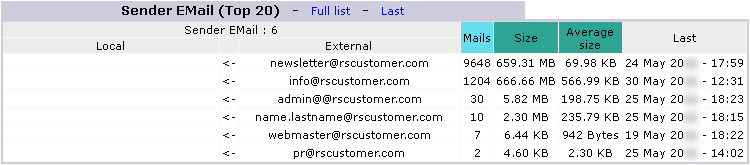
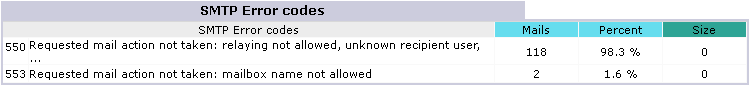
Hinweis: Diese Fehler werden durch unbefugte Versuche verursacht, E-Mails über den Server zu versenden.
Mit RealSender können Sie über den Browser auf die verarbeiteten E-Mail-Daten zugreifen:
Die angezeigten Daten können direkt über den Browser lokal gespeichert werden oder in regelmäßigen Abständen (z. B. einmal täglich) automatisch erfasst werden, um einen Verlauf zu erstellen.
31. Mai 06:26:22 rs336 v4V4QL1K030027:from=sender@yourcompany.com
31. Mai 06:26:25 rs336 v4V4QL1K030027:to=recipient@yourcustomer.com, dsn=2.0.0, stat=Gesendet (Nachricht zur Zustellung angenommen)
31. Mai 08:58:04 rs336 v4V6w3jN001390:from=sender@yourcompany.com
31. Mai 08:58:05 rs336 v4V6w3jN001390:to=recipient@yourcustomer.com, dsn=4.0.0, stat=Deferred: 421 recipient@yourcustomer.com Dienst nicht verfügbar – zu ausgelastet
31. Mai 09:02:03 rs336 v4V6w3jN001390:to=recipient@yourcustomer.com, dsn=4.0.0, stat=Deferred: 421 recipient@yourcustomer.com Dienst nicht verfügbar – zu ausgelastet
31. Mai 09:12:42 rs336 v4V6w3jN001390:to=recipient@yourcustomer.com, dsn=2.0.0, stat=Sent (Nachricht zur Zustellung angenommen)
31. Mai 10:00:22 rs336 v4V80L9Z004176:from=sender@yourcompany.com
31. Mai 10:00:24 rs336 v4V80L9Z004176:to=recipient@yourcustomer.com, dsn=4.7.1, stat=Deferred: 451 4.7.1 recipient@yourcustomer.com: Empfängeradresse abgelehnt: Greylisting aktiv, bitte versuchen Sie es später erneut
31. Mai 10:02:03 rs336 v4V80L9Z004176:to=recipient@yourcustomer.com, dsn=4.7.1, stat=Deferred: 451 4.7.1 recipient@yourcustomer.com: Empfängeradresse abgelehnt: Greylisting aktiv, bitte versuchen Sie es später erneut
31. Mai 10:12:04 rs336 v4V80L9Z004176:to=recipient@yourcustomer.com, dsn=2.0.0, stat=Sent (Nachricht zur Zustellung angenommen)
31. Mai 16:17:14 rs336 v4VEHCk6017038:from=sender@yourcompany.com
31. Mai 16:17:15 rs336 v4VEHCk6017038:to=recipient@yourcustomer.com, dsn=5.1.1, stat=Benutzer unbekannt
31. Mai 16:17:15 rs336 v4VEHCk6017038: v4VEHFk5017041: DSN: Benutzer unbekannt
25. Mai 12:43:37 rs336 v4PAhZw1019212:from=sender@yourcompany.com
25. Mai 12:43:38 rs336 v4PAhZw1019212:to=recipient@yourcustomer.com, dsn=5.0.0, stat=Dienst nicht verfügbar
25. Mai 12:43:38 rs336 v4PAhZw1019212: v4PAhcw0019217: DSN: Dienst nicht verfügbar
25. Mai 09:17:41 rs336 v4P7Hc6P011481:from=sender@yourcompany.com
25. Mai 09:17:42 rs336 v4P7Hc6P011481:to=recipient@yourcustomer.com, dsn=4.1.1, stat=Deferred: 452 4.1.1 recipient@yourcustomer.com 4.2.2 Postfach voll
[…] das System wiederholt den Zustellversuch alle zehn Minuten* […]
25. Mai 13:25:47 rs336 v4P7Hc6P011481:to=recipient@yourcustomer.com, dsn=4.1.1, stat=Deferred: 452 4.1.1 recipient@yourcustomer.com 4.2.2 Postfach voll
25. Mai 13:25:48 rs336 v4P7Hc6P011481: v4PBPko0020848: Absenderbenachrichtigung: Nachricht kann 4 Stunden lang nicht gesendet werden*
* = siehe Anmerkung am Ende des nächsten Absatzes
Zurückgewiesene E-Mails (z. B. wegen unbekanntem Empfänger) werden an die E-Mail-Adresse des Absenders oder an die Return-Path-Adresse (sofern angegeben) zurückgesendet.
Sollte es zu einer Verzögerung bei der Zustellung der Nachrichten kommen, erhalten Sie nach 30 Minuten* eine entsprechende Benachrichtigung, die wie folgt aussieht:
Betreff:
Warnung: In den letzten 30 Minuten konnte keine Nachricht gesendet werden
Text:
**********************************************
** DIES IST NUR EINE WARNUNG **
** SIE MÜSSEN IHRE NACHRICHT NICHT ERNEUT SENDEN **
**********************************************
[...] Das System versucht es vier Stunden lang automatisch erneut*. Wenn Sie keine weiteren Benachrichtigungen erhalten, bedeutet dies, dass die Nachricht erfolgreich zugestellt wurde. Sie können die Details in den Protokollen nachlesen (siehe die oben genannten Beispiele).
Nach vier Stunden* erfolgloser Wiederholungsversuche wird eine eindeutige Fehlermeldung an die E-Mail-Adresse des Absenders oder an die Return-Path-Adresse (sofern angegeben) gesendet, und zwar wie folgt:
Subject:
Returned mail: see transcript for details
Body:
The original message was received at ...
----- The following addresses had permanent fatal errors -----
<recipient@yourcustomer.com>
----- Transcript of session follows -----
Deferred: Connection timed out with yourcustomer.com.
Message could not be delivered for 4 hours
Message will be deleted from queue
[...] * = beim Versand von Massen-E-Mails:
Benachrichtigungen über verzögerte Zustellungen sind deaktiviert,
das Intervall zwischen den Zustellversuchen wird verlängert (von zehn auf dreißig Minuten),
die maximale Verweildauer in der Warteschlange wird verlängert (von vier auf vierundzwanzig Stunden)
Auf Wunsch können wir die „Zustellungsbenachrichtigung“ auch für erfolgreich zugestellte E-Mails aktivieren. Auf diese Weise erhält der Absender für jede zugestellte Nachricht eine Zustellungsbestätigung vom Zielserver, wie im folgenden Beispiel. Diese Option ist nützlich für alle, die für jede versendete E-Mail eine Zustellungsbestätigung benötigen.
Subject:
Return receipt
Body:
The original message was received at ...
----- The following addresses had successful delivery notifications -----
<recipient@yourcustomer.com> (successfully delivered to mailbox)
----- Transcript of session follows -----
<recipient@yourcustomer.com>... Successfully delivered
[...]In seltenen Fällen (bei weniger als 1 % der versendeten E-Mails) wird die Empfangsbestätigung nicht an den Absender gesendet. Dies geschieht, wenn der Empfänger auf seinem Mailserver eine spezielle Option namens „Datenschutz / keine Empfangsbestätigungen“ aktiviert hat. Diese Einstellung wird im Allgemeinen nicht empfohlen, da sie auch den Versand von standardmäßigen Benachrichtigungen über die Nichtzustellung blockiert.
Manchmal muss man sich die versendeten E-Mails ansehen, um zu verstehen, was vor sich geht.
Auf Wunsch kann RealSender die automatische Kopie aller ausgehenden E-Mails in ein spezielles Postfach aktivieren.
Das Postfach ist so eingerichtet, dass es problemlos große Mengen an E-Mails innerhalb kurzer Zeit empfangen kann.
E-Mails werden nach 7 Tagen automatisch gelöscht.
Bitte beachten Sie: Wenn die Nachrichten von privaten E-Mail-Konten versendet werden (auch wenn es sich um Firmenkonten handelt),
müssen Sie den Absender darüber informieren, dass die von ihm gesendeten Nachrichten zu technischen Überprüfungszwecken eingesehen werden können.

Um die ordnungsgemäße Funktion des Dienstes
zu überprüfen, haben wir eine automatische Testumgebung eingerichtet.
Eine externe Anwendung stellt alle zehn Minuten eine Verbindung zu jedem SMTP-Server her
und versendet eine echte Nachricht. Durch den erfolgreichen Versand der E-Mail können wir
die Verfügbarkeit und die ordnungsgemäße Funktion des Systems gewährleisten.
Das Ergebnis wird auf der „Statusseite“ Ihres RealSender-Servers unter
veröffentlicht
und ist unter der Webadresse rsXXX-realsender.com/status frei zugänglich
Die Daten werden in Echtzeit angezeigt, wie in den unten aufgeführten Beispieldaten zu sehen ist.
Die angezeigten Informationen beziehen sich auf die letzten vierundzwanzig Stunden.
11.09.2024 06:25:26 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
11.09.2024 06:16:18 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
2024-09-11 06:05:56 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
2024-09-11 05:55:41 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
2024-09-11 05:45:57 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
2024-09-11 05:35:58 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
2024-09-11 05:25:27 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
2024-09-11 05:16:30 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
2024-09-11 05:05:57 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
2024-09-11 04:55:36 UTC
rsXXX – alle zehn Minuten UPTIME-PRÜFUNG (eine E-Mail wurde erfolgreich versendet) – OK
Themen in diesem Bereich:
click.it: Der Link-Tracker mit sofortiger Rückmeldung per E-Mail
ein Ort, an dem E-Mails gespeichert und bei Bedarf abgerufen werden können
Teilen Sie Ihre Geheimnisse per E-Mail – Enigma ist ein sicherer Generator für einmalig verwendbare Links ohne Passwort
Ein gefälschter SMTP-/API-Dienst mit Web-GUI zum einfachen Testen von E-Mails in Anwendungen
ein Online-Prüftool zur Überprüfung der SPF- und DKIM-Einstellungen beim Versenden einer E-Mail
![]()
Die kostenlose Version ist voll funktionsfähig, weist jedoch einige Einschränkungen auf:
Die kostenpflichtige Version ist individuell angepasst und bietet Ihnen folgende Möglichkeiten:
email.locker ist ein Ort, an dem E-Mails gespeichert und bei Bedarf abgerufen werden können.
Nach sieben Tagen werden die E-Mails automatisch gelöscht.
Probieren Sie es jetzt aus:
E-Mail-Locker- Boxen werden spontan erstellt, indem man eine E-Mail-Nachricht an sie sendet.
Da keine Registrierung erforderlich ist, fungiert die E-Mail-Locker-Adresse im Grunde genommen als Passwort,
wählen Sie also etwas, das nicht leicht zu erraten ist.
Wenn Sie vertrauliche Informationen erhalten, sollten Sie in Erwägung ziehen, den Ordner zu sperren und den Zugriff darauf einzuschränken
oder sich eine eigene E-Mail-Adresse unter „@locker.yourcompany.com“ einzurichten. Kontaktieren Sie uns für weitere Informationen.
Alle an email.locker eingehenden Nachrichten werden mit RealSender-Authentifizierungsprüfungen gescannt,
sodass Sie überprüfen können, ob die Absenderadresse echt oder gefälscht ist.
Dem Betreff jeder empfangenen E-Mail wird ein Präfix hinzugefügt,
und zeigt Ihnen an, ob die Absender-Domain korrekt authentifiziert ist mit SPF und DKIM.
Ein Finale || OK || wird hinzugefügt, wenn Sie sich zu 100 % der Echtheit der Absenderdomain sicher sein können.

E-Mails sind weder privat noch sicher. Sie wurden nicht unter Berücksichtigung von Datenschutz oder Sicherheit entwickelt.
Jeder, der Ihre E-Mail während der Übertragung abfängt, kann sie lesen,
einschließlich Ihres Internetanbieters, eines Hackers oder der NSA (US-amerikanische Nationale Sicherheitsbehörde).
Eine End-to-End-Verschlüsselung (e2ee) für E-Mails kann eingesetzt werden, um sicherzustellen,
dass nur der Absender und der Empfänger einer Nachricht den Inhalt lesen können.
PGP ist die beste Lösung für eine sichere Kommunikation mit einem Partner, der
es bereits nutzt. Es könnte schwierig sein, Ihren Gesprächspartner dazu zu bewegen, PGP zu nutzen.
Enigma ist eine App, die auf dem Open-Source-Projekt SnapPass basiert.
Damit kannst du Geheimnisse auf sichere und kurzlebige Weise teilen.
Gib ein ein- oder mehrzeiliges Geheimnis sowie dessen Ablaufzeit ein und klicke auf „URL generieren“.
Teile die einmalig verwendbare URL mit dem gewünschten Empfänger.
Probieren Sie es aus:
enigma.realsender.com

inxsend ist ein gefälschter SMTP-/API-Dienst,
mit dem sich E-Mails in Anwendungen ganz einfach testen lassen,
indem alle Nachrichten an einen einzigen Mailserver gesendet werdenKonfigurieren Sie den SMTP-Server mit den folgenden Parametern:
Servername: inxsend.realsender.com
Port: 25 |oder| 2525 |oder| 587 (+TLS) |oder| 465 (+SSL)
Benutzername: CDED54
Passwort: 478DEDVerwenden Sie den API-Zugriff wie in der Anleitung„Versenden über API“beschrieben, mit den folgenden Parametern:
Serveradresse: (https://) inxsend-api.realsender.com/mail/send
apiuser: CDED54
apipass: 478DEDSenden Sie eine Nachricht an:
[IhrName]@inxbox.realsender.com
!! Alle empfangenen Nachrichten sind für jeden sichtbar !!
(andere Empfänger werden abgelehnt)
Teilen Sie uns bitte mit, wenn Sie Probleme haben.
Öffnen Sie https://inxbox.realsender.com/monitor und prüfen Sie die Empfangsqualität
(verwenden Sie den Google Chrome-Browser > Neues Inkognito-Fenster oder den Microsoft Edge-Browser)
Weitere Informationen zu diesem Postfach finden Sie unter: inxbox demo temporary email.

RealSender bietet unter
ein kostenloses Online-Prüftool an,
mit dem Sie Ihre SPF- und DKIM-Einstellungen durch das Versenden einer E-Mail überprüfen können:
Bei der Überprüfung wird der Betreffzeile „
“ ein Präfix hinzugefügt,
falls die Nachricht nicht ordnungsgemäß authentifiziert wurde.
Details on how it works
are located in the “email authentication basics” area of the website:
email authentication basics :: <spf> check online

Themen in diesem Bereich:
Anleitung zur Konfiguration der Protokolle SPF, DKIM und DMARC für die E-Mail-Authentifizierung
Mailman-„One-Way“-Liste, eine spezielle Konfiguration für Newsletter oder Ankündigungen
So verbessern Sie die Sicherheit, Leistung und Skalierbarkeit Ihres SMTP-Servers
Mit regulären Ausdrücken kannst du die gewünschten Daten abrufen
Eine einfache Möglichkeit, Domains, die keine E-Mails versenden, vor Missbrauch zu schützen
Warum Unternehmen SMS-Nachrichten nutzen
Wie man mit zurückgewiesenen E-Mails umgeht, um Schaden zu vermeiden
Wie kann ich überprüfen, ob mein SMTP-Server sicher ist?
Welche DNS-Einstellungen sind für den Versand von E-Mails erforderlich?
Wie man Mailinglisten mit Weitsicht verwaltet
Wie man Newsletter versendet und dabei die Qualität der Empfängerliste sowie das Interesse der Empfänger aufrechterhält
So versenden Sie private und verschlüsselte E-Mails
So versenden und begrenzen Sie Bcc-E-Mails: Vor- und Nachteile, Fazit
So messen Sie die Leistung Ihrer E-Mail-Marketing-Kampagnen
Welche Nutzer und Mailserver gelten als Spam-E-Mails?
Wie man mit einsatzbereiten Open-Source-E-Mail-Clients wieder die Kontrolle über seine E-Mails erlangt
E-Mails von Mitarbeitern: Dürfen sie gelesen werden? Können sie gesichert werden? Können sie archiviert werden?
So schützen Sie geschäftliche E-Mails vor Spam
So funktioniert DMARC mit Gmail und Office 365 – aktualisiert
Wie sich die DKIM-Domänenabgleichung auf die DMARC-Authentifizierung auswirkt
Welche sind die beliebtesten E-Mail-Anbieter im Jahr 2020?
So funktioniert DMARC mit Gmail und Office 365

!! ACHTUNG !! Dieses Dokument wurde automatisch aus dem Italienischen übersetzt
Die italienische Nationale Agentur für Cybersicherheit hat Leitlinien für die Konfiguration des E-Mail-Dienstes im Hinblick auf die Authentifizierung veröffentlicht, mit dem Ziel, die Zuverlässigkeit des E-Mail-Dienstes für alle betroffenen Organisationen zu stärken und dessen Sicherheitsniveau insgesamt zu erhöhen.
| VERSION | VERÖFFENTLICHUNGSDATUM | ANMERKUNGEN |
|---|---|---|
| 1.0 | April 2026 | Erstveröffentlichung. |
E-Mail ist heute einer der wichtigsten Dienste im digitalen Umfeld, da sie zu den Hauptkanälen gehört, die von Unternehmen und Nutzern für die Kommunikation und den Informationsaustausch genutzt werden1.
Die Funktionsweise des E-Mail-Dienstes und insbesondere die Übertragung von Nachrichten basieren auf dem SMTP-Protokoll, das jedoch von Haus aus keine ausreichenden Mechanismen zur Absenderauthentifizierung und zum Schutz der Vertraulichkeit und Integrität von Nachrichten enthält. Diese Schwachstellen setzen das System der Gefahr von Angriffen wie Spoofing, Phishing, Manipulation und dem Abfangen von Nachrichten während der Übertragung aus.
Um die Schwachstellen des SMTP-Protokolls zu beheben und damit das Risiko durch die oben genannten Angriffe zu verringern, wurden im Laufe der Zeit Mechanismen zur Absenderauthentifizierung und zum Schutz der Nachrichtenintegrität entwickelt, wie beispielsweise SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail) und DMARC (Domain-based Message Authentication, Reporting and Conformance).
Diese Richtlinien veranschaulichen diese Mechanismen mit dem Ziel, die Zuverlässigkeit des E-Mail-Dienstes zu stärken und dessen Sicherheitsniveau insgesamt zu erhöhen, wobei insbesondere auf die in Kapitel 4 beschriebenen Bedrohungen Bezug genommen wird.
Die zum Schutz der Vertraulichkeit von E-Mail-Nachrichten erforderlichen Maßnahmen und Protokolle (wie S/MIME und OpenPGP, die die Verschlüsselung von Nachrichten betreffen) sind nicht Gegenstand dieser Richtlinien.
| VERORDNUNG | BESCHREIBUNG |
|---|---|
| Nationaler Cybersicherheitsperimeter (PSNC) | Gesetzesdekret Nr. 105 vom 21. September 2019. Dringlichkeitsbestimmungen zum nationalen Cybersicherheitsperimeter und zur Regelung von Sonderbefugnissen in Sektoren von strategischer Bedeutung. |
| Cloud-Vorschriften für die öffentliche Verwaltung | Verwaltungsbeschluss der ACN Nr. 21007/24 vom 27. Juni 2024. |
| Gesetzesdekret Nr. 138 vom 4. September 2024 | Gesetzesdekret Nr. 138 vom 4. September 2024. Umsetzung der Richtlinie (EU) 2022/2555 über Maßnahmen für ein hohes gemeinsames Cybersicherheitsniveau in der gesamten Union, zur Änderung der Verordnung (EU) Nr. 910/2014 und der Richtlinie (EU) 2018/1972 sowie zur Aufhebung der Richtlinie (EU) 2016/1148. |
| TITEL UND VERÖFFENTLICHUNGSADRESSE |
|---|
| NIST Technical Note 1945. https://nvlpubs.nist.gov/nistpubs/TechnicalNotes/NIST.TN.1945.pdf |
| NIST SP 800-177 R1 https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-177r1.pdf |
| ACN. E-Mail-Authentifizierungs-Framework. https://www.acn.gov.it/portale/w/framework-di-autenticazione-per-la-posta-elettronica |
| RFC 5321 – Simple Mail Transfer Protocol https://datatracker.ietf.org/doc/html/rfc5321 |
| RFC 5322 – Format von Internetnachrichten https://datatracker.ietf.org/doc/html/rfc5322 |
| RFC 7208 – Sender Policy Framework (SPF) zur Autorisierung der Nutzung von Domänen in E-Mails, Version 1 https://datatracker.ietf.org/doc/html/rfc7208 |
| RFC 6376 – DomainKeys Identified Mail (DKIM)-Signaturen https://datatracker.ietf.org/doc/html/rfc6376 |
| RFC 7489 – Domain-basierte Nachrichtenauthentifizierung, Berichterstattung und Konformität (DMARC) https://datatracker.ietf.org/doc/html/rfc7489 |
Zum Schutz der digitalen Ressourcen des Landes, einschließlich E-Mail-Diensten und der Infrastruktur, auf der diese gehostet werden, wurde ein umfassendes Bündel an Sicherheitsmaßnahmen auf der Grundlage der geltenden Rechtsvorschriften eingeführt, das ständig aktualisiert wird.
Das höchste Schutzniveau für die wichtigsten Dienste des Landes, die mit dem Schutz der nationalen Sicherheit in Zusammenhang stehen, wird durch den Nationalen Cybersicherheitsperimeter gewährleistet, der durch das Gesetzesdekret Nr. 105 vom 21. September 2019 eingerichtet und mit Änderungen durch das Gesetz Nr. 133 vom 18. November 2019 umgesetzt wurde. Dieser sieht Sicherheitsmaßnahmen mit besonders hohem Schutzniveau vor, die in Anhang B des Dekrets des Ministerpräsidenten vom 14. April 2021, Nr. 81, die für die Netzwerke, Informationssysteme und IT-Dienste öffentlicher und privater Einrichtungen gelten, von denen die Ausübung einer wesentlichen staatlichen Funktion oder die Erbringung einer wesentlichen Dienstleistung zur Aufrechterhaltung ziviler, sozialer oder wirtschaftlicher Aktivitäten abhängt, die für die Interessen des Staates von grundlegender Bedeutung sind und deren Gefährdung zu einer Beeinträchtigung der nationalen Sicherheit führen könnte.
Darüber hinaus unterliegen E-Mail-Dienste, wie alle digitalen Dienste der öffentlichen Verwaltung, den Bestimmungen der sogenannten Cloud-Verordnung, die gemäß Artikel 33-septies des Gesetzesdekrets Nr. 179 vom 18. Oktober 2012 erlassen und von der Nationalen Agentur für Cybersicherheit (ACN) mit dem Direktorialdekret Nr. 21007 vom 27. Juni 2024 aktualisiert wurde. Gemäß der vorgenannten Verordnung sind alle öffentlichen Verwaltungen aufgefordert, ihre digitalen Daten und Dienste nach dem von der ACN erstellten Modell als gewöhnlich, kritisch oder strategisch einzustufen. Diese Maßnahme zielt darauf ab, sicherzustellen, dass digitale Daten und Dienste der öffentlichen Verwaltung über digitale Infrastrukturen und Cloud-Dienste verarbeitet und bereitgestellt werden, die den Anforderungen – einschließlich der Sicherheitsanforderungen – entsprechen, die den mit der jeweiligen Einstufungsstufe verbundenen Risiken angemessen sind, wie in der Verordnung dargelegt.
Mit dem Gesetzesdekret Nr. 138 vom 4. September 2024 (dem sogenannten NIS-Dekret) zur Umsetzung der Richtlinie (EU) 2022/2555 wurden – über die Anhänge 1 und 2 des ACN-Beschlusses 379907/2025 – die grundlegenden Sicherheitsmaßnahmen fest, die wesentliche und wichtige Stellen zur Erfüllung der Verpflichtungen gemäß den Artikeln 23 und 24 des NIS-Dekrets ergreifen müssen, und definiert damit einen Sicherheitsrahmen zur Stärkung des Schutzes von Netz- und Informationssystemen, einschließlich E-Mail-Diensten.
Wie bereits eingangs erwähnt, basiert die Funktionsweise des E-Mail-Dienstes auf dem SMTP-Protokoll, das die Übertragung von E-Mail-Nachrichten vom Absender zum Empfänger regelt.
Das SMTP-Protokoll wurde ursprünglich 1982 definiert2 als Store-and-Forward-Protokoll definiert, bei dem der Absender über seinen E-Mail-Client – in der Fachsprache Mail User Agent (MUA) – eine Nachricht erstellt, die an den Mailserver des Absenders gesendet wird. Dieser leitet die Nachricht über eine Komponente namens Mail Transfer Agent (MTA) weiter, möglicherweise auch über einen oder mehrere zwischengeschaltete MTAs, und liefert sie an den MTA des Ziel-Mailservers. Der Empfänger greift über seinen E-Mail-Client (MUA) auf die Nachricht zu[1].
Der MTA ist somit eine Komponente des E-Mail-Dienstes, die die Übertragung von E-Mail-Nachrichten vom Absender zum Empfänger übernimmt. MTA-Komponenten sind auf den Mail-Servern des Absenders und des Empfängers vorhanden, und es können auch Zwischen-MTAs konfiguriert werden, beispielsweise zur Verwaltung von Verteilerlisten.
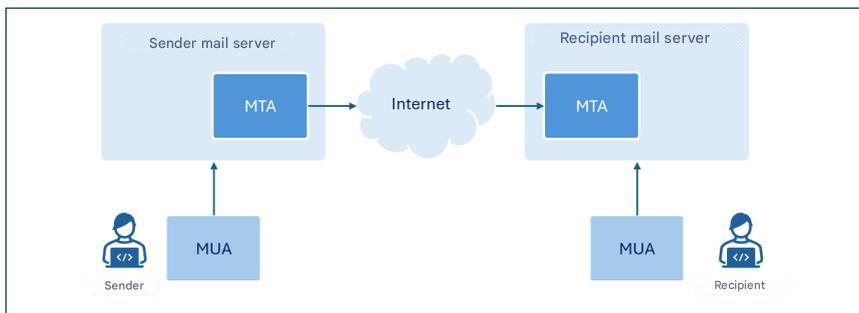
Die Abbildung zeigt nur die Komponenten, die für diese Leitlinien von Bedeutung sind.
Obwohl der Begriff MTA eine bestimmte Komponente von E-Mail-Servern bezeichnet3, wird in diesem Dokument auf diese hauptsächlich in ihrer Funktion als MTAs Bezug genommen; sofern keine Unklarheiten bestehen, wird der Begriff „E-Mail-Server“ der Einfachheit halber häufig anstelle des spezifischeren Begriffs „MTA“ verwendet.
In diesem Leitfaden konzentrieren wir uns auf die Konfiguration der Protokolle SPF, DKIM und DMARC, damit Mailserver die Echtheit und Integrität von E-Mail-Nachrichten überprüfen können.
Das im vorigen Kapitel vorgestellte SMTP-Protokoll war ursprünglich für den Einsatz in einem relativ kleinen akademischen Netzwerk konzipiert und berücksichtigte keine Aspekte hinsichtlich der Sicherheit der übertragenen Nachrichten oder der Absenderauthentifizierung [1].
Die zunehmende Verbreitung von E-Mails und die dem SMTP-Protokoll innewohnenden Schwachstellen haben im Laufe der Zeit die Entstehung von Angriffen begünstigt, deren Hauptarten in den folgenden Absätzen kurz erläutert werden.
Spoofing ist eine Technik für Cyberangriffe, bei der die Absenderadresse einer Nachricht gefälscht wird, sodass diese scheinbar von einer vertrauenswürdigen Adresse stammt (wie beispielsweise von einem Kollegen, einem Bekannten oder der eigenen Bank), um den Empfänger dazu zu verleiten, potenziell gefährliche Handlungen vorzunehmen, wie zum Beispiel das Öffnen eines E-Mail-Anhangs oder das Anklicken von Links in der Nachricht.
Diese Art von Angriff ist relativ einfach durchzuführen, da das SMTP-Protokoll keine Mechanismen zur Absenderauthentifizierung enthält und es daher über den E-Mail-Client möglich ist, beim Versenden der Nachricht eine beliebige Absenderadresse anzugeben.
E-Mail-Adresse des Absenders: envelope-from und message-from
Das E-Mail-Format sieht zwei unterschiedliche Felder vor, um die E-Mail-Adresse des Absenders anzugeben. Diese Felder heißen „envelope-from“ und „message-from“: Das erste (auch als „return-path“ bezeichnet, da es die E-Mail-Adresse angibt, an die etwaige Fehlermeldungen gesendet werden müssen, falls eine E-Mail den Empfänger nicht erreicht) ist die Adresse, die für die korrekte Weiterleitung der Nachricht verwendet wird; das zweite ist die Adresse, die dem Empfänger im Kopf der empfangenen Nachricht angezeigt wird.
Um einen Vergleich mit dem Versand eines Briefes in einem Umschlag per Post anzustellen: Der „envelope-from“ entspricht der Absenderadresse auf dem Briefumschlag, während der „message-from“ der Kopfzeile im Brief entspricht, aus der hervorgeht, wer den Brief an den Empfänger verfasst hat.
Es ist wichtig zu beachten, dass die beiden Adressen nicht unbedingt übereinstimmen müssen. Diese Unterscheidung ermöglicht die Handhabung von Situationen wie beispielsweise der Weiterleitung von Nachrichten durch Dienste von Drittanbietern, der Verteilung über Mailinglisten oder automatischen E-Mail-Antworten.
Es ist in der Tat möglich, einen beliebigen Absender sowohl auf der „Message-From“-Ebene (die E-Mail-Adresse des Absenders, die dem Empfänger im Kopf der empfangenen Nachricht angezeigt wird) als auch auf der „Envelope-From“-Ebene (die E-Mail-Adresse des Absenders, die für die Übermittlung der Nachricht verwendet wird) anzugeben.
Um diesen Bedrohungen entgegenzuwirken, ist es daher unerlässlich, Mechanismen bereitzustellen, die eine zuverlässige Authentifizierung des Absenders ermöglichen und sicherstellen, dass die Person, die die Nachricht gesendet hat, tatsächlich dazu berechtigt ist.
Phishing ist eine Technik für Cyberangriffe, die darauf abzielt, Informationen (wie beispielsweise Anmeldedaten, Kreditkartennummern oder andere sensible Daten) auf betrügerische Weise zu erlangen, in der Regel durch das Versenden von irreführenden Nachrichten, die den Anschein erwecken, von vertrauenswürdigen Absendern zu stammen3.
Das im vorigen Absatz behandelte Spoofing gehört zu den wichtigsten Techniken, die Angreifer einsetzen, um die Identität des Absenders zu fälschen und den Anschein zu erwecken, die Nachricht stamme von einem legitimen Nutzer oder einer legitimen Domain.
Alternativ kann eine Absenderadresse bzw. -domain verwendet werden, die der vom Empfänger erkannten ähnelt, indem beispielsweise der sogenannte Anzeigename geändert wird4 , um die scheinbare Authentizität der Nachricht zu verstärken.
Zum Versenden von Phishing-Nachrichten können auch legitime Konten genutzt werden, die zuvor vom Angreifer kompromittiert wurden.
Eine Phishing-Nachricht ist in der Regel so verfasst, dass sie beim Empfänger ein Gefühl der Dringlichkeit, Besorgnis oder wirtschaftlichen Verlockung hervorruft. Dadurch werden Situationen geschaffen, die den Empfänger dazu veranlassen, impulsiv zu reagieren und bestimmte Handlungen auszuführen, wie beispielsweise das Öffnen bösartiger Anhänge oder das Anklicken von Links, die auf scheinbar legitime Websites weiterleiten, die jedoch in Wirklichkeit vom Angreifer erstellt wurden, um Informationen zu stehlen und/oder Malware zu installieren.
In der Regel werden Phishing-Angriffe durchgeführt, indem dieselbe E-Mail-Nachricht an eine große Anzahl von Opfern versendet wird, ohne den Text an das jeweilige Profil der Opfer anzupassen.
Eine Variante des Phishing ist das sogenannte Spear-Phishing, bei dem der Angreifer das Profil des Opfers kennt und gezielt darauf abzielt.
Im Gegensatz zu einer gewöhnlichen Phishing-E-Mail nutzt eine Spear-Phishing-Nachricht präzisere Kontextinformationen, um den Nutzer davon zu überzeugen, dass er es mit einem vertrauenswürdigen Absender zu tun hat [2].
Der Inhalt einer E-Mail-Nachricht kann – wie jede andere Kommunikation, die über das Internet übertragen wird und keine End-to-End-Verschlüsselung (E2EE) nutzt – während der Übertragung zwischen Absender und Empfänger abgefangen und verändert werden (eine Art von Bedrohung, die gemeinhin als „Man-in-the-Middle“-Angriff bezeichnet wird).
Folglich besteht nicht nur die Gefahr eines Verlusts der Vertraulichkeit, sondern es kann auch vorkommen, dass die empfangene Nachricht nicht mit der ursprünglich vom Absender verfassten Nachricht übereinstimmt.
Ein Angreifer könnte beispielsweise den Inhalt der Nachricht so manipulieren, dass sie den Anschein erweckt, von einem vertrauenswürdigen Absender zu stammen, den Text oder darin enthaltene Links und/oder Anhänge ändern oder schädlichen Code einfügen.
Der Empfänger, der der scheinbaren Echtheit der Nachricht vertraut, kann so dazu verleitet werden, potenziell schädliche Handlungen vorzunehmen, wie beispielsweise die Weitergabe von Anmeldedaten, die Autorisierung von Zahlungen oder das Öffnen schädlicher Dateien.
Um diesen Bedrohungen entgegenzuwirken, ist es daher unerlässlich, Mechanismen einzuführen, die die Integrität und Authentizität der Nachricht gewährleisten und sicherstellen, dass der empfangene Inhalt nicht verändert wurde und der Absender tatsächlich der ist, für den er sich ausgibt.
In Kapitel 2 wurden die Vorschriften in Erinnerung gerufen, die Sicherheitsmaßnahmen auch zum Schutz von E-Mail-Diensten vorsehen. Dieses Dokument soll in erster Linie als Leitfaden für die Umsetzung der in diesen Vorschriften vorgesehenen und in Anhang A aufgeführten Sicherheitsmaßnahmen dienen, die auch für die Konfiguration von E-Mail-Diensten relevant sind, um die mit den in Kapitel 4 behandelten Bedrohungen verbundenen Risiken zu mindern. Es sei jedoch darauf hingewiesen, dass die in diesen Leitlinien enthaltenen Hinweise auch denjenigen empfohlen werden, die nicht den oben genannten Vorschriften unterliegen.
Die betreffenden Sicherheitsmaßnahmen beziehen sich nicht ausdrücklich auf die Konfiguration des E-Mail-Dienstes, sondern – je nach der jeweiligen Verordnung – auf die Konfiguration von IT-Systemen und industriellen Steuerungssystemen (PSNC und Cloud-Verordnung) oder von Informations- und Netzwerksystemen (NIS2). Die E-Mail-Dienste, die Gegenstand dieser Leitlinien sind, fallen unter beide Arten von Systemen.
Insbesondere werden im Folgenden die Protokolle SPF, DKIM und DMARC erläutert, die Sicherheitsmechanismen bieten, die darauf abzielen, die allgemeine Sicherheit des E-Mail-Dienstes und insbesondere die Absenderauthentifizierung sowie die Überprüfung der Nachrichtenintegrität zu verbessern.
SPF – Sender Policy Framework ist ein durch RFC 7208 formalisiertes Authentifizierungsprotokoll, das es einem Domaininhaber ermöglicht, festzulegen, welche IP-Adressen berechtigt sind, E-Mail-Nachrichten in seinem Namen zu versenden, und die Richtlinien festzulegen, die der Empfänger anwenden muss, wenn die mit der Domain verknüpfte IP-Adresse5 der E-Mail-Adresse des Absenders nicht zu den ausdrücklich autorisierten gehört.
Die autorisierten IP-Adressen sind in einem DNS-TXT-Eintrag aufgeführt, der sich auf die Absenderdomain bezieht und als SPF-Eintrag bezeichnet wird; dies wird im folgenden Abschnitt dieses Absatzes erläutert.
Auf diese Weise wird der E-Mail-Server des Empfängers6 beim Empfang einer Nachricht von einer bestimmten Domain den zugehörigen SPF-Eintrag abfragen und deren Herkunft authentifizieren, indem er überprüft, ob die IP-Adresse, von der die Nachricht empfangen wurde, zu denjenigen gehört, die zum Versenden von Nachrichten im Namen der Domain berechtigt sind.
Es ist wichtig zu beachten, dass die auf SPF-Ebene überprüfte Domain diejenige ist, die sich auf den „Envelope-From“-Eintrag bezieht; folglich reicht die Einführung des SPF-Protokolls allein nicht aus, um Spoofing zu verhindern, da diese Art von Angriff auf der „Message-From“-Ebene durchgeführt werden könnte7.
Falls ein Unternehmen seinen E-Mail-Dienst ganz oder teilweise an einen Dritten, wie beispielsweise einen Cloud-Anbieter, auslagert, muss es sicherstellen, dass die von diesen Anbietern versendeten Nachrichten die SPF-Prüfung bestehen. Zu diesem Zweck sollte das Unternehmen in seinen SPF-Eintrag die IP-Adressen aufnehmen, von denen aus die Anbieter E-Mails im Namen der Unternehmensdomain versenden.
Bei der automatischen E-Mail-Weiterleitung werden Nachrichten in der Regel über einen Zwischenserver umgeleitet, sodass die IP-Adresse, von der die endgültige Zustellung erfolgt, nicht mehr mit der ursprünglich von der Absenderdomain autorisierten IP-Adresse übereinstimmt. Um in diesen Fällen ein Scheitern der SPF-Überprüfung zu vermeiden, ist es erforderlich, auch alle zwischengeschalteten Weiterleitungsserver zu autorisieren oder auf Mechanismen wie SRS (Sender Rewriting Scheme) oder ARC (Authenticated Received Chain) zurückzugreifen, die insbesondere bei einer Vielzahl von zwischengeschalteten Weiterleitungsservern effektiver sein können.
Es ist zu beachten, dass SPF nur dann wirklich wirksam ist, wenn es nicht nur vom Absender, sondern auch vom Empfänger korrekt konfiguriert wird. Insbesondere:
Ein SPF-Eintrag ist ein DNS-Eintrag vom Typ TXT, dessen Name der Absenderdomain entspricht und dessen Inhalt aus8 aus dem Abschnitt, der die Version angibt9 sowie einer Reihe von Anweisungen, die das Verhalten des E-Mail-Servers des Empfängers festlegen, wenn eine Übereinstimmung zwischen der IP-Adresse der Absenderdomain und einer Anweisung vorliegt.
Die Anweisungen bestehen aus einem Mechanismus, dem ein Qualifizierer vorangestellt ist. Die wichtigsten Mechanismen, die in SPF-Einträgen verwendet werden, sind [2]:
Insbesondere die alle Dieser Mechanismus ermöglicht es, Richtlinien für Nachrichten festzulegen, die von IP-Adressen stammen, die durch frühere Mechanismen nicht erfasst wurden.
Darüber hinaus stellt SPF die folgenden Qualifizierer zur Verknüpfung mit Mechanismen bereit:
Es ist wichtig zu betonen, dass der SPF-Eintrag in der Praxis dazu dient, autorisierte IP-Adressen anzugeben, wobei auf die Anweisung zurückgegriffen wird -alle um festzulegen, dass alle anderen Adressen nicht zugelassen sind (siehe hierzu die folgenden Beispiele). Dies ist die empfohlene Konfiguration, da sie es ermöglicht, zugelassene IP-Adressen ausdrücklich anzugeben und alle anderen auszuschließen.
Auf jeden Fall wird empfohlen, die Anweisung niemals zu verwenden +alle (oder das Äquivalent alle), da dies einer Freigabe aller IP-Adressen entsprechen würde.
Beispiele für SPF-Einträge
Eine bestimmte IP-Adresse autorisieren
v=spf1 ip4:203.0.113.0 -all
Der oben gezeigte SPF-Eintrag verwendet SPF Version 1 und autorisiert über den ip4 Mechanismus der IP-Adresse 203.0.113.0 (da für das ip4 Mechanismus, die Standardeinstellung + wird implizit verwendet). Das -alle Richtlinie, die von der alle Mechanismus und die - Der Qualifizierer „(fail)“ gibt an, dass alle anderen Adressen nicht zugelassen sind.
Einen bestimmten IP-Adressbereich autorisieren
v=spf1 ip4:203.0.113.0/24 -all
Der oben gezeigte SPF-Eintrag entspricht dem vorherigen, autorisiert jedoch alle IP-Adressen der 203.0.113.0/24 Adressraum.
Mehrere IP-Adressen autorisieren
v=spf1 ip4:203.0.113.22 ip4:203.0.113.44 -all
Der oben gezeigte SPF-Eintrag autorisiert ausschließlich die IPv4-Adressen 203.0.113.22 und 203.0.113.44.
MX-Einträge und eine bestimmte Domain autorisieren
v=spf1 mx include:spf.emailprovider.it -all
Der oben angezeigte SPF-Eintrag autorisiert ausschließlich die IP-Adressen der MX-Einträge derselben Domain wie der SPF-Eintrag sowie die autorisierten IP-Adressen der Domain. spf.emailprovider.it (zum Beispiel die Domain eines E-Mail-Anbieters).
Ist die SPF-Überprüfung korrekt konfiguriert, ruft der Mailserver des Empfängers beim Empfang einer neuen E-Mail-Nachricht den SPF-Eintrag der Absenderdomain ab, indem er den DNS-Server abfragt, der die Einträge dieser Domain enthält, wie sie sich aus der im „Envelope-From“-Feld angegebenen Adresse ergibt. Wenn beispielsweise die im „Envelope-From“-Feld angegebene Adresse lautet alice@example.com, ruft der Mailserver des Empfängers den SPF-Eintrag der Domain ab beispiel.com.
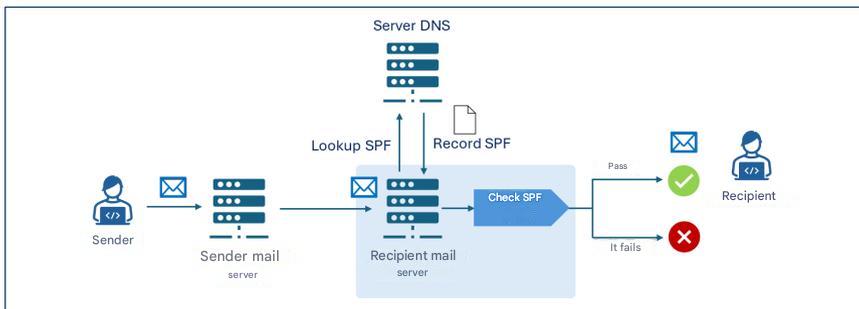
Der Mailserver des Empfängers führt daraufhin die SPF-Überprüfung durch und analysiert den SPF-Eintrag, um festzustellen, ob die IP-Adresse, von der die Nachricht empfangen wurde, zum Versenden von E-Mails für den beispiel.com Domain. Falls die E-Mail die SPF-Überprüfung besteht, wird sie an den Empfänger zugestellt.
Wenn beispielsweise der SPF-Eintrag der beispiel.com Domain waren v=spf1 ip4:203.0.113.22 -all Die Überprüfung würde nur erfolgreich sein, wenn die IP-Adresse des Absenderservers 203.0.113.22, während dies bei jeder anderen Adresse fehlschlagen würde.
DKIM – DomainKeys Identified Mail ist ein durch RFC 6376 standardisiertes Authentifizierungsprotokoll, das es einem Domaininhaber ermöglicht, die Echtheit versendeter E-Mail-Nachrichten zu gewährleisten, indem er eine digitale Signatur (DKIM-Signatur) anbringt, die vom Mailserver mithilfe öffentlicher kryptografischer Algorithmen generiert und in die Kopfzeilen der zu übermittelnden Nachricht eingefügt wird.
Damit der Empfänger überprüfen kann, ob die Nachricht während der Übertragung nicht verändert wurde, wird der mit der DKIM-Signatur verbundene öffentliche Schlüssel in einem TXT-Eintrag des öffentlichen DNS der Absenderdomain gespeichert – dem sogenannten DKIM-Eintrag –, der vom Mailserver des Empfängers beim Empfang der Nachricht abgefragt wird.
Die DKIM-Signatur und der DKIM-Eintrag werden in den folgenden Abschnitten dieses Absatzes erläutert.
Genau wie bei SPF muss auch DKIM vom Absender und vom Empfänger korrekt konfiguriert werden, insbesondere:
Die DKIM-Signatur wird ausgehend von bestimmten Elementen des Nachrichtentextes und der Kopfzeilen generiert und besteht aus einer Reihe von Schlüssel-Wert-Paaren, die Elemente angeben, darunter:
Kanonisierung ist der Prozess der Normalisierung von Nachrichtenelementen vor der digitalen Signatur, um die Auswirkungen kleinerer Änderungen zu minimieren, die während der Übertragung auftreten können, wie beispielsweise wiederholte Leerzeichen oder Zeilenumbrüche. Es gibt zwei Arten der Kanonisierung: die einfache Kanonisierung, bei der eine exakte Übereinstimmung zwischen der ursprünglichen und der empfangenen Nachricht erforderlich ist, und die lockere Kanonisierung, bei der Normalisierungen wie das Entfernen von Leerzeichen, die Umwandlung von Großbuchstaben in Kleinbuchstaben in den Kopfzeilen und die Reduzierung aufeinanderfolgender Leerzeilen im Nachrichtentext vorgenommen werden.
Der DKIM-Eintrag wird in einem DNS-Eintrag vom Typ TXT gespeichert, dessen Name folgende Struktur aufweist selector._domainkey.domain, wo _domainkey ist eine Kennzeichnung, die angibt, dass es sich bei dem DNS-Eintrag tatsächlich um einen DKIM-Eintrag handelt. Der Inhalt des DKIM-Eintrags besteht aus einer Reihe von Schlüssel-Wert-Paaren, die verschiedene Elemente festlegen, darunter:
Beispiel für einen DKIM-Eintrag
Name: s1._domainkey.example.com
Wert: v=DKIM1; k=rsa; p=Y2hpYXZ1cHViYmxpY2FkaWVzZW1waW8h...
Der Beispiel-DKIM-Eintrag ist mit dem Selektor verknüpft s1 der beispiel.com Domain, verwendet Version 1 und enthält den öffentlichen RSA-Schlüssel im Base64-Format (Y2hpYXZ1cHViYmxpY2FkaWVzZW1waW8h...).
Wenn das DKIM-Protokoll sowohl auf dem Mailserver des Absenders als auch auf dem des Empfängers korrekt konfiguriert ist, sieht der Ablauf des DKIM-Authentifizierungs- und -Verifizierungsprozesses vor, dass der Mailserver des Absenders die DKIM-Signatur der Nachricht gemäß Abschnitt 5.2.1 erstellt, die der Nachricht selbst hinzugefügt wird. Die DKIM-Signatur enthält insbesondere im d Feld „Signaturdomäne“17 und in der b Tragen Sie die digitale Signatur der Nachricht ein, die mit dem privaten Schlüssel der signierenden Domäne erstellt wurde.
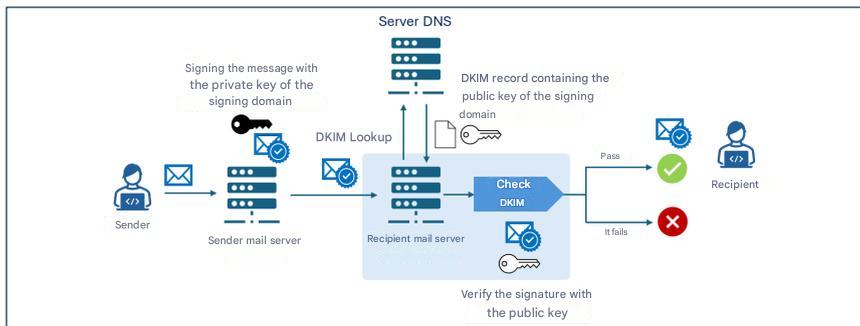
Nach dem Empfang einer Nachricht ruft der Mailserver des Empfängers den DKIM-Eintrag der signierenden Domain ab (d Feld der DKIM-Signatur) vom DNS-Server, der die Einträge dieser Domain enthält. Anschließend verwendet es den im DKIM-Eintrag enthaltenen öffentlichen Schlüssel, um die digitale Signatur zu überprüfen (b (Feld), das in der DKIM-Signatur enthalten ist. Ist die Überprüfung erfolgreich, wird die Nachricht an den Empfänger zugestellt.
Im Bereich der Kryptografie wurde bei DKIM bislang der RSA-Algorithmus verwendet, insbesondere in der Variante rsa-sha256, die seit 2007 als Standard gilt. Die neue Alternative, die durch RFC 8463 eingeführt wurde, ist Ed25519-SHA256, eine moderne Form der digitalen Signatur auf Basis elliptischer Kurven, die eine höhere Effizienz und wesentlich kompaktere Schlüssel gewährleistet.
Auf technischer Ebene bleibt RSA mit einer Schlüssellänge von 2048 Bit der universelle Standard, doch die Schlüssel sind lang und die Signaturen relativ groß, während Ed25519 neunmal kürzere Schlüssel und viermal kleinere Signaturen bietet, wobei die Signaturleistung im Vergleich zu RSA 2048 bis zu dreißigmal höher ist. Trotz dieser Vorteile ist die Unterstützung in der Praxis begrenzt: Im Jahr 2026 wird Ed25519 nur von wenigen Anbietern verifiziert, während einige große Betreiber weder die Signierung noch die Verifizierung zuverlässig unterstützen, was es als alleinige Lösung im Produktivbetrieb ungeeignet macht.
Aus diesem Grund wird die Verwendung von Ed25519 – obwohl es technisch überlegen ist – zum Zeitpunkt der Erstellung dieses Dokuments nicht empfohlen, außer in Kombination mit RSA im Rahmen einer doppelten Signatur, und zwar aus experimentellen Gründen und als Maßnahme zur Gewährleistung der zukünftigen Kompatibilität. Bis große Anbieter die Überprüfung dieses Verfahrens vollständig implementiert haben, bleibt RSA unverzichtbar, um eine maximale Zuverlässigkeit bei der Nachrichtenzustellung zu gewährleisten.
Im Hinblick auf die langfristige Sicherheit ist zu beachten, dass weder RSA noch Ed25519 gegen Angriffe durch künftige Quantencomputer resistent sind [3] und dass der Übergang zu postquanten-sicheren Algorithmen neue DKIM-Standards erfordern wird, die derzeit noch nicht existieren. Daher ist es unerlässlich, die Entwicklungen im Bereich der Kryptografie der nächsten Generation sowie künftige Empfehlungen des ACN in diesem Bereich aufmerksam zu verfolgen.
Was die Verwaltung kryptografischer Schlüssel betrifft, muss der private DKIM-Schlüssel durch strenge Sicherheitsmaßnahmen geschützt werden. Dazu gehört, ihn auf isolierten Systemen zu speichern, auf die nur autorisierte Dienste Zugriff haben, sowie restriktive Zugriffsrechte, regelmäßige Rotation und ständige Überwachung, um unbefugten Zugriff oder Kompromittierungen zu verhindern.
DMARC – Domain-based Message Authentication, Reporting and Conformance ist ein durch RFC 7489 formalisiertes Authentifizierungsprotokoll, das18 die Mechanismen SPF und DKIM integriert und es einem Domain-Inhaber ermöglicht, den Empfängern von Nachrichten, die von dieser Domain gesendet werden, Richtlinien für den Umgang mit solchen Nachrichten vorzugeben, die die SPF- und DKIM-Prüfungen nicht bestehen.
Insbesondere führt DMARC einen Authentifizierungsmechanismus ein – das sogenannte „Alignment“ –, der die Übereinstimmung zwischen den durch SPF und DKIM authentifizierten Domänen und der Domäne überprüft, auf die sich die Nachricht von Feld der empfangenen Nachricht. Beachten Sie, dass die Überprüfung der Ausrichtung zwischen dem Nachricht von Feld, und die SPF/DKIM-Domäne schlägt in jedem Fall fehl, wenn die entsprechende SPF/DKIM-Überprüfung fehlschlägt (siehe Abbildung 4).
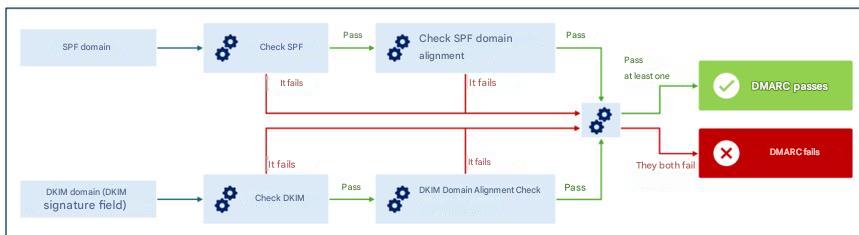
Die Ausrichtung kann überprüft werden in streng Modus, bei dem eine exakte Übereinstimmung zwischen den durch SPF/DKIM authentifizierten Domänen und derjenigen erforderlich ist, die sich auf die Nachricht von Feld oder entspannt, wobei es ausreicht, dass die Hauptdomains übereinstimmen, auch wenn sich die Subdomains unterscheiden können.
Zum Beispiel in entspannt Modus für Domains sub1.example.com und sub2.example.com würde für die DMARC-Überprüfung eine Übereinstimmung gefunden (da die primäre Domain, beispiel.com, ist dasselbe). In streng In diesem Modus würde die DMARC-Übereinstimmungsprüfung jedoch fehlschlagen, da keine exakte Übereinstimmung zwischen den Domänen vorliegt.
Durch die Überprüfung der Übereinstimmung kann ein Angreifer, selbst wenn es ihm gelänge, die SPF- und/oder DKIM-Prüfungen mithilfe eines Nachricht von anders als der Absenderadresse Selbst wenn die E-Mail durch SPF authentifiziert wurde und/oder von der authentifizierten Signaturdomäne stammt, würde DMARC die Diskrepanz dennoch erkennen und so eine konsistente und zuverlässige Überprüfung der Identität des Absenders gewährleisten [2].
Richtlinien für den Umgang mit fehlgeschlagenen Nachrichten19 DMARC-Überprüfung sind in einem TXT-Eintrag des relativen DNS-Servers der Absenderdomain festgelegt, der als DMARC-Eintrag bezeichnet wird und im folgenden Abschnitt dieses Absatzes erläutert wird.
DMARC ermöglicht es außerdem, Empfänger dazu aufzufordern, Berichte an die Inhaber der Absenderdomain zu senden, die sich auf Nachrichten beziehen, die angeblich von dieser Domain stammen. Auf diese Weise kann der Domaininhaber überprüfen, ob und in welchem Umfang seine Domain unbefugt genutzt wird, indem er beispielsweise analysiert, wie viele der Nachrichten, die angeblich von seiner Domain stammen, tatsächlich auf ihn zurückzuführen sind.
Genau wie bei SPF und DKIM muss auch DMARC vom Absender und vom Empfänger korrekt konfiguriert werden, insbesondere:
Der Name des DMARC-Eintrags hat folgende Struktur _dmarc.domain, wo _dmarc ist ein Kennzeichen, das angibt, dass es sich bei dem DNS-Eintrag um einen DMARC-Eintrag handelt, und Domäne ist die Domäne, auf die sich die Richtlinie bezieht.
Der DMARC-Eintrag besteht aus einer Reihe von Schlüssel-Wert-Paaren, die verschiedene Elemente festlegen, darunter:
keine, Quarantäne, ablehnen;entspannt, Standardwert oder streng);entspannt, Standardwert oder streng);Beispiel für einen DMARC-Eintrag
Name:
_dmarc.example.com
Wert:
v=DMARC1; p=reject; rua=mailto:dmarc-reports@example.com; ruf=mailto:dmarc-fail@example.com; adkim=s; aspf=s
Der Beispiel-DMARC-Eintrag ist mit dem beispiel.com Domäne, verwendet Version 1 und gibt die ablehnen Richtlinie für E-Mails, die die DMARC-Überprüfung nicht bestehen, mit der Aufforderung streng Modus (s) zur Überprüfung der Übereinstimmung von SPF- und DKIM-Domänen sowie zur Übermittlung von Sammelberichten an die E-Mail-Adresse dmarc-reports@example.com sowie Fehlermeldungen an die Adresse dmarc-fail@example.com.
Wie im vorigen Absatz beschrieben, gibt der DMARC-Eintrag die Richtlinie an, die der empfangende Mailserver auf Nachrichten anwenden soll, die die DMARC-Überprüfung nicht bestehen. Folgende Richtlinien sind möglich:
Wenn das DMARC-Protokoll sowohl auf dem Mailserver des Absenders als auch auf dem des Empfängers korrekt konfiguriert ist, ruft der Mailserver des Empfängers beim Empfang der Nachricht die SPF- und DKIM-Einträge ab, um die entsprechenden Überprüfungen sowie die DMARC-Überprüfung durchzuführen (wie im Einleitungsteil von Abschnitt 5.2.4 beschrieben). Falls die Nachricht die DMARC-Überprüfung nicht besteht, wird die im DMARC-Eintrag angegebene Richtlinie (keine, Quarantäne oder ablehnen) wird angewendet.
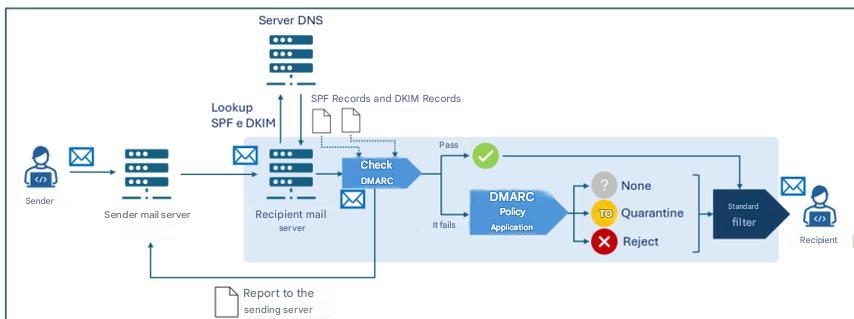
Beachten Sie, dass jeder Mailserver lokale Heuristiken und Richtlinien anwenden kann, um über die Zustellung einer Nachricht zu entscheiden, wobei auch die Ergebnisse der SPF-, DKIM- und DMARC-Prüfungen berücksichtigt werden. Daher findet im Allgemeinen nach den oben genannten Prüfungen ein zusätzlicher Entscheidungsprozess statt („Standardfilter“ in Abbildung 5), der auch weitere Überprüfungen (wie beispielsweise Anti-Spam- und Anti-Malware-Filter) umfassen kann.
Darüber hinaus kann der empfangende Mailserver Folgendes übermitteln:
Straße Feld des DMARC-Eintrags, aggregierte Berichte mit statistischen Daten und Zusammenfassungen zu den von der Absenderdomain empfangenen Nachrichten;ruf Feld des DMARC-Eintrags, detaillierte Berichte zu einzelnen Nachrichten, die von der Absenderdomain empfangen wurden und die DMARC-Überprüfung nicht bestanden haben.Wie im vorigen Kapitel erläutert, ist es zur bestmöglichen Abwehr von Bedrohungen im Zusammenhang mit der Vortäuschung der Absenderdomain erforderlich, dass alle drei untersuchten Protokolle gemeinsam implementiert werden, und insbesondere, dass [3]:
Im Hinblick auf die Protokollimplementierung werden zudem folgende Empfehlungen ausgesprochen [2]:
Weitere Informationen finden Sie in den unter „Referenzdokumente“ aufgeführten Quellen.
Es ist festzustellen, dass zum angemessenen Schutz der E-Mail-Sicherheit neben den hier untersuchten Authentifizierungsprotokollen weitere Protokolle existieren – die nicht Gegenstand dieser Leitlinien sind –, wie beispielsweise TLS (Transport Layer Security), das die Verschlüsselung des Übertragungskanals gewährleistet, sowie S/MIME und OpenPGP, die sich auf die End-to-End-Verschlüsselung und die Nachrichtenauthentifizierung beziehen.
Es sei zudem darauf hingewiesen, dass – obwohl es sich dabei nicht um ein E-Mail-Sicherheitsprotokoll im engeren Sinne handelt – im Hinblick auf die Sicherheit von E-Mail-Diensten die Implementierung von DNSSEC (Domain Name System Security Extensions) empfohlen wird, einer Erweiterung des DNS-Protokolls, die DNS-Einträge mit kryptografischen Signaturen versieht, um die Integrität und Authentizität von DNS-Abfragen zu gewährleisten. Dank DNSSEC werden beispielsweise Informationen zu SPF-, DKIM- und DMARC-Einträgen während der Übertragung geschützt, wodurch das Risiko von Manipulationen verringert und somit die Sicherheit des E-Mail-Dienstes erhöht wird.
PR.IP-1: Für die Konfiguration von IT-Systemen und industriellen Steuerungssystemen werden Referenzverfahren (sogenannte Baselines) definiert und verwaltet, die Sicherheitsgrundsätze (z. B. das Prinzip der minimalen Funktionalität) berücksichtigen.
PR.IP-01: Für die Konfiguration von IT-Systemen und industriellen Steuerungssystemen werden Referenzverfahren (sogenannte Baselines) definiert und verwaltet, die Sicherheitsgrundsätze (z. B. das Prinzip der minimalen Funktionalität) berücksichtigen.
PR.IP-01: Für die Konfiguration von IT-Systemen und industriellen Steuerungssystemen werden Referenzverfahren (sogenannte Baselines) definiert und verwaltet, die Sicherheitsgrundsätze (z. B. das Prinzip der minimalen Funktionalität) berücksichtigen.
PR.PS-01: Es werden Verfahren für das Konfigurationsmanagement festgelegt und angewendet.
[1] NIST, „Technical Note 1945“.
[2] NIST, „NIST Special Publication 800-177 Revision 1“
[3] Nationale Cybersicherheitsbehörde, „Post-Quanten- und Quantenkryptografie – Vorbereitung auf die Quantenbedrohung“.
[4] Nationale Cybersicherheitsbehörde, „Rahmenwerk für die E-Mail-Authentifizierung“.
Eurostat-Daten 2026, https://ec.europa.eu/eurostat/databrowser/view/tin00094/default/table?lang=en&category=f_isoc_t_isoc_i_t_isoc_iu↩︎
RFC 821 wurde später durch RFC 5321 aus dem Jahr 2008 aktualisiert.↩︎
Im Allgemeinen verfügen E-Mail-Server sogar über zusätzliche Module, die andere Aufgaben als der MTA übernehmen, wie zum Beispiel Module für die lokale Speicherung von Nachrichten und für den Zugriff der Clients auf ihre E-Mail-Postfächer.↩︎↩︎
Der Anzeigename ist das Textfeld, das der E-Mail-Adresse des Absenders zugeordnet ist und dem Empfänger vom E-Mail-Client im Kopf der Nachricht angezeigt wird. Er unterscheidet sich von der E-Mail-Adresse und dient dazu, den Absender auf lesbare und erkennbare Weise zu identifizieren.↩︎
Eine E-Mail-Adresse hat folgende Struktur: lokaler-Teil@Domänen-Teil wo lokaler Teil identifiziert den jeweiligen Benutzer innerhalb des E-Mail-Systems oder -Servers, der mit dem Domänen-Teil, was stattdessen dem Domainnamen des Systems oder Dienstes entspricht, auf dem das durch die lokaler Teil [2]. ↩︎
Sofern dies zu keinen Missverständnissen führt, wird im Interesse eines flüssigen Leseflusses der Begriff „E-Mail-Server“ anstelle von „MTA“ verwendet, wobei es sich bei MTA um die Komponente des E-Mail-Servers handelt, die die Übertragung von Nachrichten vom Absender zum Empfänger übernimmt.↩︎
Zur Unterscheidung zwischen „envelope-from“ und „message-from“ lesen Sie bitte den Abschnitt „E-Mail-Adresse des Absenders: envelope-from und message-from“ in Abschnitt 4.1.↩︎
Es können auch sogenannte Modifikatoren vorhanden sein, die zusätzliche Informationen, Ausnahmen von Regeln und Abweichungen von Standardwerten angeben.↩︎
Derzeit gibt es nur eine Version des Protokolls (v=spf1). ↩︎
Derzeit gibt es nur eine Version des Protokolls (v=1). ↩︎
Der Standardalgorithmus ist rsa-sha256. ↩︎
Die signierende Domain ist jene, die die Authentizität der Nachricht durch eine digitale Signatur gewährleistet und auf die sich Empfänger beziehen, um den öffentlichen DKIM-Schlüssel aus dem DNS abzurufen und die Signatur zu überprüfen. Sie muss nicht unbedingt mit der „Message-From“- und/oder „Envelope-From“-Domain übereinstimmen, doch DMARC-Richtlinien können eine Übereinstimmung mit diesen verlangen (siehe hierzu den Abschnitt zu DMARC).↩︎
Der Selektor ermöglicht die eindeutige Identifizierung des kryptografischen Schlüsselpaars, das zur Erstellung der Signatur verwendet wurde. Für eine bestimmte Domäne können tatsächlich mehrere Schlüsselpaare generiert werden, damit MTAs derselben Domäne unterschiedliche Schlüssel verwenden können oder um eine effektive regelmäßige Schlüsselrotation zu ermöglichen.↩︎
Insbesondere werden bestimmte Nachrichten-Header (wie „Von“, „An“, „Betreff“ und „Datum“) signiert, die während der Nachrichtenübertragung nicht verändert werden.↩︎
Der Nachrichten-Hash wird in der Regel über den gesamten Nachrichtentext berechnet. Um Fälle zu berücksichtigen, in denen die Nachricht während der Übertragung verändert wird, indem beispielsweise Elemente wie Fußzeilen oder Haftungsausschlüsse hinzugefügt werden (man denke an Mailinglisten-Dienste oder automatische Weiterleitungen), ist es möglich, für Signaturzwecke nur einen Teil der Nachricht heranzuziehen. Diese Vorgehensweise birgt jedoch Risiken, da sie die vollständige Integrität der empfangenen Nachricht nicht gewährleistet.↩︎
Die digitale Signatur wird ausgehend von den in h und den Hash des Nachrichtentextes in bh. ↩︎
Wie bereits in Abschnitt 5.2.1 erwähnt, stimmt die signierende Domäne in der Regel nicht mit der „message-from“- und/oder „envelope-from“-Domäne überein, doch können DMARC-Richtlinien eine Übereinstimmung vorschreiben (wie im Abschnitt zu DMARC erläutert wird).↩︎
Damit DMARC funktioniert, muss mindestens eines der Protokolle SPF oder DKIM implementiert sein. In diesem Leitfaden wird, wie in Kapitel 5 beschrieben, die gemeinsame Implementierung aller drei Protokolle empfohlen.↩︎
Um die DMARC-Überprüfung zu bestehen, muss mindestens eine der beiden Authentifizierungsmethoden (SPF oder DKIM) gültig sein.↩︎
Derzeit gibt es nur eine Version des Protokolls (v=DMARC1). ↩︎

In einem früheren Beitrag haben wir die Vor- und Nachteile der Verwendung von BCC-E-Mails erläutert,
siehe:„So versenden und begrenzen Sie BCC-E-Mails“.
In den Schlussfolgerungen haben wir unter anderem Folgendes festgestellt:
Verwenden Sie spezielle Apps für den Versand von Massen-E-Mails.
Die professionellen Systeme verfügen über einen Genehmigungsworkflow
und eine schrittweise Kontrolle;
sie sind darauf ausgelegt, Fehler zu vermeiden.
Zusammenfassung dieses Artikels:
E-Mail-Marketing-Plattformen können schwierig zu erlernen und zu betreuen sein (falls Sie diese Ihren Kunden zur Verfügung stellen).
Wir möchten Ihnen hier die Möglichkeit vorstellen, die Open-Source-Software „GNU Mailman“ für den Versand Ihrer Massen-E-Mails zu nutzen.
Dieser Vorschlag basiert auf unseren eigenen Erfahrungen mit der benutzerfreundlichen„Copymail App“.
Eine „One-Way“-Liste in Mailman ist eine Konfiguration für Newsletter oder Ankündigungen
,
bei der nur autorisierte Moderatoren Beiträge veröffentlichen können und Mitglieder nicht auf der Liste antworten können.
So funktioniert es:
Der Nutzer sendet die Nachricht über seinen E-Mail-Client oder über das Webmail an die E-Mail-Adresse der Liste:
Anschließend muss er den Versand bestätigen, woraufhin die Nachricht serverseitig an alle Abonnenten verteilt wird.
Das System verarbeitet automatisch Bounces (zurückgesendete E-Mails) und führt auf Wunsch die Abmeldung durch.
Abonnements müssen manuell registriert werden.
Der Dienst ist äußerst zuverlässig und kann problemlos Tausende von Adressen verarbeiten.
Der Versand erfolgt über RealSender oder andere SMTP-Server.
GNU Mailman ist eine weit verbreitete Software, die von den meisten Internetdienstanbietern angeboten wird.
Im Internet gibt es einige Anleitungen, die erklären, wie man sie für Massenversendungen konfiguriert und nutzt:
Die wichtigste Quelle ist dieses Dokument, das auf zwei Beiträgen von Barry Warsaw in der Mailman-Users-Liste basiert:
Wie erstelle ich einen Newsletter, eine Ankündigung oder eine Einweg-Liste?
Der Text erläutert die wichtigsten Punkte im Detail:
Ein weiterer Artikel der Stanford University erklärt, wie Mailman
genutzt werden kann, um eine Liste einzurichten, die ausschließlich für Ankündigungen gedacht ist:
So richten Sie eine „einseitige“ Liste nur für Ankündigungen oder einen Newsletter ein – Wissensartikel KB00010792
Mailinglisten können entweder als Diskussionsforen oder als Ankündigungsplattformen dienen. Die Mailman-Software ist in Python geschrieben; vor ihrer Veröffentlichung nutzte die Python-Community Majordomo, einen auf Perl basierenden Mailinglisten-Manager.
Heute betreut Mark Sapiro den stabilen 2.1-Zweig,
,
während sich Barry Warsaw auf die neue 3.X-Version konzentriert.
Zwei übergeordnete Grundsätze, die für den anhaltenden Erfolg von Mailman entscheidend sind:
In Mailman 2 haben die Entwickler das System zur Nachrichtenverarbeitung neu gestaltet, um sicherzustellen, dass diese beiden Grundsätze stets oberste Priorität haben. Dieser Teil des Systems ist nun seit mindestens einem Jahrzehnt stabil und einer der Hauptgründe dafür, dass Mailman heute so weit verbreitet ist.
VERP steht für „Variable Envelope Return Path“. Es handelt sich um eine bekannte Technik, die Mailinglisten einsetzen, um Adressen von Empfängern, bei denen es zu Rückläufern kommt, eindeutig zu identifizieren. Wenn die Mailingliste einen Rückläufer erhält, kann sie entsprechende Maßnahmen ergreifen, beispielsweise die betreffende Adresse deaktivieren oder aus der Mitgliederliste entfernen.
Es gibt ein Standardformat für Rückmeldungen, das als „Zustellstatusbenachrichtigungen“ bezeichnet wird. Mailman nutzt eine Bibliothek, die Dutzende von Heuristiken für das Format von Rückmeldungen enthält, die alle im Laufe der zwanzigjährigen Geschichte von Mailman in der Praxis aufgetreten sind.
VERP nutzt eine Anforderung des grundlegenden SMTP-Protokolls aus, um eine eindeutige Erkennung von Bounce-Nachrichten zu gewährleisten, indem solche Bounce-Nachrichten an den Absender der Hülladresse zurückgesendet werden.
Dies ist nicht die Von: Feld im Nachrichtentext, aber tatsächlich ist das E-MAIL VON Wert, der im SMTP-Dialog festgelegt wurde. Dieser Wert bleibt während des gesamten Zustellungsvorgangs erhalten, und der endgültige empfangende Mailserver ist gemäß den Standards verpflichtet, die Rückmeldungen an diese Adresse zu senden.
Wenn der Mailman-Server mylist@example.org, dann der VERP-kodierte Absender einer E-Mail, die an eine Mailingliste gesendet wurde anne@example.com lautet:
mylist-bounce+anne=example.com@example.org. Zurückgewiesene E-Mails werden an die VERP-verschlüsselte Empfängeradresse gesendet. Mailman kann dann die An: Header, um den ursprünglichen Empfänger zu ermitteln anne@example.com
Die Verwendung von VERP setzt voraus, dass Mailman genau eine Kopie der Nachricht pro Empfänger versendet.
VERP erfordert eine eindeutige E-MAIL VON für jeden Empfänger, und das geht nur, indem man eine eigene Kopie der Nachricht versendet.
Dieser Ansatz trägt zudem dazu bei, dass die Nachricht nicht als Spam eingestuft wird.
Während der Testphase ist die Standardeinstellung „Copymail-AppBei der Konfiguration „“ wird eine von uns bereitgestellte Domain als E-Mail von Adresse (auch bekannt als Bounce-/Return-Path-/Envelope-Adresse), an die zurückgewiesene E-Mails zurückgeschickt werden. Diese E-Mail von Die Domain unterscheidet sich von der Von Absenderadresse (die für die Empfänger sichtbare Adresse des Absenders).
Bevor das System in Betrieb genommen wird, müssen einige Änderungen am DNS vorgenommen werden, um die mit dem Von Domain.
Die neuesten E-Mail-Standards ermöglichen es Ihnen, authentifizierte E-Mails unter Verwendung einer Subdomain als E-Mail von Adresse (zum Beispiel, email.deine-E-Mail-Domain.com), wobei die Basisdomain weiterhin als Von/Absender Adresse (zum Beispiel, info@youremaildomain.com). Weitere Einzelheiten finden Sie in der E-Mail-Authentifizierung – Erweitert Seite.
Die gleiche Situation kann auch in anderen Umgebungen auftreten. Wir empfehlen Ihnen, dies bei Ihrem Internetanbieter zu überprüfen.
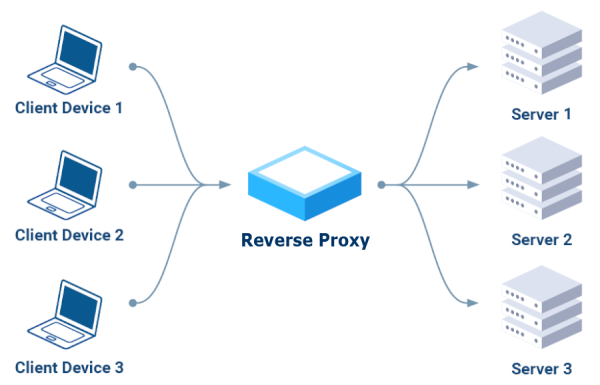
Die wichtigsten Vorteile:
Im Internet stehen verschiedene Tools zur Verfügung; nach eingehender Recherche haben wir zunächst diejenigen ausgeschlossen, die nur das HTTP-Protokoll (Schicht 7) unterstützen:
KEIN Apache-
„Oh je. Nehmen Sie sich einen Moment Zeit, um sich mit den Technologien vertraut zu machen, mit denen Sie arbeiten. E-Mails nutzen SMTP.
Apache nutzt HTTP. Apache hat absolut keine Ahnung von SMTP. Wenn Sie mit E-Mail-Nachrichten arbeiten möchten, benötigen Sie eine Technologie, die SMTP versteht.“
– EEAA, kommentiert am 18. August 2016 um 2:49 Uhr
NEIN Caddy
„Caddy kann kein TCP-Proxy sein, sondern nur HTTP über TCP.
Verwenden Sie einen Reverse-Proxy, der TCP-Proxy unterstützt, wie Traefik, Nginx oder haproxy, oder nutzen Sie dieses experimentelle Plugin.“
– ElevenNotes, kommentiert am 24. September 2024
Wir haben uns dann auf die drei in den Kommentaren empfohlenen Lösungen konzentriert: „Traefik, NginX oder HAProxy“, und sie nacheinander installiert und getestet.
Die meisten Anleitungen begannen mit Docker, einer Plattform, die ich vermeiden und stattdessen eine einfache Lösung wählen wollte, möglicherweise basierend auf einem der Linux-Paketmanager, wie beispielsweise YUM für RPM-basierte Distributionen wie Fedora und CentOS, oder APT (Advanced Package Tool), das bei Debian-basierten Distributionen wie Ubuntu und Debian zum Einsatz kommt.
Nach langer Suche sind wir auf diesen aktuellen Artikel gestoßen, der genau die Art der Installation beschreibt, nach der wir gesucht haben: Traefik als systemd-Dienst einrichten.
Ein Hinweis: Sie müssen die SELinux-Einstellungen von „Enforcing“ auf „Permissive“ ändern.
Nachdem wir erneut zwei Kurse auf Udemy ausprobiert hatten, stießen wir auf diesen hervorragenden Kurs:
Traefik Crash Course (ohne Docker)
Es gelang uns, das Tool zum Laufen zu bringen, indem wir die bereitgestellten Beispiele nachstellten.
Gegen Ende des Videos äußerte der hervorragende Kursleiter seine völlige Ablehnung gegenüber diesem Tool:
Traefik Crash Course – 53:50 Zusammenfassung.
Dies hielt uns von weiteren Tests ab, sodass wir uns entschlossen, etwas anderes auszuprobieren.
In diesem Fall war die Installation einfacher, kurz gesagt mit YUM:
yum install epel-release nginx nginx-mod-stream nginx-mod-mail
Hinweis: In SELinux müssen Sie „relay“ aktivieren:
setsebool -P httpd_can_network_relay 1
Für die Schulung sind wir auf Nummer sicher gegangen und haben denselben Dozenten wie beim letzten Kurs engagiert:
NginX-Crashkurs (der erste Teil endet nach etwa einer Stunde und zwanzig Minuten).
Auch der Kursleiter ist von dieser Anwendung NICHT überzeugt, insbesondere von der Tatsache, dass sie sowohl als Webserver als auch als Reverse-Proxy fungiert:
NginX-Crashkurs – 1:20:10 Zusammenfassung.
Der Bericht endet mit den Worten „Ich würde HAProxy gegenüber NginX vorziehen“, also haben wir beschlossen, auch HAProxy auszuprobieren.
Die Installation war kinderleicht, da es sich um eine sehr verbreitete Anwendung handelt, die in allen Linux-Paketmanagern verfügbar ist, zum Beispiel: yum install haproxy
Wir haben auch unseren bewährten Kursleiter zu Rate gezogen: HAProxy-Crashkurs.
Es funktioniert zwar, ist aber leider NICHT für die SMTP-Authentifizierung geeignet:
„Es ist nicht möglich, HAProxy auf diese Weise zu konfigurieren, da HAProxy SMTP überhaupt nicht unterstützt.“
– lukastribus, kommentiert am 17. August 2023
Nach zwei Wochen Testphase haben wir festgestellt, dass
es besser ist, einen Standard-SMTP-Server als Reverse-Proxy für andere SMTP-Server zu verwenden.
Es erfüllt seinen Zweck, nutzt ausschließlich das SMTP-Protokoll, authentifiziert Verbindungen ordnungsgemäß,
und kann Anfragen über die „smarhost“-Funktion an andere SMTP-Server weiterleiten.
In Postfix, in der Datei „main.cf“, wie folgt:
relayhost = [smarthost_address]:port
In Sendmail, in der Datei „sendmail.mc“, wie folgt
define(`SMART_HOST',`mail.example.com')
Manchmal haben Sie Daten von Ihrer Website oder Ihrer Unternehmenssoftware exportiert
, die Bestellinformationen oder Kundendaten enthalten.
Möglicherweise benötigten Sie nur die E-Mail-Adresse und das Bestelldatum.
Eine Möglichkeit besteht darin, alle Daten in Excel zu importieren, die unerwünschten Spalten zu löschen
und die verbleibenden zu exportieren.
This may not work well if the email field also contains the email address description,
for example: “Dave Martin <davemartin@bogusemail.com>”.
Es kann mühsam sein, wenn man die Aufgabe mehrmals wiederholen muss
oder wenn man alle Schritte jemand anderem erklären muss.
Ein regulärer Ausdruck (kurz „regex“ oder „regexp“ genannt),
ist eine Zeichenfolge, die ein Muster angibt, nach dem im Text gesucht wird.
Ein ganz einfacher Fall ist es, ein Wort, das auf zwei verschiedene Arten geschrieben wird, in einem Texteditor zu finden,
der reguläre Ausdruck seriali[sz]e passt sowohl auf „serialise“ als auch auf „serialize“.
Eine komplexere Situation stellt die Syntax zur Identifizierung im Text dar
eine E-Mail-Adresse:
[a-zA-Z0-9._-]+@[a-zA-Z0-9._-]+\.[a-zA-Z0-9_-]+
Quelle: Stack Overflow – E-Mail-Adressen mit regulären Ausdrücken aus Zeichenfolgen extrahieren
ein Datum:
\d{4}-\d{2}-\d{1,2}
Quelle: Stack Overflow – Regulärer Ausdruck zum Extrahieren eines Datums aus einer Zeichenfolge
Empfohlenes YouTube-Video
„38 Minuten, die sich gelohnt haben, das war es absolut wert “:
So finden Sie beliebige Textmuster
(ab Minute 25 wird die Syntax zum Extrahieren von E-Mail-Adressen erklärt)
Spickzettel zur Verwendung regulärer Ausdrücke
Reguläre Ausdrücke werden in der Regel
in fortgeschrittenen Texteditoren wie Notepad++ oder Atom unterstützt.
Es stehen auch kostenlose Online-Tools zur Verfügung, darunter:
https://regexr.com – ein Online-Dienst zum Erlernen, Erstellen und Testen regulärer Ausdrücke.
Erläuterung der Weboberfläche:
„Expression“ ist das Feld, in das die Regex-Syntax eingegeben wird.
„Text“ ist der Inhalt, den Sie analysieren möchten.
Unter „Tools > List“ werden die Ergebnisse der Extraktion angezeigt.
Ausdruck:
[a-zA-Z0-9._-]+@[a-zA-Z0-9._-]+\.[a-zA-Z0-9_-]+
Text:
Dave Martin
615-555-7164
173 Main St., Springfield RI 55924
davemartin@bogusemail.com
Charles Harris
800-555-5669
969 High St., Atlantis VA 34075
charlesharris@bogusemail.com
Eric Williams
560-555-5153
806 1st St., Faketown AK 86847
laurawilliams@bogusemail.comExtras > Liste:
$&\n
Ergebnis:
davemartin@bogusemail.com
charlesharris@bogusemail.com
laurawilliams@bogusemail.comAusdruck:
","(.*?)([a-zA-Z0-9._-]+@[a-zA-Z0-9._-]+\.[a-zA-Z0-9_-]+)(.*?)",".*",(\d{2}\.\d{2}\.\d{4})
Text:
"lorem ipsum dolor sit amet","Robert Farrell <rmfarrell@bogusemail.com>","",02.01.2024, ,5379,
"consectetur adipiscing elit","""Mesa, Rene <rmesa@bogusemail.com>""","",04.01.2024, ,20826,
"sed do eiusmod tempor incididunt","Antonio Bugan <antonio@bogusemail.com>","",04.01.2024, ,2856,
"ut labore et dolore magna aliqua","Crawley Down Tennis Club <hello@bogusemail.com>","",05.01.2024, ,4453,Extras > Liste:
$2,$4\n
Ergebnis:
rmfarrell@bogusemail.com,02.01.2024
rmesa@bogusemail.com,04.01.2024
antonio@bogusemail.com,04.01.2024
hello@bogusemail.com,05.01.2024. - Any Character Except New Line
\d - Digit (0-9)
\D - Not a Digit (0-9)
\w - Word Character (a-z, A-Z, 0-9, _)
\W - Not a Word Character
\s - Whitespace (space, tab, newline)
\S - Not Whitespace (space, tab, newline)
\b - Word Boundary
\B - Not a Word Boundary
^ - Beginning of a String
$ - End of a String
[] - Matches Characters in brackets
[^ ] - Matches Characters NOT in brackets
| - Either Or
( ) - Group
Quantifiers:
* - 0 or More
+ - 1 or More
? - 0 or One
{3} - Exact Number
{3,4} - Range of Numbers (Minimum, Maximum)Quelle: GitHub-Codeausschnitte
Die meisten Unternehmen und öffentlichen Einrichtungen registrieren mehrere Domainnamen.
Unternehmen erwerben oft mehr als eine Domain, um sich gegen Nutzerfehler abzusichern und ihre Marken zu schützen.
In anderen Fällen dienen sie dazu, Veranstaltungen oder Projekte zu bewerben, die besondere Aufmerksamkeit verdienen.
Die Zahlen können bei einer einzelnen Aktivität von einigen Dutzend Domains bis zu mehreren Hundert variieren.
Sie reichen von etwa zweihundert in einer Stadtverwaltung einer Großstadt bis hin zu Tausenden bei Ferrari und Goldman Sachs.
Die Zahlen sind geradezu atemberaubend, wenn man die Gesamtzahl der registrierten Domains betrachtet:
Laut Verisign belief sich diese Zahl Ende 2022 auf 350 Millionen Domainnamen.
Viele dieser Domains dienen lediglich als „Visitenkarte“. Auf der Website sind keine E-Mail-Adressen angegeben.
Kontaktanfragen werden in der Regel auf auszufüllende Formulare oder auf Social-Media-Kanäle weitergeleitet.

Die Verwaltung von E-Mail-Versendungen mit den erforderlichen Authentifizierungsverfahren (SPF, DKIM, DMARC usw.) wird immer komplexer.
Aus diesem Grund wird in der Regel nur eine einzige Domain tatsächlich für die offizielle externe Kommunikation per E-Mail genutzt.
Der Gedanke, die eigene Online-Präsenz zu schützen, kann sich jedoch als zweischneidiges Schwert erweisen.
Falsch konfigurierte „Showcase-Domains“ können von böswilligen Akteuren leicht ausgenutzt werden.
Oft nutzen sie den bekannten Namen des Absenders aus, um das Vertrauen der Empfänger zu gewinnen und sie dazu zu bewegen,
vertrauliche Informationen preiszugeben oder Links und Anhänge zu öffnen.
Die Empfänger laufen Gefahr, die Sicherheit ihrer Systeme zu gefährden,
wodurch Banden digitaler Krimineller Zugriff von außen erhalten.

Die oben erwähnten komplexen Authentifizierungssysteme haben auch ihre positiven Seiten.
Das DMARC-Protokoll wurde entwickelt, um gegen gefälschte E-Mails vorzugehen,
und zu verhindern, dass unbefugte Personen oder Organisationen sich als unsere Absender ausgeben.
Mit einer schnellen Einrichtung können Sie angeben, dass eine bestimmte Domain NICHT in Gebrauch ist,
und Empfänger warnen, E-Mails von dieser Domain abzulehnen.
Es reicht aus, einen Eintrag (eine einzelne Zeile) mit folgendem Hinweis in das DNS der Domain einzufügen:
_dmarc.yourdomain.com. TXT "v=DMARC1; p=reject"
Ob diese Regel gilt, hängt vom System ab, das die Nachrichten empfängt.
Die gute Nachricht ist, dass das DMARC-Protokoll seit März 2015 ein anerkannter IETF-Standard ist.
Die meisten Online-E-Mail-Dienste setzen es ein, um ihre Nutzer zu schützen.
Nachrichten von „NO-MAIL“-Domains werden automatisch zurückgewiesen.
Auf diese Weise schützen Sie Ihr Unternehmen nicht nur vor Missbrauch, sondern verhindern auch, dass „alte“ Domains wie
,
die nicht mehr zum Versenden von E-Mails berechtigt oder authentifiziert sind, versehentlich verwendet werden.
Im E-Mail-Posteingang herrscht ein reger Wettbewerb um die Aufmerksamkeit der Verbraucher,
was es für Unternehmen umso schwieriger macht, von ihren Kunden und Interessenten wahrgenommen zu werden.
Es wird immer schwieriger, jemanden dazu zu bringen, eine wichtige E-Mail zu lesen (oder ihn überhaupt ans Telefon zu bekommen)
.
48 % der Verbraucher haben mehr als 50 ungelesene Nachrichten in ihrem Posteingang.
Die meisten Verbraucher verzichten darauf, ungelesene Nachrichten zu löschen, sodass sich die E-Mails immer weiter stapeln.
– Quelle: ZipWhip „Warum Ihre Kunden Ihre E-Mails nicht mehr lesen“ (PDF, 15 MB)
Manche Updates sind dringend und können von entscheidender Bedeutung sein. Der Versand per E-Mail birgt das Risiko
,
dass die Nachricht nicht gelesen wird oder im Spam-Ordner landet.
Auf die Frage „Wie viele E-Mail-Konten haben Sie?“ antworteten 77 % mit „zwei oder mehr“.
In der Regel ist auf dem Smartphone nur eines davon eingerichtet.

Es kommt immer häufiger vor, dass man Kunden anruft und KEINE Antwort erhält
oder dass der Anruf auf die Voicemail umgeleitet wird
.
97 % der Verbraucher geben zu, Anrufe von Unternehmen und unbekannten Nummern zu ignorieren.
– Quelle: ZipWhip „Warum Ihre Kunden nicht mehr ans Telefon gehen “ (PDF, 15 MB)
Durch Covid-19 hat die Nutzung elektronischer Geräte zugenommen,
64 % der Befragten gaben an: „Ich verbringe mehr Zeit mit meinem Handy“.
58 % der Verbraucher geben an, dass SMS für Unternehmen der effektivste Weg ist, sie schnell zu erreichen.
– Quelle: ZipWhip State of Texting 2021 (PDF, 21 MB)
Selbst im E-Commerce, wo für die Registrierung normalerweise eine E-Mail-Adresse erforderlich ist,
bieten einige große Unternehmen, darunter Amazon, die Möglichkeit, sich über die Handynummer zu registrieren.
Es ist unmittelbar
SMS-Nachrichten werden fast immer gelesen, meist schon Sekunden nach dem Empfang.
Die Öffnungsrate liegt bei über 95 % (von diesen 95 % erfolgen 90 % innerhalb von drei Minuten nach Zustellung).
SMS-Nachrichten sind kurz und prägnant, die Kommunikation ist auf das Wesentliche beschränkt und erfolgt unmittelbar.
Es ist ganz einfach:
Sie benötigen keine Internetverbindung, um ihren Empfänger zu erreichen.
So kann Ihre Marke Zielgruppen erreichen, die sich mit Technologie nicht so gut auskennen.
Die Nutzung ähnelt der von Videoinhalten (schnell, unmittelbar, in 160 Zeichen zu vermitteln).
Es ist allgegenwärtig
SMS ist mit jedem Mobiltelefon auf der Welt kompatibel, ohne dass neue Apps installiert werden müssen.
Das Smartphone (oder ein Mobiltelefon der älteren Generation) ist wie der Geldbeutel und die Hausschlüssel immer griffbereit.
Es bietet die Möglichkeit, über einen zuverlässigen Kanal mit einem Kunden zu interagieren, egal wo er sich gerade befindet.
Es ist günstig
Das Versenden von SMS-Nachrichten ist kostengünstig.
Die durchschnittliche Länge der versendeten Nachrichten beträgt nicht mehr als 155 Zeichen (das Limit liegt bei 160 Zeichen pro Nachricht).
Die Kombination von SMS mit Telefonaten oder E-Mails kann bei der Kommunikation mit Kunden Zeit sparen.
Es ist interaktiv
Die Kommunikation erfolgt über einen „unbelasteten“ Kanal, sie wird nicht „aufgedrängt“ und wirkt nicht „aufdringlich“.
SMS werden als wichtiger eingestuft, sie werden eher geöffnet und gelesen. Außerdem ist die Wahrscheinlichkeit höher, dass sie beantwortet werden.
Die Sprache von Textnachrichten ist einfach und fördert die Interaktion. Die Antwortraten liegen bei bis zu 45 %.
Zurückgesendete E-Mails oder einfach „Bounces“ sind E-Mails, die automatisch
von einem MTA (Mail Transfer Agent) an den Absender gesendet werden,
um ihn darüber zu informieren, dass die Nachricht beim Empfänger NICHT korrekt angekommen ist
Der Betreff lautet in der Regel „Zurückgesendete E-Mail: Details siehe Transkript“.
Die erläuternden Informationen zur Fehlermeldung, bestehend aus einem Code mit einer Beschreibung, finden Sie im Text der E-Mail.
Der „Statuscode“ sollte eindeutig die Art des Fehlers angeben, der die Rückmeldung verursacht hat
, doch oft müssen die von den einzelnen E-Mail-Anbietern verwendeten Codes und Beschreibungen
analysiert und interpretiert werden, um den Bounce korrekt einzuordnen.
Das Versenden von E-Mails an falsche oder inaktive Empfänger gilt als „Spam-Verhalten“.
Wenn Sie den Rest Ihrer Liste erreichen möchten, sollten Sie am besten keine E-Mails mehr an den „schlechten“ Teil davon senden.
Manchmal wird dies als „Listenpflege“ bezeichnet.
Es gibt drei Arten von Zustellstatusbenachrichtigungen (DSN):
Erfolg – Die E-Mail wurde zugestellt (die Benachrichtigung wird nur gesendet, wenn der Absender dies wünscht)
Hard Bounce – Es ist ein permanenter Fehler aufgetreten
Soft Bounce – Es ist ein vorübergehender Fehler aufgetreten
Hard Bounce (Statuscode 5.XXX.XXX): Die E-Mail-Adresse hat einen permanenten Fehler generiert
wie z. B. „550 5.1.1 … Benutzer unbekannt“ oder „5.1.2 … Host unbekannt“
Ein permanenter Fehler bedeutet, dass Sie niemals wieder an diesen Empfänger senden sollten.
Eine einzige zurückgewiesene Nachricht sollte die Sperrung der E-Mail-Adresse auslösen.
Soft Bounce (Statuscode 4.XXX.XXX): Die E-Mail-Adresse hat einen vorübergehenden Fehler verursacht
wie z. B. „452 4.2.2 … Postfach voll“
Ein vorübergehender Fehler bedeutet, dass Sie die Zustellung zu einem späteren Zeitpunkt erneut versuchen können.
Mindestens drei zurückgewiesene Nachrichten innerhalb weniger Tage sollten die Sperrung der E-Mail-Adresse auslösen.
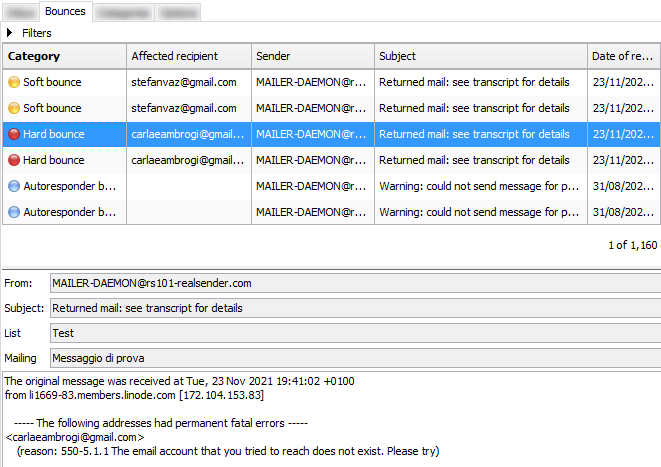
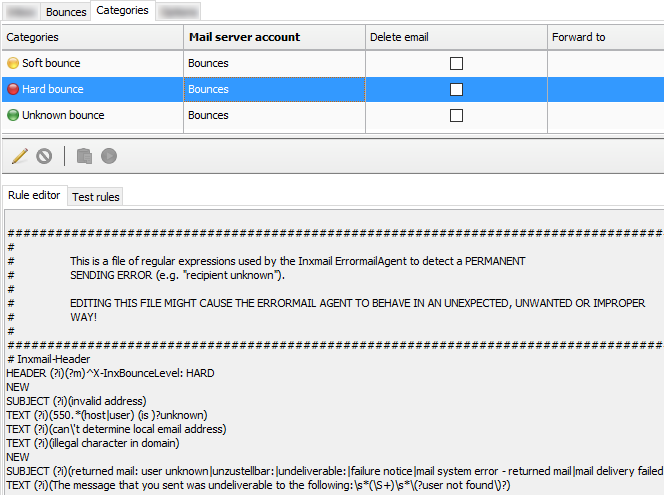
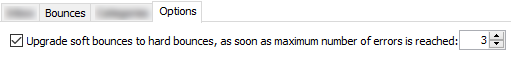
Manchmal kann ein Konfigurationsfehler sowohl auf der Seite des Absenders als auch auf der Seite des Empfängers
zu einem Soft-Bounce oder sogar zu einem Hard-Bounce führen.
Es empfiehlt sich, regelmäßig die Anzahl der in der letzten Woche zurückgesendeten Nachrichten unter
zu überprüfen,
um festzustellen, ob die Werte unverändert geblieben sind oder ob Abweichungen vorliegen.
Sollte etwas nicht stimmen, werden Sie dies sofort bemerken.
Ein Blick auf die Details der Rückläufer hilft Ihnen dabei, die Ursache zu ermitteln.
Bei einigen Systemen können Sie die Anzahl der Tage (z. B. 180) festlegen,
nach deren Ablauf die Bounce-Informationen eines Abonnenten gelöscht werden.
Auf diese Weise versucht der SMTP-Server, den Empfänger erneut zu kontaktieren.
Versehentlich aktivierte Sperren werden automatisch aufgehoben
, doch die Reputation des SMTP-Servers kann darunter leiden.
Kurz gesagt: Vorbeugen ist besser als heilen.
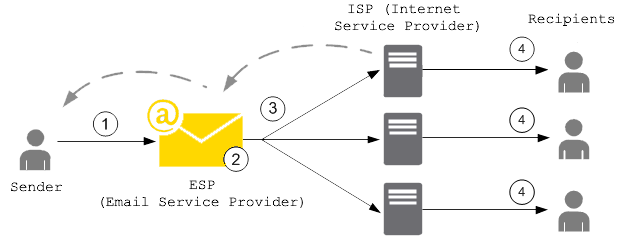
Um Rufschädigungen ihrer SMTP-Server zu vermeiden,
nutzen immer mehr ESPs (E-Mail-Dienstleister) eine„E-Mail-Sperrliste“
, die greift, bevor die Nachrichten das Postfach des Empfängers erreichen.
Wenn ein Kunde eine E-Mail sendet, die zu einem Hard Bounce führt,
wird die E-Mail-Adresse, die den Bounce verursacht hat, zur Sperrliste hinzugefügt.
Die Sperrliste gilt für alle Kunden. Mit anderen Worten:
Wenn ein anderer Kunde versucht, eine E-Mail an eine Adresse zu senden, die auf der Sperrliste steht,
wird diese vom SMTP-Server nicht versendet, da die E-Mail-Adresse gesperrt ist.
Durch die Verwendung von SMTP-Servern mit dedizierter IP-Adresse lassen sich einige Probleme im Zusammenhang mit der gemeinsamen Nutzung von Reputationswerten vermeiden.
So kann beispielsweise die „E-Mail-Sperrliste“ ausschließlich auf Ihre IP-Adresse beschränkt werden,
sodass Ihre Mailings nicht beeinträchtigt werden, falls ein anderer Kunde eine Sperrung des SMTP-Servers und die damit verbundenen Bounce-Meldungen verursacht,
.
Statuscodes zur Kennzeichnung von Hard Bounces und Soft Bounces haben folgende Syntax:
status-code = class „.“ subject „.“ detail
Statuscodes bestehen aus drei durch „.“ getrennten Ziffernfeldern
Der Untercode (Klasse) dient der allgemeinen Klassifizierung des Status.
Die für jede Klasse aufgeführten Werte sind in den RFC 3463 und RFC 6522 wie folgt definiert:
2.XXX.XXX Erfolg (wird nur auf Anfrage des Absenders gesendet)
„Erfolg“ gibt an, dass die DSN eine erfolgreiche Zustellung meldet.
Detaillierte Untercodes können Hinweise auf für die Zustellung erforderliche Anpassungen enthalten.
4.XXX.XXX Anhaltender vorübergehender Fehler
Ein anhaltender vorübergehender Fehler liegt vor, wenn die gesendete Nachricht zwar gültig ist,
aber das Fortbestehen einer vorübergehenden Situation dazu geführt hat, dass der Versuch, die Nachricht zu versenden, abgebrochen oder verzögert wurde.
Wenn dieser Code mit einem Zustellungsfehlerbericht einhergeht, kann der Versand in Zukunft erfolgreich sein.
5.XXX.XXX Dauerhafter Fehler
Ein dauerhafter Fehler ist ein Fehler, der durch erneutes Senden der Nachricht in der aktuellen Form wahrscheinlich nicht behoben werden kann.
Für eine erfolgreiche Zustellung müssen Änderungen an der Nachricht oder am Zielort vorgenommen werden.Einige Beispiele für Code und Beschreibungen:
2.0.0: Gesendet (Nachricht zur Zustellung angenommen)
4.2.2: Kontingent überschritten
4.4.5: Nicht genügend Speicherplatz
5.0.0: Ungültiger Domänenname
5.1.1: Benutzer unbekannt
5.7.1: Inhalt der Nachricht abgelehntAngesichts der steigenden Zahl von Ransomware-Angriffen in den 2020er Jahren
– ist E-Mail, unser wichtigster Kommunikationskanal im Internet, noch sicher?
SMTP-Server sind eine besonders sensible Infrastruktur.
Sie können in unserem Namen E-Mail-Nachrichten versenden,
die unsere Empfänger als von vertrauenswürdigen Absendern stammend anerkennen,
da sie vom sendenden Server korrekt authentifiziert werden.
SMTP-Server sind eine besonders sensible Infrastruktur.
Sie versenden in unserem Namen E-Mail-Nachrichten,
die unsere Empfänger als von vertrauenswürdigen Absendern stammend anerkennen,
da sie vom SMTP-Server des Absenders ordnungsgemäß authentifiziert werden.
Was passiert, wenn jemand anderes Ihren SMTP-Server nutzt?
Wie kann ich überprüfen, ob mein SMTP-Server sicher ist?
Die Nutzung sensibler Infrastrukturen im Internet
erfordert ein hohes Maß an Schutz, um Missbrauch zu verhindern.
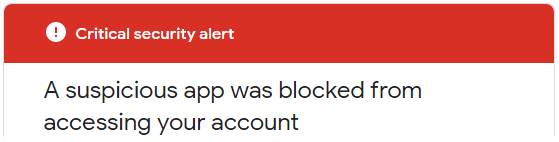
Wenn Sie versuchen, Nachrichten über smtp.gmail.com
zu versenden,
werden Sie blockiert und erhalten folgende „kritische Sicherheitswarnung“:
Weniger sichere App blockiert
Google hat die App, die Sie nutzen wollten, blockiert,
da sie unseren Sicherheitsstandards nicht entspricht. [...]Die einzige Alternative ist die Verwendung von OAuth2, einem Protokoll, bei dem keine Passwortdaten weitergegeben werden
sondern stattdessen Autorisierungstoken zum Identitätsnachweis verwendet werden.
Die am häufigsten verwendeten Mailserver im Internet (Stand: August 2021) sind:
Exim (58 %), Postfix (35 %), Sendmail (4 %)
Um Ihren eigenen Mailserver
weiterhin nutzen zu können
und das Risiko eines Hackerangriffs zu verringern,
sollten Sie folgende Mindestanforderungen überprüfen:
Es werden nur sichere Authentifizierungs
akzeptiert.
Benutzername und Passwort müssen über sichere Verbindungen übertragen werden,
in der Regel Port 587+TLS oder Port 25+TLS oder Port 465+SSL
Die Übertragung sensibler Daten im Klartext ist deaktiviert.
Die „Mail-From“-Adresse (der Absender) muss überprüft werden:
Nur von Ihnen autorisierte Absender werden zugelassen
Konfigurieren Sie Fail2ban so, dass alle externen Angriffe blockiert werden
, um Versuche zu verhindern, Ihre Sicherheitsvorkehrungen zu umgehen.
Insbesondere sollte Fail2ban alle wiederholten Versuche blockieren:
Die Sperre tritt in der Regel nach drei bis zehn Versuchen ein
und sperrt die Quell-IP für drei bis vierundzwanzig Stunden.
Es ist ganz einfach, diese Punkte zu überprüfen und zu entscheiden, ob
Ihre SMTP-Infrastruktur eine Sicherheitsaktualisierung benötigt.
Fail2ban schützt Ihren Server vor Brute-Force- und DDoS-Angriffen.
Das funktioniert so, als würde ein Fremder an die Tür klopfen,
und nach einer bestimmten Anzahl von Schlägen verschwindet die Tür.

Ein Erfahrungsbericht von Hacker News:
Ich betreibe seit mehreren Jahren meinen eigenen Mailserver und ich glaube, viele andere hier
nutzen Lösungen wie Mail-in-a-box, mailcow, Mailu usw.
Bis zur Corona-Pandemie hatte ich nie größere Probleme mit meinem Mailserver, aber in den letzten Wochen
hatte ich sehr hohen eingehenden Datenverkehr – das war zu viel für meinen Server und ich musste ihn jedes Mal manuell neu starten ...
[...] Edit: Ich habe meine Fail2ban-Einstellungen geändert und festgestellt, dass ich hauptsächlich Ziel
von Brute-Force-Angriffen war, gegen die ich mich mit Tools wie Fail2ban schützen können sollteFail2ban ist eine Anwendung zur Protokollauswertung, die Systemprotokolle
auf Anzeichen eines automatisierten Angriffs überwacht.
Wenn anhand der definierten Parameter ein Missbrauchsversuch erkannt wird,
fügt Fail2ban der Firewall (iptables oder firewalld) eine neue Regel hinzu
, um die IP-Adresse des Angreifers entweder für einen festgelegten Zeitraum oder dauerhaft zu sperren.
Fail2ban kann Sie zudem per E-Mail darüber informieren, dass ein Angriff stattfindet.
Fail2ban konzentriert sich in erster Linie auf SSH-Angriffe, kann jedoch unter
so konfiguriert werden, dass es für jeden Dienst funktioniert, der Protokolldateien verwendet und potenziell angegriffen werden kann.
Es ist weit verbreitet. Wenn man bei Google danach sucht, findet man leicht
Konfigurationsbeispiele zum Schutz von Mail-Servern.
Welche DNS-Einstellungen sind für den Versand von E-Mails erforderlich?
E-Mail-Anbieter verlangen in der Regel, dass Sie die Domain des Absenders
verifizieren, bevor Sie ihre SMTP-Server nutzen können. Dafür gibt es zwei Gründe:
Domain-Inhaberschaft nachweisen
Durch die Verwaltung des DNS weisen Sie nach, dass Sie die Kontrolle über die Absender-Domain haben
Das bedeutet, dass Sie nicht die Domain einer anderen Person verwenden (Spoofing)
Versenden von authentifizierten E-Mails
Durch die Einrichtung der SPF- und DKIM-Authentifizierung werden Ihre Nachrichten
von den Empfängern als von einem „echten“ Absender stammend erkannt
Wenn Ihre Domain und Ihr SMTP-Anbieter einen guten Ruf genießen
sollten die Nachrichten den Posteingang der Empfänger erreichen
Zusammenfassung:
Nachfolgend finden Sie einige der wichtigsten Anbieter, die wir geprüft haben, in alphabetischer Reihenfolge.
Ende Juli 2021 haben wir die Grundeinstellungen getestet, die für den Versand von E-Mails erforderlich sind.
Die verifizierte Domain lautete „emailperfect.com“. Sie wurde 2012 registriert und zuvor noch nie zum Versenden von E-Mails verwendet.
| Name des Anbieters | DKIM-Domänenabgleich für die Absenderadresse „ “ |
SPF-„Mail-From“- -Domänenabgleich |
Anmerkungen |
|---|---|---|---|
| Amazon SES | Ja (3 CNAME-Einträge) | NEIN (@amazonses.com) | |
| Mailgun | Ja (TXT-Eintrag) | Ja (TXT-Eintrag) | Zustellungsprüfung für Hotmail und Yahoo* |
| Mailjet | Ja (TXT-Eintrag) | NEIN (@mailjet.com) | Zustellungsprüfung für Hotmail und Yahoo* |
| RealSender | Ja (2 CNAME-Einträge) | Ja (TXT-Eintrag) | feste IP-Adresse |
| Sendgrid | Ja (2 CNAME-Einträge) | Ja (CNAME-Eintrag) | Zustellungsprüfung für Hotmail* |
| Smtp2go | Ja (1 CNAME-Eintrag) | Ja (CNAME-Eintrag) |
* = Wir haben eine Nachricht an jede der folgenden E-Mail-Adressen gesendet und vermerkt, ob es Anzeichen dafür gab, dass wir es noch einmal versuchen sollten:
Gmail, Hotmail, Yahoo, GMX, Aruba, Tiscali, Exchange Online
Im Jahr 2021 halten wir es für zwingend erforderlich, dass die Domain des Absenders authentifiziert wird
, damit der Empfänger sicher sein kann, dass die E-Mail-Adresse des Absenders nicht gefälscht wurde.
Eine vorausschauende Authentifizierungsprüfung verringert zudem das Risiko des Missbrauchs von Versandsystemen erheblich.
Aus diesem Grund haben wir einen Anbieter aus der Liste „gelöscht“:
Dieser Anbieter verlangt keine Domain-Validierung, bevor er das Versenden von Nachrichten zulässt.
Beim Versenden einer Nachricht haben wir es mit zwei Domänen zu tun:
Die Anforderung der „Domänenübereinstimmung“ lässt sich in diesem Satz zusammenfassen:
„Wenn ein Absender seine E-Mail mithilfe von SPF und/oder DKIM authentifiziert,
muss mindestens eine der Domänen mit der Absender-Domäne übereinstimmen.“
Für die DKIM-Authentifizierung ist ein CNAME-Eintrag einfacher zu implementieren.
Das gleiche Ergebnis lässt sich durch Hinzufügen eines 2048-Bit-TXT-Eintrags erzielen, dies ist jedoch komplizierter.
Darüber hinaus ermöglicht die Delegierung des DKIM-Eintrags über CNAME Ihrem Provider
, seinen Schlüssel bei Bedarf aus Sicherheitsgründen zu ändern.
Bei der SPF-Authentifizierung mittels eines CNAME-Eintrags bedeutet dies, dass die „Mail-From“-Adresse
eine von Ihrem E-Mail-Dienstanbieter verwaltete Subdomain ist, beispielsweise: bounce.your-company-name.org.
Der Anbieter übernimmt sowohl die SPF-Authentifizierung als auch die Bearbeitung von zurückgesendeten Nachrichten.
Ein TXT-Eintrag für die SPF-Authentifizierung ist die beste Wahl bei E-Mail-Servern wie Zimbra oder Exchange,
wo jeder Absender die zurückgewiesenen Nachrichten direkt erhält.
Es gibt nur einen TXT-Eintrag für die Domain-Authentifizierung,
was die Verwaltung erschweren kann, wenn Sie mehrere SMTP-Server verwalten.
Die „Internetprotokolladresse“ oder „IP-Adresse“
ist vergleichbar mit einer Telefonnummer Ihres Festnetzanschlusses oder Mobiltelefons.
Die meisten SMTP-Dienste stellen ihren Kunden „gemeinsam genutzte“ IP-Adressen zur Verfügung.
Bei jedem Versand einer E-Mail wird eine andere IP-Adresse zugewiesen.
„Feste IP-Adresse“ bedeutet, dass sich die IP-Adresse, von der aus Ihre E-Mails versendet werden, im Laufe der Zeit nicht ändert.
Dies ermöglicht eine hervorragende Kontrolle über die Reputation des Absenders, die nicht durch die Nutzung durch Dritte beeinträchtigt werden kann.
Nicht unbedingt, denn dafür sind gewisse technische Kenntnisse erforderlich.
Die Unternehmensleitung sollte sich bewusst sein, dass bereits wenige Änderungen an den DNS-Einstellungen
schwerwiegende Folgen haben können, wie zum Beispiel:
Wie verwaltet man Mailinglisten mit Weitsicht?
Zunächst einmal: Warum sollte man einen Mailinglisten-Manager nutzen?
CRM-Systeme (wie Salesforce und Microsoft CRM)
und geschäftliche E-Mail-Dienste (wie Office 365 und Google Apps Gmail)
sind für Massenversendungen nicht geeignet.
Sie wurden für die Eins-zu-Eins-Kommunikation entwickelt.
Oftmals werden zur Vermeidung von Missbrauch tägliche Versandlimits festgelegt.
Häufig müssen Unternehmen E-Mails an die meisten ihrer Kontakte oder an ausgewählte Gruppen versenden.
Massenversendungen müssen mit speziellen Systemen verwaltet werden,
die in der Lage sind, große Mengen an Nachrichten zu verarbeiten und automatische Abmeldungen zu bearbeiten.
Zweiter Schritt: Wo findet man diese Lösungen?
Die einfache Antwort lautet: Schauen Sie sich „SaaS“-Angebote – Software as a Service – an
(Mailchimp ist das bekannteste System, Inxmail ist weniger bekannt, wird aber von großen Unternehmen genutzt).
Die Entscheidung zwischen lokaler Installation und Cloud-Diensten ist immer wichtig.
Wir sind der Meinung, dass die lokale Option dabei hilft, die „Kontrolle über E-Mails zurückzugewinnen“, was wir befürworten.
Selbst wenn Sie sich für eine selbst gehostete Anwendung in der Cloud entscheiden,
können Sie so problemlos den Anbieter wechseln, während Sie dieselbe Lösung beibehalten.
Drei Lösungen sind erwähnenswert:
Auf der Suche nach einer übersichtlichen Benutzeroberfläche, einer auf Listen basierenden Lösung, die leicht zu warten
und im Falle von Problemen einfach wiederherzustellen ist, haben wir uns für listmonk als beste Wahl entschieden.
listmonk ist ein selbst gehosteter, leistungsstarker Manager für Mailinglisten und Newsletter.
Es wird als eigenständige Binärdatei bereitgestellt und benötigt lediglich eine Postgres-Datenbank.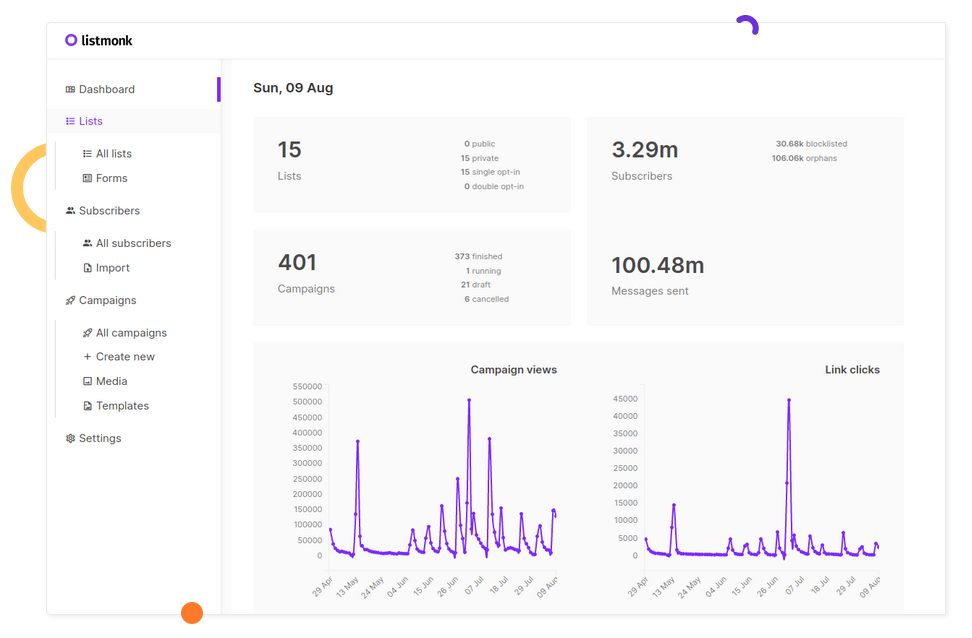
Dies ist die ursprüngliche Ankündigung auf Hacker News:
knadh am 12. Juli 2019 [–]
Der Autor hier. Um etwas Kontext dazu zu geben, warum listmonk entwickelt wurde: Bei meiner Arbeit (im regulierten Finanzgeschäft)
müssen wir regelmäßig E-Mails, meist wichtige Updates, an über 1,5 Millionen Kunden versenden.
Wir haben lange Zeit phpList verwendet und dann MailTrain und Sendy ausprobiert, bevor wir uns schließlich entschlossen haben, das Rad neu zu erfinden,
nachdem wir auf eine Reihe von Problemen gestoßen waren, von denen einige wichtige unten aufgeführt sind.
- Leistung. Unangemessen lange Wartezeiten beim Versenden von E-Mails.
phpList wurde so langsam, dass die Verarbeitung einer Kampagne mehrere Tage dauerte.
listmonk kann N Goroutinen (~Threads) starten und E-Mails an mehrere SMTP-Server senden.
Auf einer Standard-EC2-Instanz können wir über 1,5 Millionen E-Mails in wenigen Stunden versenden.
- Der Import von Abonnenten war extrem langsam. Die direkte Integration zur Synchronisierung der Abonnenten mit externen CRMs war umständlich.
Direkte DB-Einfügungen waren aufgrund der komplexen Tabellenstrukturen kompliziert. listmonk importiert 10.000 Datensätze pro Sekunde in eine Postgres-Datenbank auf einer Standard-EC2-Instanz.
- Segmentierung. Oft müssen wir Nutzer schnell anhand benutzerdefinierter Attribute und Bedingungen segmentieren und ihnen eine Aktualisierung übermitteln.
listmonk unterstützt SQL-Ausdrücke, um Nutzer anhand ihrer Attribute zu segmentieren, die als beliebige JSON-Maps definiert sind (dank des Postgres-Typs JSONB).
- Fehlende dynamische Vorlagen. listmonk-Vorlagen unterstützen Go-Template-Ausdrücke, sodass es möglich ist, Logik in Nachrichten zu schreiben, um diese dynamisch zu gestalten.Kailash Nadhisist ein sehr aktiver Entwickler im Bereich FOSS (Free and Open Source Software).
Er arbeitet bei Zerodha, Indiens größtem Online-Broker.
Der Blog der technischen Mitarbeiter von Zerodha wird unter zerodha.tech veröffentlicht.
Listmonk ist sowohl für die Standardnutzung (über die Weboberfläche) als auch für Entwickler (über die API) gut dokumentiert.
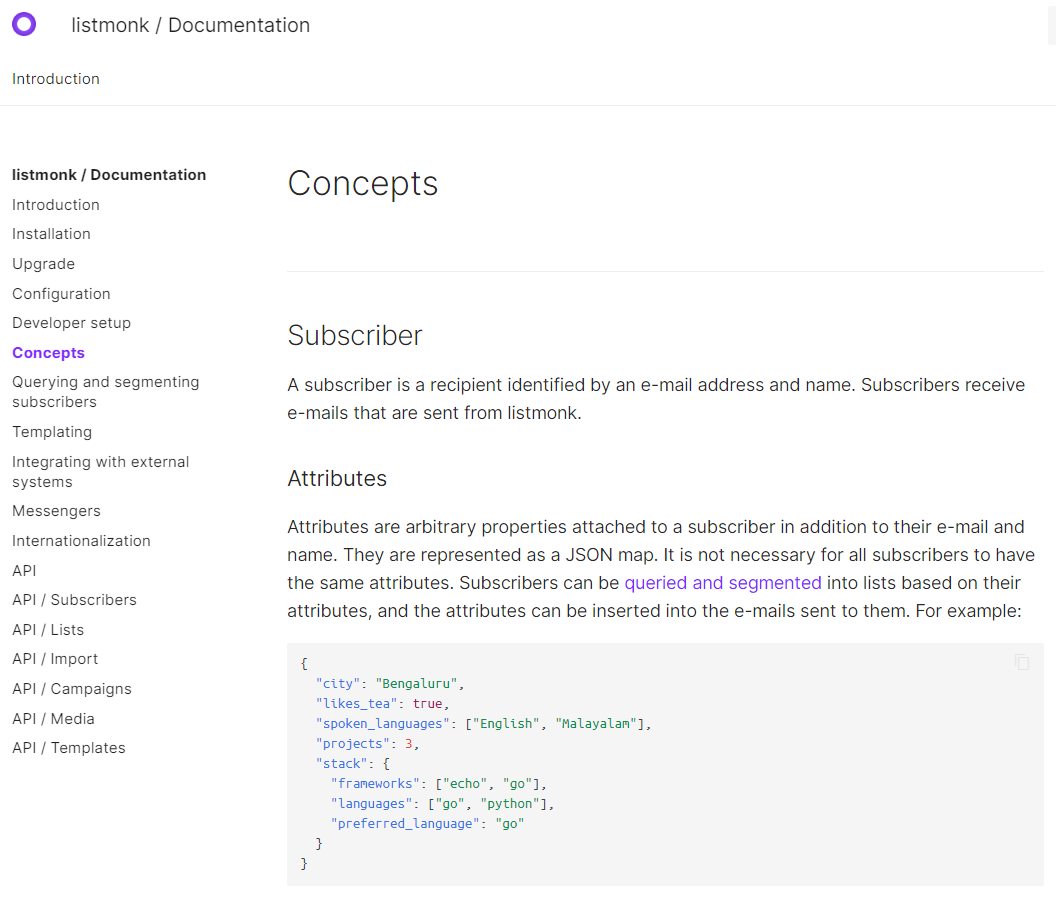
Die Lösung eignet sich sowohl für große Verteilerlisten (mit bis zu Millionen von Abonnenten) als auch für kleine Gruppen.
Dank der Funktion zum Abfragen und Segmentieren von Abonnenten,
können Sie eine Auswahl von Abonnenten anhand ihrer Profile und Attribute abfragen und exportieren.
Die extrahierten Daten lassen sich problemlos in eine neue zielgerichtete Mailingliste importieren.
Es fehlen einige wichtige Funktionen wie die Bearbeitung von E-Mail-Bounce-Meldungen.
Diese sollten jedoch in der nächsten Hauptversion verfügbar sein:
Bounce-Bearbeitung #166
Vorschau auf den Screenshot zur Bounce-Bearbeitung
Wir haben in der Vergangenheit eine andere Go-Anwendung verwendet: RealSender – DMARC REPORTS.
Quelle: dmarc-report-converter. Es funktionierte sofort und ohne Probleme.
„Das Datenbankmanagementsystem PostgreSQL, auf das mehr als zwei Jahrzehnte Entwicklungsarbeit zurückblicken,
ist heute die fortschrittlichste Open-Source-Datenbank, die es gibt.“
– Eine kurze Geschichte von PostgreSQL – https://www.postgresql.org/docs/9.3/history.htmlWir haben damit bereits einige Erfahrungen gemacht, als wir in der Vergangenheit mit der Installation des Inxmail Professional-Servers gearbeitet haben.
Im Jahr 2017 gab die Inxmail GmbH bekannt, dass sie künftig ausschließlich PostgreSQL unterstützen und alle anderen Datenbanken einstellen werde:
Ab dem 1. Januar 2019 konzentrieren wir uns auf die optimale technische Basis und stellen den Support
für Windows-Server sowie für MySQL-, Oracle- und MS SQL Server-Datenbanken ein.
Das bedeutet, dass wir nur noch Support für Inxmail Professional auf Basis von Linux-Servern und PostgreSQL anbieten.
-- Inxmail Professional-Lizenzlösung: Änderungen bei unserem System-Support
https://www.inxmail.de/files/files/de/downloads/Inxmail-Professional-licence-solution-EN.pdfDas ist sicherlich eine gute Wahl und eine Investition in wertvolles Wissen für Einsteiger.
Die Online-Kurse von Udemy können bei der Erstinstallation und Wartung von PostgreSQL helfen.
Open Source birgt Risiken: Wird ein neues Projekt, das 2019 gestartet wurde, auch in Zukunft weitergeführt?
Das weiß niemand; vielleicht kümmert sich im schlimmsten Fall ein anderer Entwickler darum, aber:
E-Mail-Zustellbarkeit, Fragen und Antworten:
hemancuso am 12. Juli 2019 [–]
Projekte wie dieses scheinen eine großartige Idee zu sein, doch die Zustellbarkeit scheint ein großes Problem zu sein,
das sich nur schwer messen lässt, wenn man nicht über ausreichende Erfahrung verfügt.
Was sind bewährte Vorgehensweisen für die Nutzung/Auswahl eines ESP,
wenn man ein solches Projekt nutzen und eine angemessene Zustellbarkeit sicherstellen möchte?
knadh am 12. Juli 2019 [–]
Hier spricht der Autor. Wir nutzen Listmonk in unserem Unternehmen (reguliertes Finanzgeschäft) bereits seit über 6 Monaten in der Produktion,
um E-Mail-Updates, einschließlich regulatorischer Mitteilungen, zu versenden.
Wir hosten unsere eigenen SMTP-Instanzen mit Postal auf EC2-Instanzen und hatten noch nie Probleme mit der Zustellbarkeit.
Wenn es sich um legitime E-Mails handelt, halte ich das nicht für ein großes Problem.Wir sind uns einig, dass das Versenden von erwarteten Mitteilungen an Kunden dazu beitragen sollte, die meisten Zustellungsprobleme zu vermeiden.
Unserer Erfahrung nach steigt die Wahrscheinlichkeit von Problemen mit zunehmender Anzahl.
AWS-EC2-Server werden in Gmail häufig auf die Blacklist gesetzt – alle gesendeten Nachrichten landen im Spam-Ordner.
RealSender bietet dedizierte IP-SMTP-Server an,
die in einer zuverlässigen und ständig überwachten Umgebung betrieben werden.
goberoi am 13. Juli 2019 [–]
Eine ganz spontane Frage: Wie bist du auf den Namen gekommen?
knadh am 13. Juli 2019 [–]
Ich kann mich nicht mehr genau erinnern, aber ich glaube, der Gedankengang war in etwa:
„stressfreie, unkomplizierte Listenverwaltung“.Mit dem Docker-Image können Sie innerhalb weniger Minuten eine funktionsfähige Demo-Installation einrichten.
Alternativ können Sie bei RealSender ein Listmonk-Demo-Konto anfordern.
Nach der Aufnahme in die Blacklist antwortet der Kundensupport eines großen Anti-Spam-Dienstes oft:
„Bitte überprüfen Sie die Qualität Ihrer Liste, um sicherzustellen, dass die Empfänger an Ihren Mailings interessiert sind.“
„Listenpflege“ und „Interesse der Empfänger“ haben viele Facetten:
A – auf der MASCHINENSEITE – „Listenpflege“
ordnungsgemäß verwaltete An- und Abmeldungen
Der Abonnent muss seine E-Mail-Adresse bestätigt haben (Double-Opt-in),
Empfänger sollten sich einfach und zuverlässig abmelden können (Opt-out)
Versenden Sie E-Mails nur an „aktive“ und voll engagierte Empfänger
Versenden Sie keine E-Mails wiederholt an Empfänger mit ungültigen Adressen oder vollen Postfächern
Stellen Sie den Versand an inaktive Empfänger ein; wenn diese nicht interagieren, ist dies ein klares Zeichen für mangelndes Interesse
Der Inhalt muss gut strukturiert sein (kein einzelnes Bild) und „responsive“ sein, damit er auf verschiedenen Geräten lesbar ist
Andernfalls könnten Spamfilter die Nachricht blockieren, bevor sie den Posteingang des Empfängers erreicht
Stellen Sie sicher, dass die Server erkennen, wer die E-Mail sendet
Durch die E-Mail-Authentifizierung können die Ziel-Mailserver Nachrichten als von vertrauenswürdigen Absendern stammend identifizieren
B – auf der MENSCHLICHEN Seite – „Interesse des Empfängers“
Abonnenten sollten die Inhalte erwarten, die sie erhalten
Die Empfänger sollten sich auf Ihre Nachricht freuen und sie zu schätzen wissen
Benutzerantworten sollten verwaltet werden
Manchmal läuft etwas schief oder ein Empfänger möchte einfach mit Ihnen in Kontakt treten,
vielleicht nur, um Ihnen mitzuteilen, dass er keine weiteren Nachrichten mehr erhalten möchte, auch wenn ein Abmeldelink vorhanden ist
Die oben aufgeführten Punkte lassen sich bei kleinen Verteilerlisten mit einigen hundert Empfängern problemlos bewältigen.
Oft kennt der Absender sie persönlich, da es sich um Kunden oder Mitglieder eines Vereins handelt.
Es wird kompliziert, wenn die Liste größer ist, mit Tausenden von Empfängern
und mehr Personen an den Mailings arbeiten.
In diesem Fall ist der Einsatz professioneller Tools unerlässlich.
Im Internet gibt es viele professionelle Lösungen für das E-Mail-Marketing,
die international bekannteste ist MailChimp
viele Websites listen auch Alternativen zu MailChimp auf.
Die Mission von EmailTrends lautet: „Die Kontrolle über E-Mails zurückgewinnen“,
Aus diesem Grund schlagen wir eine Alternative vor.
Laut W3Techs laufen 40 % aller Websites im Internet auf WordPress
und es ist die beliebteste Technologie im gesamten Internet in der Kategorie Open Source.


Mit über 200.000 aktiven Installationen ist Mailpoet
eines der meistgenutzten WordPress-Plugins für Newsletter.
MailPoet ist eine Open-Source-Software undgehört seit Ende 2020
zu den Unternehmen, die mit Automattic, der Muttergesellschaft von WordPress,verbunden sind.
Einige Screenshots vermitteln Ihnen vielleicht einen Eindruck davon, wie die verschiedenen Punkte umgesetzt werden:
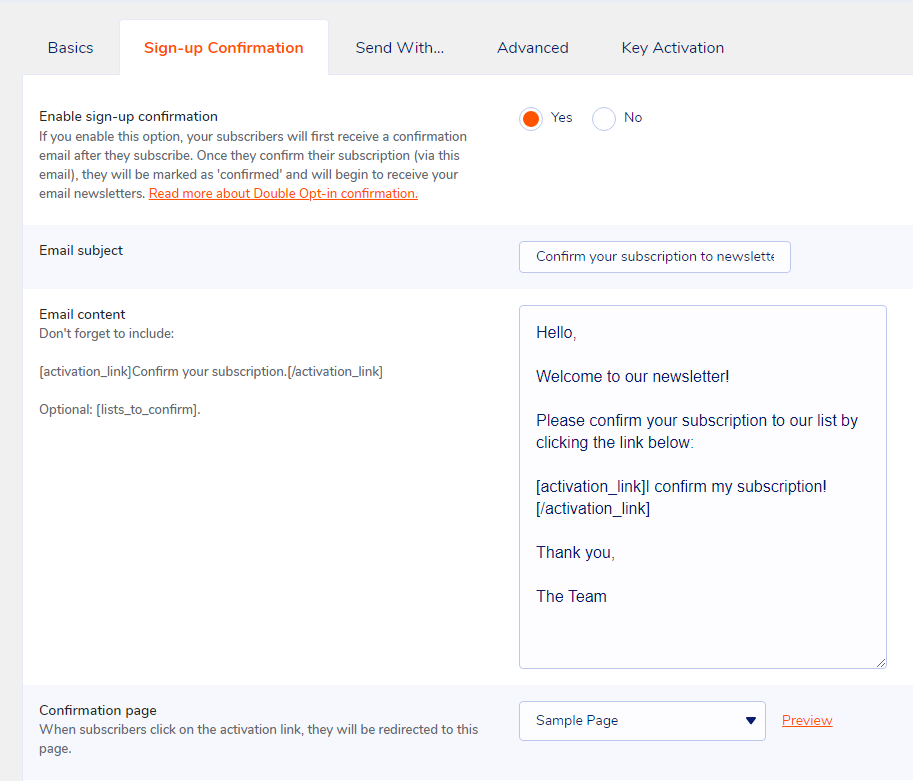
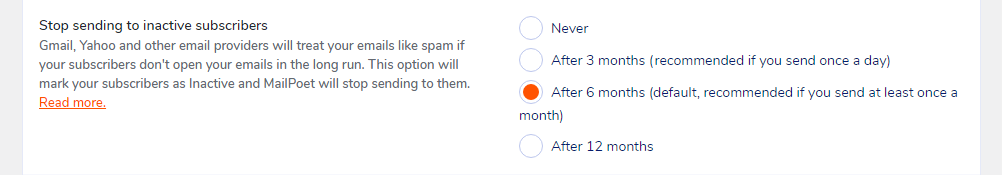
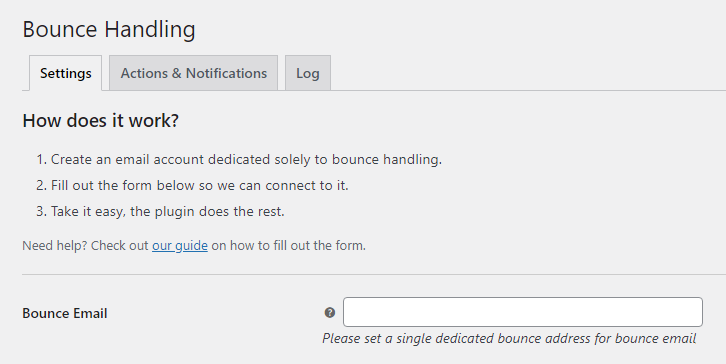
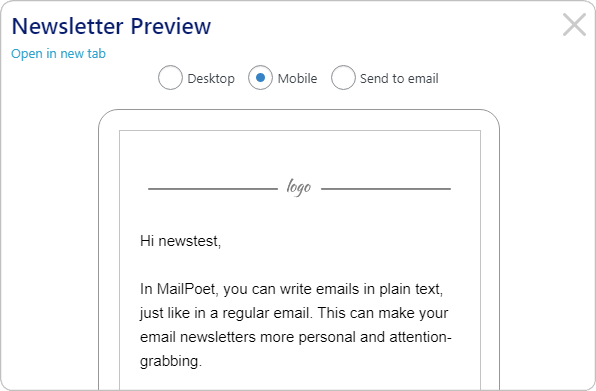
Mailpoet verfolgt ein „Freemium“-Geschäftsmodell, bei dem Sie folgende Option wählen können:
„Ich möchte nur die Premium-Version ohne Versandfunktion“.
Der dedizierte SMTP-Server von RealSender kann über die Option „Senden mit… > Andere“ konfiguriert werden.
Das Plugin „Bounce Handler MailPoet“ sorgt in Verbindung mit den von RealSender bereitgestellten Newsletter-Postfächern
für die korrekte Authentifizierung der versendeten E-Mail-Nachrichten.
Die menschliche Seite ist schwieriger zu erreichen,
sie ist aber auch der Punkt, der den Unterschied ausmacht
wenn das technische Management nicht perfekt ist.
„BE RELEVANT“
ist ein Slogan, der vor einigen Jahren im E-Mail-Marketing verwendet wurde.
Wenn du wertvolle Informationen an Menschen sendest
die du nach langen Gesprächen sehr gut kennst,
spielt es keine Rolle, wie schlecht die Formatierung ist
oder ob die Nachricht im Spam-Ordner landet.
Technische Unvollkommenheiten werden immer verziehen,
sie warten auf Ihre E-Mails, lesen Sie diese
und klicken Sie gegebenenfalls auf die Schaltfläche „Kein Spam“.
Wie versendet man private und verschlüsselte E-Mails?
E-Mails sind weder privat noch sicher.
Sie wurden nicht unter Berücksichtigung von Datenschutz oder Sicherheit entwickelt.
Jeder, der Ihre E-Mail während der Übertragung abfängt, kann sie lesen,
einschließlich Ihres Internetanbieters, eines Hackers oder der NSA (US-amerikanische Nationale Sicherheitsbehörde).
Zusammenfassung:
„Der Wert einer Information wird erst dann deutlich, wenn man sie
mit etwas anderem verknüpfen kann, das zu einem späteren Zeitpunkt eintrifft.
Da man keine Punkte verbinden kann, die man nicht hat, treibt uns das in einen Modus,
in dem wir grundsätzlich versuchen, alles zu sammeln und für immer festzuhalten.“
„Sie haben gesagt, es seien nur Metadaten, es seien nur Metadaten, […]
mit wem man spricht, wann man mit ihnen spricht, wohin man gereist ist.
Das sind alles Metadaten-Ereignisse.
Bei PRISM geht es um Inhalte. […] Sie können alles sehen, weil es unverschlüsselt ist.“
Es gibt Dutzende psychologischer Studien, die belegen
, dass Menschen, die wissen, dass sie beobachtet werden könnten,
sich wesentlich konformistischer und gefügiger verhalten.
[…] Massenüberwachung schafft ein Gefängnis im Kopf […]
Betrüger könnten auch Malware einsetzen, um in das Computernetzwerk eines Unternehmens einzudringen
und Zugriff auf E-Mail-Korrespondenz zu finanziellen Angelegenheiten zu erlangen.
Business Email Compromise (BEC) – auch bekannt als Email Account Compromise (EAC)
– ist eine der finanziell schädlichsten Formen der Online-Kriminalität.
Bei einem BEC-Betrug versenden Kriminelle eine E-Mail, die scheinbar von einer bekannten Absenderadresse stammt
und eine legitime Anfrage enthält […]
Anonymität ist etwas anderes als Vertraulichkeit
[…] wir verschlüsseln Nachrichten
damit andere, selbst wenn sie sehen, dass wir eine Nachricht gesendet haben
nicht lesen können, was darin steht
aber manchmal wollen wir gar nicht, dass andere überhaupt sehen, dass wir eine Nachricht gesendet haben
Anonymität im Internet ist schwer zu erreichen.
Dazu sind fundierte Kenntnisse der von Ihnen gewählten Tools erforderlich.
Dieser Leitfaden vermittelt Ihnen vielleicht einen Eindruck von der Komplexität des Themas:
Private E-Mail-Anbieter
Vertraulichkeit ist leichter zu erreichen.
Auch wenn Sie nichts zu verbergen haben, trägt die Verwendung von Verschlüsselung
dazu bei, die Privatsphäre Ihrer Kommunikationspartner zu schützen
und macht Massenüberwachungssystemen das Leben schwer.
Wenn Sie etwas Wichtiges zu verbergen haben, sind Sie in guter Gesellschaft;
Es handelt sich um dieselben Tools, die Whistleblower nutzen, um ihre Identität zu schützen
und gleichzeitig Menschenrechtsverletzungen, Korruption und andere Verbrechen ans Licht zu bringen.
Der entscheidende erste Schritt besteht darin, sich selbst zu schützen
und die Überwachung Ihrer Kommunikation so weit wie möglich zu erschweren.
Durch eine End-to-End-Verschlüsselung (e2ee) für E-Mails kann sichergestellt werden,
dass nur der Absender und die Empfänger einer Nachricht den Inhalt lesen können.
Ohne diesen Schutz können Netzwerkadministratoren,
E-Mail-Anbieter und Behörden Ihre Nachrichten leicht einsehen.
Die Umsetzung von End-to-End-Verschlüsselung erfordert Sorgfalt sowohl seitens des Absenders als auch seitens der Empfänger.
Ein einziger Fehler einer der beteiligten Parteien kann bereits ausreichen, um die Sicherheit der End-to-End-Verschlüsselung zu gefährden.
E-Mail-Metadaten wie Absender- und Empfängeradresse sowie Datum und Uhrzeit können nicht durch End-to-End-Verschlüsselung geschützt werden.
Auch der Betreff der E-Mail bleibt möglicherweise ungeschützt und leicht lesbar, selbst wenn End-to-End-Verschlüsselung verwendet wird.

Die PGP-Software folgt dem OpenPGP-Verschlüsselungsstandard, dem
Standard (RFC 4880) zum Ver- und Entschlüsseln von Daten.
PGP verschlüsselt den Text Ihrer E-Mail in einen Code
, den nur die richtige Person lesen kann.
PGP läuft auf so gut wie jedem Computer oder Smartphone.
Es ist frei lizenziert und kostet nichts.
Jeder Benutzer verfügt über einen eindeutigen öffentlichen Schlüssel und einen privaten Schlüssel,
die aus zufälligen Zahlenfolgen bestehen.
Dein öffentlicher Schlüssel ist nicht wie ein physischer Schlüssel, denn er befindet sich in einem Online-Verzeichnis, von dem andere ihn herunterladen können.
Andere verwenden deinen öffentlichen Schlüssel zusammen mit PGP, um E-Mails zu verschlüsseln, die sie an dich senden.
Dein privater Schlüssel ähnelt eher einem physischen Schlüssel, da du ihn für dich behältst (auf deinem Computer).
Du verwendest PGP und deinen privaten Schlüssel, um verschlüsselte E-Mails zu entschlüsseln, die andere dir senden.
Wenn eine mit PGP verschlüsselte E-Mail in die falschen Hände gerät, sieht sie einfach wie Unsinn aus.
Ohne den privaten Schlüssel des tatsächlichen Empfängers ist es fast unmöglich, sie zu lesen.
Um uns vor Überwachung zu schützen, müssen wir lernen, wann wir PGP nutzen sollten
und damit beginnen, unsere öffentlichen Schlüssel weiterzugeben, wann immer wir E-Mail-Adressen austauschen.
Um PGP zu nutzen, benötigen Sie einen öffentlichen Schlüssel und einen privaten Schlüssel (zusammen als Schlüsselpaar bezeichnet).
Beide bestehen aus einer langen Zeichenfolge zufällig generierter Zahlen und Buchstaben, die für Sie einzigartig ist.
Ihr öffentlicher und Ihr privater Schlüssel sind durch eine spezielle mathematische Funktion miteinander verknüpft.
Es wird eine Anwendung benötigt, die die Schlüssel sowie die Ver- und Entschlüsselung von Nachrichten verwaltet,
hier ist eine Auswahl der beliebtesten Anwendungen:
Mailvelope ist ein kostenloses Open-Source-Browser-Plugin, das für Mozilla Firefox und Google Chrome verfügbar ist:
Es ist wahrscheinlich der einfachste Einstieg in PGP:
„Mailvelope Demonstration“ist ein gut gemachtes Tutorial
Die Anwendung Mozilla Thunderbird bietet alle notwendigen Funktionen zum Versenden von PGP-signierten Nachrichten
Einführung in die End-to-End-Verschlüsselung in Thunderbird
GnuPG ist eine vollständige und kostenlose Implementierung des OpenPGP-Standards
Ein PGP-Leitfaden für Anfänger mit Gpg4Win [Einfache Einrichtung in 5 Minuten] erklärt, wie man es benutzt
PGP ist die beste Lösung für eine sichere Kommunikation mit einem Partner, der PGP bereits nutzt.
Es könnte schwierig sein, Ihren Gesprächspartner dazu zu bewegen, PGP zu nutzen.
Eine Alternative sind Dienste, mit denen man ein Geheimnis nur einmal weitergeben kann.
Wenn Sie etwas nur einmal versenden möchten, gibt es Open-Source-Webanwendungen
,
mit denen Sie Informationen eingeben können, die nur einmal angezeigt werden können.
Sobald der Empfänger die Seite geöffnet hat, werden die Informationen gelöscht,
und in Ihren Chat-Protokollen oder E-Mails bleibt lediglich ein ungültiger Link zurück.
Es ist zwar nicht so sicher, als würde Ihr gesamtes Team PGP verwenden, aber es lässt sich viel einfacher einrichten und erklären.
Wir konnten damit Anmeldedaten an Personen senden, die technisch nicht besonders versiert sind, und diese fanden die Handhabung einfach.
Beispiel (ohne Passwort hinzuzufügen):
Nehmen wir an, du hast ein Passwort. Du möchtest es deiner Kollegin Jane geben.
Du könntest es ihr per E-Mail schicken, aber dann befindet es sich in ihrer E-Mail, die möglicherweise gesichert wird,
und wahrscheinlich auf einem Speichermedium landet, das von der NSA kontrolliert wird.
Wenn Jane einen Link zum Passwort erhält und ihn nie anklickt, verschwindet das Passwort.
Wenn die NSA den Link in die Hände bekommt und das Passwort ansieht … nun, dann hat sie das Passwort.
Außerdem kann Jane das Passwort nicht erhalten, aber jetzt weiß Jane, dass nicht nur jemand ihre E-Mails durchstöbert,
sondern auch auf Links klickt.Einige dieser Dienste, die alle kostenlos und Open Source sind, sind unten aufgeführt.
Sie können sich auch dafür entscheiden, eine Instanz auf Ihrem eigenen Webserver zu hosten.
PrivateBin (eine Art sichere Version von PasteBin) wurde in PHP entwickelt
Der Code von PrivateBin ist auf GitHub veröffentlicht – 3100 Sterne
Eine Anleitung für PrivateBin ist auf einer anderen Website verfügbar
OneTimeSecret wurde in Ruby entwickelt
Der Code und die Anleitung zu OneTimeSecret sind auf GitHub veröffentlicht – 1200 Sterne
SnapPass wurde in Python geschrieben. Es wurde ursprünglich von Pinterest entwickelt
Der SnapPass-Code und die Anleitung sind auf GitHub veröffentlicht – 600 Sterne
Wie versendet und begrenzt man E-Mails mit Bcc?
„Cc“ steht für „Carbon Copy“ im (alten) Sinne der Anfertigung einer Kopie
auf einer Schreibmaschine unter Verwendung von Kohlepapier.
Das Feld „Bcc:“ in E-Mails (wobei „Bcc“ für „Blind Carbon Copy“ steht)
enthält die Adressen von Empfängern der Nachricht
, deren Adressen den anderen Empfängern der Nachricht nicht offenbart werden sollen.
– IETF RFC 2822 „Internet Message Format“
Der Unterschied zwischen „Bcc“ und „Cc“ liegt in der Anonymität der Empfänger.
Bei Verwendung der Cc-Funktion sind die E-Mail-Adressen im Cc-Feld
für alle Empfänger der E-Mail sichtbar.
Ein Bcc-Empfänger kann den direkten Empfänger (An:) sehen,
er kann jedoch nicht erkennen, wer sonst noch per Bcc in die E-Mail aufgenommen wurde.
Bcc wird oft als benutzerfreundliches System für den Massenversand von E-Mails angesehen.
Im Folgenden finden Sie eine kurze Analyse der Vor- und Nachteile der Verwendung von Bcc.
Am Ende der Seite finden Sie die Schlussfolgerungen sowie einige Vorschläge.
Es ist ganz einfach: Jeder kann es benutzen.
E-Mail ist ein Ausgangs-Gateway ohne vorherige Überprüfung.
Über „Bcc“ lässt sich die Reichweite auf Hunderte oder Tausende von Kontakten ausweiten.
Bcc sollte als risikoreiches,
potenziell gefährliches Kommunikationsmittel betrachtet werden.
Wie lässt sich die Leistung Ihrer E-Mail-Marketing-Kampagnen messen?
Die folgenden Informationen basieren auf unserer fünfzehnjährigen Erfahrung
mit der E-Mail-Marketing-Plattform Inxmail.
Was sind „E-Mail-Marketingkampagnen“?
Es handelt sich um umfangreiche, auf Einwilligung basierende E-Mails,
deren Inhalt in der Regel auf die Interessen des Empfängers zugeschnitten ist,
und bei denen der Absender anhand des Verhaltens der Empfänger Feedback-Daten erhalten kann.
Die Antworten oder „Feedback-Daten“ bilden die Grundlage für die Kennzahlen
, auf denen die Berichte zur Performance von E-Mail-Marketingkampagnen basieren.
Lassen Sie uns einen Überblick darüber geben, was diese Kennzahlen sind und wie sie gemessen werden:
Selbst die besten technischen Tools nützen nichts, wenn die Nachrichten nicht im Posteingang des Empfängers ankommen.
Hier kommt die „E-Mail-Zustellbarkeit“ ins Spiel:
Permission-Marketing, auch „Dialog-Marketing“ genannt,
ist ein Konzept, das Seth Godin 1999 in seinem Bestseller „Permission Marketing“ vorgestellt hat.
In dem Buch wird es als Gegenstück zum „Interruptionsmarketing“ definiert
, das üblicherweise in traditionellen Massenmedien wie Fernsehen und Zeitungen zum Einsatz kommt.
Ziel ist es, eine persönliche und direkte Kommunikation herzustellen,
eine Beziehung zwischen den beiden Parteien aufzubauen und einen „menschlichen“ Dialog in Gang zu setzen,
dessen Erfahrung für beide Seiten nützlich und bereichernd ist.
Je nach den erteilten Datenschutzberechtigungen kann der Absender Folgendes aufzeichnen:
Aggregierte Daten
Sie liefern allgemeine Rückmeldungen und Informationen zu allgemeinen Trends
(z. B. wie viele die E-Mail geöffnet haben, wie viele darauf geklickt haben)
Einzelbenutzer-Daten
Sie ermöglichen es, individuelle Informationen zu erhalten
durch die Erfassung personenbezogener Daten und das anschließende Versenden personalisierter Nachrichten
auf der Grundlage früherer Interaktionen und des Nutzerverhaltens
Unter Link-Tracking versteht man das Ersetzen der endgültigen URL der Website
durch eine fiktive Adresse, die den Besuch erfasst und den Nutzer auf die Zielseite weiterleitet.
In E-Mail-Nachrichten können nur Klicks auf Links nachverfolgt werden.
Externe Bilder, bei denen der E-Mail-Client vor dem Herunterladen um Bestätigung bittet,
werden als Links behandelt. Daher reicht es aus, die URL eines externen Bildes zu tracken
, um die E-Mail-Öffnungsrate zu ermitteln.
Bei der Nachverfolgung wird in der Regel nur die „Mail-ID“ erfasst,
eine eindeutige Kennung der versendeten E-Mail.
Die personalisierte Nachverfolgung erfolgt durch Hinzufügen eines oder mehrerer von der Software generierter Parameter zu den besuchten Seiten,
wie zum Beispiel: example.com/test.html?id=54725788327466628654
Der Parameter „id“ bezieht sich auf einen bestimmten Nutzer und einen bestimmten Link in der Nachricht.
Die gewonnenen Informationen können automatisch
die Daten des Empfängers in der E-Mail-Marketing-Anwendung
aktualisieren oder die Angaben zur Herkunft des Klicks an die Webanalyse-Plattform weiterleiten.
Beispiel: Ein Reisebüro könnte unter
erfassen, wie oft der Nutzer auf Nachrichten zum Thema „Meer“ oder „Berge“ klickt,
wodurch sich ein bestimmter Zähler im Laufe der Zeit erhöht.
Die gesammelten Daten geben Aufschluss über das bevorzugte Reiseziel des Empfängers.
Die Öffnungsraten werden ermittelt, indem Daten zu Klicks auf nachverfolgte Links
und zu „verborgenen Klicks“ kombiniert werden, die durch heruntergeladene, nachverfolgte Bilder generiert wurden.
Wenn eine Nachricht in der Vorschau des E-Mail-Clients geöffnet wird,
ohne dass die Bilder heruntergeladen oder Links angeklickt werden,
ist es nicht möglich zu erkennen, dass sie geöffnet wurde.
Seit 2003 – zunächst Outlook, dann die meisten E-Mail-Clients –
begannen zum Schutz der Privatsphäre ihrer Nutzer
den automatischen Download von Bildern zu blockieren
, die andernfalls bei jedem Gelesen einer E-Mail nachverfolgt worden wären.
Seit 2013 werden Bilder in Gmail standardmäßig automatisch angezeigt.
Der Download erfolgt über einen Drittanbieter-Server, einen sogenannten „Proxy“,
der das Endgerät des Nutzers verbirgt, es den Betreibern von E-Mail-Marketing-Kampagnen
jedoch dennoch ermöglicht, zu erkennen, dass das Bild heruntergeladen und die Nachricht geöffnet wurde.
Weitere Informationen finden Sie hier:
So funktioniert der neue Gmail-Bild-Proxy und was das für Sie bedeutet
Die Erfassung der Öffnungsraten ist ungenau;
liefert einen niedrigeren Wert als die tatsächlichen Öffnungen.
Es ist dennoch sinnvoll, diese zu messen,
und sei es nur, um die Ergebnisse verschiedener Kampagnen zu vergleichen.
Zunächst muss überprüft werden, ob die E-Mails in den Postfächern
der wichtigsten Freemail-Domains aus Ihrer Liste
sowie im Posteingang der beiden wichtigsten Anbieter von Unternehmens-E-Mail-Konten
– Google Apps und Office 365 – ankommen.
Inhaltsbasierte Spamfilter werden in der Regel durch Domains in URLs (http …) ausgelöst
Ein guter Tipp ist es, in den Links Ihrer Nachrichten nur eine einzige Domain zu verwenden.
Die Domain sollte mit der in der Absenderadresse verwendeten übereinstimmen;
Dies wird als „Domain-Alignment“ bezeichnet und verringert das Risiko, von Phishing-Filtern erfasst zu werden.
Aus demselben Grund sollten Links, sofern sie getrackt werden, eine Subdomain
der in der Absenderadresse verwendeten Domain nutzen.
Echte Tests lassen sich ganz einfach durchführen, indem Sie für jeden E-Mail-Anbieter ein „Test“-Postfach aktivieren:
und anschließend die Weiterleitung der Nachrichten an Ihre E-Mail-Adresse aktivieren:
Senden Sie an jedes Postfach eine Nachricht mit dem Betreff „Testnachricht“
und dem Inhalt „Testnachricht“ sowie dem Link zu Ihrer Domain:
Wenn die Nachricht die Spamfilter passiert, sollten Sie sie in Ihrem Posteingang erhalten.
Es ist normal, dass E-Mails als unzustellbar zurückkommen.
Dies kann an nicht mehr genutzten Adressen,
überfüllten Postfächern oder anderen technischen Problemen liegen.
Je nach „Sauberkeit“ Ihrer Liste,
kann die Absprungrate zwischen 5 % und 20 % schwanken.
Mit steigender Anzahl wird es unmöglich, die zurückgewiesenen E-Mails manuell zu verwalten.
E-Mail-Marketing-Anwendungen verfügen über eine Funktion namens „Bounce Handler“
die zurückgewiesene Nachrichten automatisch herunterlädt,
sie analysiert und entsprechend ihrem Inhalt klassifiziert.
Die Ziel-E-Mail-Adresse wird automatisch deaktiviert
nach einer bestimmten Anzahl von „Hard Bounces“ – also dauerhaften Fehlern wie „Benutzer unbekannt“ und „Host nicht erreichbar“
– oder nach einer größeren Anzahl von „Soft Bounces“ – also vorübergehenden Fehlern wie „Postfach voll“.
Es ist wichtig, die „Bounce-Raten“ (abgewiesene Nachrichten)
oder die komplementären „Zustellungsraten“ (angenommene Nachrichten) zu überwachen. Ihre Summe ergibt 100 %.
Eine Veränderung ihrer Werte ist ein Anzeichen, das untersucht werden sollte.
Die größten E-Mail-Marketing-Plattformen veröffentlichen Vergleichszahlen
,
die auf den von all ihren Kunden gesammelten Daten basieren.
In den Berichten verwendete Fachbegriffe:
Hier ist eine kurze Liste; die meisten davon beziehen sich auf die USA:
Zu den Kunden von Mailchimp zählen Ein-Personen-Startups,
kleine Unternehmen bis hin zu „Fortune 500“-Unternehmen,
das gesamte Spektrum ist in diesen Daten vertreten
Campaign Monitor hat über 100 Milliarden E-Mails analysiert, die weltweit
zwischen Januar und Dezember 2020 versendet wurden
Der achte jährliche Deliverability-Benchmark-Bericht von Return Path
um zu sehen, wie viele E-Mails im Posteingang, im Spam-Ordner oder blockiert gelandet sind.
Inhalt des Deliverability-Benchmark-Berichts 2020 (PDF):
Was versteht man unter Zustellbarkeit und wie wird sie gemessen?
Was passiert mit einer E-Mail, nachdem man auf „Senden“ geklickt hat?
Wie viele E-Mails landen weltweit durchschnittlich im Posteingang und im Spamfilter?
Zustellbarkeitsstatistiken für 30 einzelne Länder
Welche Nutzer und Mailserver werden als Spam-E-Mails eingestuft?
Ausgehend von unseren Erfahrungen mit RealSender,
haben wir versucht, die wichtigsten Punkte zusammenzufassen, die die Zustellung in den Posteingang beeinflussen können.
Es ist sinnlos, die anderen Punkte zu prüfen
, wenn die Nachrichten von den Empfängern nicht erwartet oder gewünscht werden.
Der Absender sollte sich in die Lage des Empfängers versetzen und versuchen, sich vorzustellen, wie eine E-Mail-Nachricht aufgenommen wird.
Beschwerden von Nutzern können dazu führen, dass der gesamte SMTP-Server oder der Domainname auf eine Blacklist gesetzt wird, was sich auf die Zustellung aller zukünftigen Nachrichten auswirkt.
Es sind grundlegende technische Einstellungen erforderlich, damit E-Mails zugestellt werden können.
Verwenden Sie E-Mail-Authentifizierungsmethoden wie SPF und DKIM, um nachzuweisen, dass Ihre E-Mails und Ihr Domainname zusammengehören.
Ein positiver Nebeneffekt ist, dass Sie damit dazu beitragen, zu verhindern, dass Ihre E-Mail-Domain gefälscht wird.
Der einzig sichere Weg, um festzustellen, ob eine E-Mail als Spam eingestuft wird, ist…
sie zu versenden und zu sehen, wie sie beim Empfänger angezeigt wird.
Wie kann man mit einsatzbereiten Open-Source-E-Mail-Clients wieder die Kontrolle über seine E-Mails erlangen?
In den letzten zehn Jahren hat sich der Bereich der Unternehmens-E-Mail-Postfächer
fast vollständig gewandelt: weg von lokalen E-Mail-Servern hin zu Cloud-Diensten wie Exchange Online (Office 365) oder Gmail for Business (Google Apps).
Die Hauptgründe dafür sind:
Auf diese Weise wurde das Leben von IT-Fachkräften vereinfacht, indem
die Verantwortung für die Verwaltung der E-Mail-Infrastruktur auf die „großen Tech-Unternehmen“ abgewälzt wurde.
Das Risiko, grundlegende E-Mail-Kenntnisse zu vernachlässigen, kann dazu führen, dass wir E-Mail-
als etwas betrachten, das wie von Zauberhand funktioniert, nur weil Microsoft und Google sich darum kümmern.
Wir können die Kontrolle über unsere E-Mails zurückgewinnen, indem wir die einzelnen Komponenten des E-Mail-Systems aufschlüsseln und separat verwalten:
Dies sorgt für eine Isolierung und Segmentierung der Dienste und trägt erheblich zur Sicherheit bei.
Daher gilt die Verringerung der Angriffsfläche durch Isolierung/Segmentierung als bewährte Vorgehensweise.
Zudem erhöht dies die Skalierbarkeit und Stabilität.
E-Mail-Clients sind die wichtigste Schnittstelle zu E-Mail-Postfächern. Es handelt sich um komplexe Software, die mit den Benutzern interagiert.
Auf dem Markt gibt es zahlreiche Lösungen; wir haben sie anhand von zwei Kriterien ausgewählt:
Wir haben uns zwei Optionen überlegt:
 Mozilla Thunderbird ist ein plattformübergreifender E-Mail-Client mit offenem Quellcode für PCs. Entwickelt von der Mozilla Foundation.
Mozilla Thunderbird ist ein plattformübergreifender E-Mail-Client mit offenem Quellcode für PCs. Entwickelt von der Mozilla Foundation.
Es unterstützt sowohl IMAP als auch POP (wobei E-Mails lokal auf Ihrer Festplatte gespeichert werden, sodass Sie auch ohne Internetverbindung darauf zugreifen können).
Es bietet hervorragende Funktionen zur E-Mail-Filterung und -Verwaltung.
Thunderbird bietet umfassende Unterstützung für die Verwendung mehrerer Konten und Identitäten, einschließlich automatischer Signaturfunktionen.
Es enthält installationsfertige Versionen für: Windows, Mac OS und Linux. Um aus der Ferne Zugriff zu erhalten, müssen sich Benutzer zunächst mit ihrem Computer verbinden.
 Die neue Rainloop-Gabelist ein einfacher, moderner, schlanker und schneller webbasierter E-Mail-Client.
Die neue Rainloop-Gabelist ein einfacher, moderner, schlanker und schneller webbasierter E-Mail-Client.
Es kann eine große Anzahl von E-Mail-Konten verwalten, ohne dass eine Datenbankverbindung erforderlich ist.
Es unterstützt sowohl das SMTP- als auch das IMAP-Protokoll, sodass E-Mails problemlos gesendet und empfangen werden können.
Im Jahr 2020 hat die SnappyMail-GitHub-Projekt wurde veröffentlicht.
Es handelt sich um eine grundlegend überarbeitete und gesicherte Abspaltung der RainLoop Webmail Community Edition.
Hier ist die Demo des E-Mail-Clients SnappyMail. Wenn Sie die Admin-Oberfläche ausprobieren möchten, Kontaktieren Sie uns.
Warnung: Dies ist ein Thema mit erheblichen rechtlichen Auswirkungen.
Wenden Sie sich an qualifizierte Berater, um die geltenden Vorschriften und deren Anwendung zu prüfen.Die geschäftliche E-Mail-Adresse ist ein Arbeitsinstrument
, das eine beeindruckende Menge an geschäftsrelevanten Informationen enthält.
Die Unternehmen können mit der E-Mail-Adresse
– die ein geschäftliches Arbeitsinstrument ist – machen, was sie wollen, aber wird sie von den Mitarbeitern verfasst und gelesen?
Können sie sie lesen? Können sie sie sichern? Können sie sie archivieren?
Zusammenfassung:
Die geschäftliche E-Mail-Adresse hat einen zwiespältigen Charakter,
sie ist ein Werkzeug, das dem Arbeitgeber gehört, aber vom Arbeitnehmer genutzt wird.
Wir müssen zwischen zwei verschiedenen Arten von geschäftlichen E-Mail-Adressen unterscheiden:
Die allgemeinen Firmenpostfächer sind überhaupt kein Problem,
das Unternehmen überprüft sie, liest alle Nachrichten und unterliegt dabei keinerlei Einschränkungen.
Persönliche E-Mail-Postfächer wie name.surname@companyname.com,
können personenbezogene Daten des Arbeitnehmers enthalten, die der Arbeitgeber schützen muss.
Wenn wir uns für die Nutzung einer solchen Mailbox entscheiden,
müssen wir als Arbeitgeber wissen, welche technischen Standards wir einhalten müssen
und welche Tools wir einsetzen müssen, um die Daten angemessen verarbeiten zu können.
Die E-Mail-Adresse lässt sich mit einem Dienstwagen vergleichen,
sie wird dem Mitarbeiter zur Nutzung im Rahmen seiner beruflichen Aufgaben zur Verfügung gestellt.
Der Arbeitgeber kann beispielsweise den Kilometerstand überprüfen, um sicherzustellen, dass der Mitarbeiter
dieses Arbeitsmittel nicht missbraucht und für private Zwecke nutzt.
Der Arbeitgeber darf jedoch nicht systematisch und ohne konkreten Anlass
überwachen, was der Arbeitnehmer im Firmenwagen tut.
Die E-Mail-Adresse ist das Äquivalent zum Firmenwagen, ein Arbeitsmittel, das sich im Besitz des Unternehmens befindet,
und dem Mitarbeiter zur Verfügung gestellt wird, damit er es für die Arbeit nutzen und seine Aufgaben erfüllen kann.
Was der Mitarbeiter – auch während der Arbeitszeit – versendet und empfängt, ist vergleichbar mit dem, was
im Cockpit des Firmenwagens geschieht, und wird der privaten Korrespondenz gleichgestellt.
Das Unternehmen kann den Inhalt der E-Mail-Nachrichten nicht einsehen,
dies ist weder systematisch noch ohne konkreten Anlass möglich.
Selbst wenn ein konkreter Anlass vorliegt, ist dies nur unter bestimmten Voraussetzungen möglich.
Es stehen drei unterschiedliche Interessen auf dem Spiel, die gegeneinander abgewogen werden müssen:
Der Mitarbeiter muss in einer angemessenen schriftlichen Mitteilung darüber informiert werden, dass die E-Mail-Adresse
ausschließlich für alle Zwecke im Zusammenhang mit dem Arbeitsverhältnis genutzt werden darf, beispielsweise durch das Verbot der privaten Nutzung.
Das Dokument muss eine Anleitung zur Nutzung der Unternehmens-Tools enthalten,
einschließlich des E-Mail-Postfachs, und darauf hinweisen, dass gemäß den Datenschutzbestimmungen:
Die sogenannten „massiven Kontrollen“ sind verboten,
wie beispielsweise das systematische Durchsehen des Inhalts des E-Mail-Postfachs eines Mitarbeiters.
Die Grenzen der Arbeitgeberkontrolle beruhen auf drei Grundprinzipien:
Zum einen gilt der Grundsatz von Treu und Glauben, wonach der Arbeitgeber die Firmen-E-Mail-Postfächer seiner Mitarbeiter nur dann überprüfen darf
, wenn ein triftiger Grund vorliegt
, beispielsweise zum Schutz von Unternehmensvermögen, das durch einen Virus gefährdet oder geschädigt werden könnte;
oder im Falle des Verdachts auf Untreue seitens des Mitarbeiters, um vorbeugende Kontrollen durchzuführen
die anderen sind die Verhältnismäßigkeit bei der Kontrolle sowie die zeitliche und sachliche Begrenzung der Forschung
Die Vorschriften verlangen, dass der Arbeitgeber nachweisen muss
, dass er angemessene und wirksame Sicherheitsmaßnahmen getroffen hat
zum Schutz von Unternehmensdaten, wie beispielsweise die Archivierung von Unternehmens-E-Mails.
Zugriff auf Daten durch den Arbeitgeber
sofern dies ohne detaillierte Unternehmensangaben erfolgt:
stellt einen sehr schwerwiegenden Verstoß dar
im persönlichen Bereich des Mitarbeiters können sensible Daten zu finden sein,
zum Beispiel Informationen über politische, religiöse, sexuelle oder gewerkschaftliche Neigungen,
deren Vertraulichkeit auf höchstem Niveau gewährleistet sein muss
Es handelt sich um eine Straftat
Zudem besteht das Risiko, dass alle illegal erlangten Daten
in einem Gerichtsverfahren unbrauchbar sind
Geschäftskorrespondenz sollte in der Regel maximal zehn Jahre lang aufbewahrt werden.
Um das Unternehmensvermögen zu sichern und sich in etwaigen Rechtsstreitigkeiten verteidigen zu können.
Die Speicherung und Verarbeitung personenbezogener Daten ist nur für einen bestimmten Zweck zulässig.
Wenn dieser Zweck nach einer bestimmten Zeit, beispielsweise nach zehn Jahren, nicht mehr besteht, müssen diese Daten gelöscht werden.
Im Falle einer Kündigung oder eines Austritts eines Mitarbeiters muss die E-Mail-Adresse
(Vorname.Nachname) innerhalb kurzer Zeit deaktiviert werden.
Das Unternehmen kann eine automatische Antwort aktivieren, in der der Absender darüber informiert wird, dass das Konto deaktiviert wurde,
und er gebeten wird, an eine andere interne E-Mail-Adresse zu schreiben.
Das historische Archiv der Unternehmensnachrichten gekündigter Mitarbeiter
kann nur dann aufbewahrt werden, wenn der Mitarbeiter darüber informiert wurde, dass seine Nachrichten gespeichert wurden.
Wie schützt man geschäftliche E-Mails vor Spam?
Es ist fast unmöglich, über E-Mails nachzudenken, ohne dabei das Thema Spam zu berücksichtigen.
Wir haben versucht, die aktuelle Situation und die möglichen Strategien zusammenzufassen:
Eine seriöse Quelle ist SenderBase, das mittlerweile Talos heißt,
und etwa 85 % Spam-E-Mails sowie 15 % legitime E-Mails ausweist
im Vergleich zum im September 2020 erfassten E-Mail-Verkehr.
Dieser Prozentsatz ist stabil geblieben und hat sich in den letzten zwölf Monaten kaum verändert.
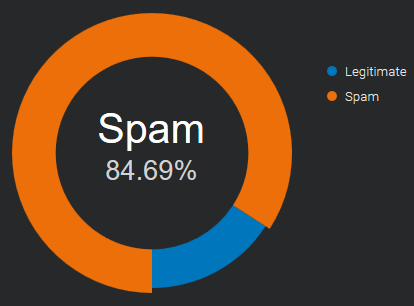
Quelle: E-Mail- und Spam-Daten – Weltweites Gesamtvolumen an E-Mails und Spam.
Manchmal dient Spam lediglich Werbezwecken, und der Absender
versucht lediglich, mehr Kunden für sein Unternehmen
zu gewinnen, was zu Ablenkung und Zeitverlust führt. Er kann Ihren Posteingang
so überfüllen, dass es schwierig wird, wichtige E-Mails zu finden.
Nicht alle Spam-Mails sind harmlose Werbe-E-Mails.
In vielen Fällen sind die Absichten böswillig und zielen darauf ab, die Systeme der Nutzer zu beschädigen oder zu kapern.
Zu den weltweit häufigsten Varianten bösartigen Spams zählen Trojaner, Spyware und Ransomware.
Stellen Sie sich die Posteingänge Ihres Unternehmens wie Ihre Haustür vor:
Sie müssen entscheiden, wen Sie hereinlassen und wen Sie draußen lassen.
Keine Methode bietet eine vollständige Lösung für das Spam-Problem.
Jede Methode bringt Kompromisse mit sich zwischen dem fälschlichen Zurückweisen legitimer E-Mails (Falsch-Positive)
und dem Nicht-Zurückweisen von Spam (Falsch-Negative)
sowie den damit verbundenen Kosten in Form von Zeit, Aufwand und Kosten für das ungerechtfertigte Blockieren legitimer E-Mails.
Anti-Spam-Maßnahmen lassen sich in zwei Bereiche unterteilen: Prävention und Bekämpfung.
Schränken Sie die Verfügbarkeit Ihrer E-Mail-Adressen ein, um das Risiko zu verringern, Spam zu erhalten.
Diskretion
Gib deine E-Mail-Adresse nicht an jeden weiter
Je weniger bekannt sie ist, desto weniger Spam wirst du erhalten
Verwende nach Möglichkeit für Online-Anmeldungen eine andere E-Mail-Adresse
Kontaktformulare
veröffentlichen Ihre E-Mail-Adresse nicht online
jeder kann sie sehen, „Spambots“ fangen sie ständig ab
um online kontaktiert zu werden, nutzen Sie sichere* Webformulare / Kontaktformulare
* = geschützt vor Bots, die sie automatisch ausfüllen
Sobald die Spammer Ihre E-Mail-Adresse haben, verlagert sich der Kampf auf Ihren Mailserver und Ihren Posteingang.
SpamAssassin-ähnliche Bewertungssysteme
Sie nutzen verschiedene Techniken zur Spam-Erkennung, darunter DNS-basierte E-Mail-Blacklists
(allgemein als Realtime Blacklist, DNSBL oder RBL bezeichnet), Textanalyse und Bayes'sche Filterung.
Jeder Test hat einen Bewertungswert. Die Bewertungen können positiv oder negativ sein, wobei positive Werte auf „Spam“ und negative auf „Ham“ (kein Spam) hinweisen.
Der Standard-Punkteschwellenwert für den Empfänger beträgt „5,0“. Liegt die Punktzahl einer E-Mail über diesem Schwellenwert, wird sie als Spam markiert.
Im Internet sind zahlreiche „SpamAssassin-Tests“ verfügbar,
mit denen Spammer ihre Nachrichten vor dem Versand überprüfen können.
Unterstützt durch Nutzer
Nutzer dieser Systeme können eingehende E-Mails als legitim oder als Spam kennzeichnen, und diese Markierungen werden in einer zentralen Datenbank gespeichert.
Sobald eine bestimmte Anzahl von Nutzern eine bestimmte E-Mail als Spam markiert hat, verhindert der Filter automatisch, dass sie in den Posteingängen der übrigen Community-Mitglieder landet.
Manchmal wird das Nutzer-Feedback mit automatisierten Kontrollen kombiniert, wie beispielsweise der Anzahl der Interaktionen mit dem Inhalt der Nachricht,
der Anzahl der Klicks auf Links und der heruntergeladenen Bilder oder der Häufigkeit, mit der dieselbe Nachricht in mehreren Postfächern auftaucht.
Wenn ein kollaboratives Inhaltsfiltersystem eine große, aktive Nutzerbasis umfasst,
kann es einen Spam-Ausbruch schnell blockieren, manchmal innerhalb weniger Minuten.
Diese Art von Filter lässt sich von Spammern kaum umgehen.
E-Mail-Authentifizierung
SPF, DKIM und DMARC sind Authentifizierungsverfahren, mit denen Sie feststellen können, ob die Absenderadresse tatsächlich von dem Absender stammt, der angegeben wird.
Im Jahr 2020 sind sie weit verbreitet und eine gute Quelle, um vertrauenswürdige Absender zu identifizieren.
Es ist wichtig, im Voraus die genaue Domain zu kennen, von der die E-Mails stammen,
da man sich sonst leicht durch die einfache Änderung eines Buchstabens täuschen lässt.
Es ist möglich, dass Spammer die E-Mail-Authentifizierung einhalten
, sodass ihre Nachrichten so aussehen, als kämen sie von „legitimen Absendern“.
Zugelassene Absender, Whitelist
In einer Whitelist kann man eine Reihe vertrauenswürdiger Adressen oder Domains angeben.
Zu Beginn sind das persönliche Adressbuch und die bisher empfangenen E-Mails eine große Hilfe.
Befindet sich ein Absender in dieser Liste, werden alle Prüfungen übersprungen und die Nachricht wird ohne Verzögerung empfangen.
Diese Methode ist einfach zu implementieren und in Verbindung mit der E-Mail-Authentifizierung sehr effektiv, um das Fälschen von E-Mail-Adressen* zu verhindern.
* = Verwendung eines gefälschten Absenders, um den Anschein zu erwecken, dass die Nachricht von einer anderen Person als dem tatsächlichen Absender stammt
Sobald Ihre Liste vertrauenswürdiger Kontakte vollständig ist, gelangt kein unbekannter Absender mehr in Ihren Posteingang.
Alle unerwünschten Nachrichten können in ein anderes Postfach umgeleitet werden, das einmal täglich oder seltener überprüft wird.
Spammer werden kaum herausfinden können, wer die vertrauenswürdigen Absender der einzelnen Empfänger sind.
Selbst wenn sie dies tun, werden Sie durch E-Mail-Authentifizierungsprüfungen auf die betrügerische Nutzung aufmerksam gemacht.
Wie funktioniert DMARC mit Gmail und Office 365? (aktualisiert)
Wir haben erneut untersucht, wie sich die E-Mail-Authentifizierung auf die Zustellungs
an Google Mail- und Office 365-Postfächer auswirkt – die beliebtesten E-Mail-Anbieter für Unternehmen.
Die Ergebnisse lassen sich in zwei Gruppen unterteilen:
(Wie sich SPF, DKIM und DMARC auf die Zustellung gesendeter Nachrichten auswirken)
# Google Mail: Die E-Mails werden immer angenommen, die SPF-Authentifizierung scheint überhaupt nicht berücksichtigt zu werden
Die DKIM-Signatur wird nur geprüft, wenn sie mit der Absender-E-Mail-Adresse übereinstimmt und DMARC mit der Richtlinie „quarantine“ oder „reject“ konfiguriert ist.
# Office 365: reagiert vollständig auf SPF; wenn eine Nachricht die SPF-Prüfung besteht, gelangt sie in den Posteingang.
Die DKIM-Signatur wird nur berücksichtigt, wenn sie mit der Absender-E-Mail-Adresse übereinstimmt, andernfalls spielt sie keine Rolle.
Hinweise: In der letzten Augustwoche zeigte Office 365 ein seltsames Verhalten:
Nur Nachrichten, die mit DKIM signiert waren (Signaturdomäne stimmte mit der Absenderadresse überein)
und bei denen ein DMARC-Eintrag vorhanden war (mit beliebiger Richtlinie), wurden in den Posteingang zugestellt
(Wie SPF, DKIM und DMARC die E-Mail-Adresse des Absenders vor Spoofing schützen*)
* = Die Nachricht so erscheinen lassen, als stamme sie von einer anderen Person als dem tatsächlichen Absender
# Google Mail: Bei Aktivierung von DMARC werden gefälschte Absender in den Spam-Ordner gefiltert (mit p=quarantine) oder abgelehnt (mit p=reject).
Es passiert nichts, wenn die Richtlinie auf „none“ (p=none) gesetzt ist; in diesem Fall gelangen alle Nachrichten in den Posteingang.
# Office 365: Die Ergebnisse „spf fail“ oder „spf softfail“ reichen aus, um die gefälschten Absender in den Junk-E-Mail-Ordner zu verschieben.
Die vorgeschlagenen Anforderungen an die E-Mail-Authentifizierung lassen sich wie folgt zusammenfassen:
| E-Mail-Zustellung | Schutz vor Spoofing | |
|---|---|---|
| Gmail | DKIM-Passwort (domänenbezogen) | dmarc mit p=quarantine oder p=reject |
| Office 365 | SPF-Pass und DKIM-Pass (domänengebunden) | SPF und DMARC aktiviert (für zusätzliche Sicherheit) |
Nachfolgend finden Sie die vollständige Liste der durchgeführten Tests
| Gmail | Gmail- (DMARC aktiviert) |
Office 365 | Office 365- (DMARC-Einrichtung) |
||
|---|---|---|---|---|---|
| SPF-Pass | dkim keine | Posteingang | Posteingang | Posteingang | Posteingang |
| SPF-Fehler | dkim keine | Posteingang | Spam | Müll | Müll |
| spf SoftFail | dkim keine | Posteingang | Spam | Müll | Müll |
| SPF: keine | dkim keine | Posteingang | Spam | Müll | Müll |
| SPF-Pass | DKI-Unterschied | Posteingang | Posteingang | Posteingang | Posteingang |
| SPF-Fehler | DKI-Unterschied | Posteingang | Spam | Müll | Müll |
| spf SoftFail | DKI-Unterschied | Posteingang | Spam | Müll | Müll |
| SPF: keine | DKI-Unterschied | Posteingang | Spam | Müll | Müll |
| SPF-Pass | DKI-Passwort | Posteingang | Posteingang | Posteingang | Posteingang |
| SPF-Fehler | DKI-Passwort | Posteingang | Posteingang | Posteingang | Posteingang |
| spf SoftFail | DKI-Passwort | Posteingang | Posteingang | Posteingang | Posteingang |
| SPF: keine | DKI-Passwort | Posteingang | Posteingang | Posteingang | Posteingang |
| SPF-Pass | DKIM ungültig | Posteingang | Posteingang | Posteingang | Posteingang |
| SPF-Fehler | DKIM ungültig | Posteingang | Spam | Müll | Müll |
| spf SoftFail | DKIM ungültig | Posteingang | Spam | Müll | Müll |
| SPF: keine | DKIM ungültig | Posteingang | Spam | Müll | Müll |
Anmerkungen:
Wie wirkt sich die DKIM-Domänenabgleichung auf die DMARC-Authentifizierung aus?
DMARC (Domain-based Message Authentication, Reporting and Conformance),
ist ein Standard zur E-Mail-Authentifizierung, der entwickelt wurde, um gefälschte E-Mails mit gefälschten Domänen zu bekämpfen.
Im Kapitel „3.1. Identifikatorabgleich“ heißt es:
E-Mail-Authentifizierungstechnologien authentifizieren verschiedene (und
unterschiedliche) Aspekte einer einzelnen Nachricht. Beispielsweise authentifiziert [DKIM]
die Domäne, die die Nachricht signiert hat,
während [SPF] entweder die Domäne authentifizieren kann, die im
RFC5321.MailFrom-Teil (Mail-From) von [SMTP] oder im RFC5321.EHLO/
HELO-Domäne oder beides. Dies können unterschiedliche Domänen sein, und sie sind
für den Endbenutzer in der Regel nicht sichtbar.
DMARC authentifiziert die Verwendung der RFC5322.From-Domäne, indem es verlangt, dass
diese mit einem authentifizierten Identifikator übereinstimmt (abgestimmt ist).
-- https://tools.ietf.org/html/rfc7489#section-3.1Das bedeutet ganz einfach:
Wenn ein Absender seine E-Mail mittels SPF und/oder DKIM authentifiziert,
muss mindestens eine der Domains mit der Absender-Domain übereinstimmenUns war nicht klar, ob eine Nachricht die SPF- oder DKIM-Prüfung
nicht bestehen und dennoch die DMARC-Authentifizierung bestehen könnte.
Wir haben es mit einem Tool getestet, das jedem zur Verfügung steht: einem Gmail-Postfach.
Um das Ergebnis zu sehen, öffnen Sie die Nachricht und wählen Sie „Original anzeigen“:
Test 1 – weitergeleitete Nachricht: SPF-Fehler, DKIM-Bestätigung (abgestimmt)
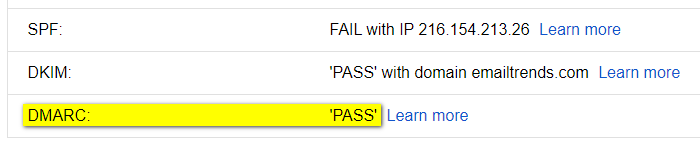
Test 2 – fehlerhafter DKIM-Schlüssel: DKIM-Fehler, SPF-Bestätigung (abgestimmt)
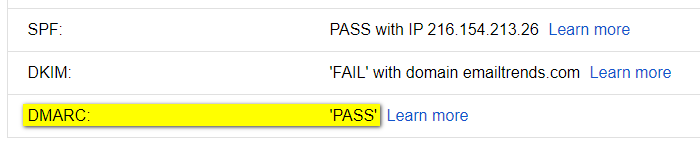
The result is evident, the message passes DMARC authentication if it occurs:
SPF and domain alignment <OR> DKIM and domain alignment
Um die DMARC-Prüfung zu bestehen, ist es daher in manchen Fällen wichtig, die DKIM-Signatur zu validieren:
Die signierende Domain (d=example.com) muss mit der „From“-Domain übereinstimmen.
Beispiele für „DMARC-PASS“-Ergebnisse, die andernfalls nicht funktioniert hätten:
Fall 1 – Durch die Weiterleitung wird die SPF-Authentifizierung unterbrochen
SPF-FEHLER: SPF-Authentifizierungsprüfungen schlagen meist fehl,
da eine neue Entität, die nicht im SPF-Eintrag des ursprünglichen Absenders aufgeführt ist, die weitergeleitete E-Mail versendet
DKIM-PASS (angepasst): Die Weiterleitung von E-Mails hat keinen Einfluss auf die DKIM-Signatur
Ergebnis: Dank der DKIM-Übereinstimmung besteht die Nachricht die DMARC-Prüfung.
Fall 2 – Die vom ESP (E-Mail-Dienstanbieter) bereitgestellte SPF-Domäne
kann NICHT mit der Absender-Domäne abgeglichen werden
SPF~PASS (nicht abgeglichen): Die SPF-Authentifizierung schlägt beim Abgleich der Domänen fehl,
da die von ESP in der „Mail-From“-Adresse verwendete Domäne von der im „From“-Feld angegebenen abweicht
DKIM-PASS (abgestimmt): Die DKIM-Signatur verwendet dieselbe Domain wie der Absender
Ergebnis: Dank der DKIM-Übereinstimmung besteht die Nachricht die DMARC-Prüfung.
Welche E-Mail-Anbieter sind 2020 am beliebtesten?
Um die Zustellbarkeit von E-Mails zu überwachen, ist es wichtig zu wissen, welche E-Mail-Anbieter Ihre Empfänger nutzen.
Für den B2B-Bereich liegen uns keine genauen Zahlen vor. Der Großteil der geschäftlichen E-Mail-Postfächer wird auf „Cloud-Office-Suiten“ umgestellt, wobei sich der Markt zwischen „G Suite“ und „Office 365“ aufteilt.
Zusammen decken sie laut Daten von datanyze.com mehr als 90 % des weltweiten Marktanteils für geschäftliche E-Mail-Dienste ab.
Diese Informationen für ein einzelnes Unternehmen zu sammeln, ist recht einfach.
Anhand des MX-Eintrags der Unternehmensdomain lässt sich der verwendete E-Mail-Anbieter erkennen:
aspmx.l.google.com für „G Suite“
mail.protection.outlook.com für „Office 365“
Wenn Ihr Unternehmen im B2B-Bereich tätig ist, empfiehlt es sich, regelmäßig die Postfächer dieser beiden Anbieter zu überprüfen.
Ein weiterer Anbieter ist Zoho (mx.zoho.com), dessen Marktanteil bei etwa 2 % liegt (Quelle: ciodive.com).
Im B2C-Bereich ist die Analyse komplexer. Es gibt keine öffentlich zugänglichen „E-Mail-Öffnungsdaten“, die auf dem Internetverkehr basieren.
Die einzige Möglichkeit, Informationen über E-Mail-Empfänger zu erhalten, besteht darin, diese aus unserer Kontaktliste zu extrahieren oder sie von großen E-Mail-Anbietern zu beziehen. Einige von ihnen erstellen Jahresberichte, um diese mit der Internet-Community zu teilen.
Die folgenden Daten zeigen die drei führenden E-Mail-Anbieter in 25 Ländern; die Informationen stammen aus der von Sendgrid veröffentlichten „2019 Email Benchmark and Engagement Study“.
Argentinien, Australien, Belgien, Brasilien, Kanada, Chile, China, Kolumbien, Dänemark, Frankreich, Deutschland, Indien, Indonesien, Italien, Japan, Mexiko, Neuseeland, Russland, Saudi-Arabien, Spanien, Südafrika, Schweden, Schweiz, Vereinigtes Königreich, Vereinigte Staaten
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| AR | gmail.com | 45.8% | hotmail.com | 33.7% | yahoo.com.ar | 8.2% | 87.7% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| AU | gmail.com | 38.0% | hotmail.com | 18.7% | bigpond.com | 5.4% | 62.1% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| SEIN | gmail.com | 30.6% | hotmail.com | 23.0% | telenet.be | 9.8% | 63.4% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| BR | gmail.com | 52.9% | hotmail.com | 22.5% | yahoo.com.br | 6.1% | 81.5% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| CA | gmail.com | 38.6% | hotmail.com | 18.8% | yahoo.com | 4.5% | 61.9% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| CL | gmail.com | 67.3% | hotmail.com | 18.2% | yahoo.es | 1.7% | 87.2% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| CN | NetEase (126.com, 163.com) | k. A. | Tencent (qq.com) | k. A. | Sina (sina.com) | k. A. | k. A. |
Hinweis: Die Informationen stammen aus „Länderübersicht: China“ von ReturnPath
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| CO | gmail.com | 41.3% | hotmail.com | 38.7% | yahoo.com | 4.3% | 84.3% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| DK | gmail.com | 35.8% | hotmail.com | 14.0% | live.dk | 3.7% | 53.5% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| FR | gmail.com | 36.0% | hotmail.fr | 9.8% | orange.fr | 8.2% | 54.0% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| DE | gmail.com | 20.8% | gmx.de | 10.0% | web.de | 9.5% | 40.3% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| IN | gmail.com | 82.4% | yahoo.com | 3.4% | yahoo.co.in | 1.6% | 87.4% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| ID | gmail.com | 82.6% | yahoo.com | 7.1% | yahoo.co.id | 1.0% | 90.7% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| IT | gmail.com | 46.8% | libero.it | 9.9% | hotmail.it | 7.2% | 63.9% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| JP | gmail.com | 33.8% | yahoo.co.jp | 12.7% | docomo.ne.jp | 8.6% | 55.1% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| MX | gmail.com | 42.6% | hotmail.com | 31.5% | yahoo.com.mx | 4.0% | 78.1% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| NL | gmail.com | 35.4% | hotmail.com | 19.5% | live.nl | 2.5% | 57.4% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| NZ | gmail.com | 46.3% | hotmail.com | 10.9% | xtra.co.nz | 9.0% | 66.2% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| RU | mail.ru | 34.8% | gmail.com | 22.7% | yandex.ru | 19.6% | 77.1% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| SA | gmail.com | 47.0% | hotmail.com | 31.0% | yahoo.com | 7.8% | 85.8% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| ES | gmail.com | 50.2% | hotmail.com | 25.8% | yahoo.es | 3.8% | 79.8% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| ZA | gmail.com | 65.5% | yahoo.com | 4.1% | hotmail.com | 2.9% | 72.5% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| SE | gmail.com | 33.2% | hotmail.com | 21.0% | live.se | 3.0% | 57.2% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| CH | gmail.com | 25.5% | bluewin.ch | 14.6% | hotmail.com | 10.5% | 50.6% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| Großbritannien | gmail.com | 30.8% | hotmail.com | 10.4% | hotmail.co.uk | 9.2% | 50.4% |
| ISO | Anbieter Nr. 1 | % | Anbieter Nr. 2 | % | Anbieter Nr. 3 | % | Insgesamt | |
|---|---|---|---|---|---|---|---|---|
| USA | gmail.com | 41.9% | yahoo.com | 15.1% | hotmail.com | 5.3% | 62.3% |
Wie funktioniert DMARC im Jahr 2020 mit Gmail und Office 365?
Wir haben untersucht, wie sich die E-Mail-Authentifizierung auf die Zustellungs
bei Google Mail und Office 365 auswirkt – den beliebtesten Anbietern von geschäftlichen E-Mail-Diensten.
Die Ergebnisse lassen sich in zwei Gruppen unterteilen:
E-Mail-Zustellung
(Wie sich SPF, DKIM und DMARC auf die Zustellung gesendeter Nachrichten auswirken)
Google Mail: Die E-Mails werden immer angenommen, die Authentifizierung scheint überhaupt keine Rolle zu spielen
Office 365: Reagiert im Allgemeinen auf SPF und DKIM. Der einzige Weg, um konsistente Ergebnisse zu erzielen und den Posteingang zu erreichen, besteht darin, diese mit DMARC zu verknüpfen
Schutz vor E-Mail-Spoofing
(Wie SPF, DKIM und DMARC die E-Mail-Adresse des Absenders vor Spoofing schützen*)
* = lässt die Nachricht so erscheinen, als stamme sie von einer anderen Person als dem tatsächlichen Absender
Google Mail: Durch die Kombination von DMARC und SPF (Fail- oder Softfail-Qualifier) werden gefälschte Absender in den Spam-Ordner gefiltert oder abgelehnt (abhängig von Ihren DMARC-Einstellungen)
Office 365: SPF (Fail- oder Softfail-Qualifier) reicht aus, um gefälschte Absender in den Junk-E-Mail-Ordner zu leiten
Sie lassen sich wie folgt zusammenfassen:
| E-Mail-Zustellung | Schutz vor Spoofing | |
|---|---|---|
| Gmail | wird immer akzeptiert, die Authentifizierung wird überhaupt nicht berücksichtigt | DMARC + SPF (FehleroderSoftfail) |
| Office 365 | DMARC + SPF bestanden oder DMARC + DKIM bestanden | spf (FehleroderSoftfail) |
Nachfolgend finden Sie eine vollständige Übersicht über die durchgeführten Tests.
| Gmail | Office 365 | |
|---|---|---|
| spf Pass – dkim none | Posteingang | Posteingang |
| SPF-Fehler – DKIM nicht vorhanden | Posteingang | Müll |
| spf SoftFail – dkim none | Posteingang | Müll |
| spf Neutral – dkim none | Posteingang | Posteingang |
| SPF: keine – DKIM: keine | Posteingang | Müll |
| SPF-Passwort – DKIM-Passwort | Posteingang | Müll* |
| SPF-Fehler – DKIM bestanden | Posteingang | Müll |
| spf SoftFail – DKIM bestanden | Posteingang | Müll* |
| spf Neutral – dkim pass | Posteingang | Müll* |
| SPF: keine – DKIM: bestanden | Posteingang | Müll* |
| SPF-Pass – DKIM ungültig | Posteingang | Müll |
| SPF-Fehler – DKIM ungültig | Posteingang | Müll |
| spf SoftFail – DKIM ungültig | Posteingang | Müll |
| spf Neutral – dkim ungültig | Posteingang | Müll |
| SPF fehlt – DKIM ungültig | Posteingang | Müll |
| SPF-Pass – DKIM ungültig – DMARC abgelehnt | Posteingang | Posteingang |
| SPF-Fehler – DKIM ungültig – DMARC-Ablehnung | dsn=5.0.0, stat=Dienst nicht verfügbar | Müll |
| spf SoftFail – DKIM ungültig – DMARC abgelehnt | dsn=5.0.0, stat=Dienst nicht verfügbar | Müll |
| spf Neutral – dkim ungültig – dmarc abgelehnt | Posteingang | Posteingang |
| SPF fehlt – DKIM ungültig – DMARC abgelehnt | dsn=5.0.0, stat=Dienst nicht verfügbar | Müll |
| spf-Pass – dkim-Pass – dmarc-Ablehnung | Posteingang | Posteingang |
| SPF abgelehnt – DKIM akzeptiert – DMARC abgelehnt | Posteingang | Posteingang |
| spf SoftFail – dkim bestanden – dmarc abgelehnt | Posteingang | Posteingang |
| spf Neutral – dkim akzeptiert – dmarc abgelehnt | Posteingang | Posteingang |
| SPF: keine – DKIM: bestanden – DMARC: abgelehnt | Posteingang | Posteingang |
| spf: Bestanden – dkim: Abweichung – dmarc: Abgelehnt | Posteingang | Posteingang |
| SPF-Fehler – DKIM-Abweichung – DMARC-Ablehnung | dsn=5.0.0, stat=Dienst nicht verfügbar | Müll |
| spf SoftFail – DKIM-Abweichung – DMARC-Ablehnung | dsn=5.0.0, stat=Dienst nicht verfügbar | Müll |
| spf Neutral – dkim diff – dmarc reject | Posteingang | Posteingang |
| SPF: keine – DKIM: nicht übereinstimmend – DMARC: abgelehnt | dsn=5.0.0, stat=Dienst nicht verfügbar | Müll |
Anmerkungen: